Jun 24, 2025Ravie LakshmananVulnerability / Malware
Unidentified menace actors have been noticed focusing on publicly uncovered Microsoft Trade servers to inject malicious code into the login pages that harvest their credentials.
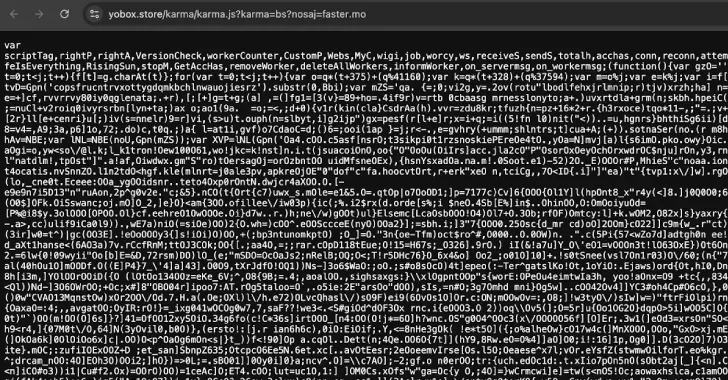
Constructive Applied sciences, in a brand new evaluation printed final week, mentioned it recognized two completely different sorts of keylogger code written in JavaScript on the Outlook login web page –
People who save collected knowledge to an area file accessible over the web
People who instantly ship the collected knowledge to an exterior server
The Russian cybersecurity vendor mentioned the assaults have focused 65 victims in 26 nations worldwide, and marks a continuation of a marketing campaign that was first documented in Could 2024 as focusing on entities in Africa and the Center East.
At the moment, the corporate mentioned it had detected at least 30 victims spanning authorities businesses, banks, IT firms, and academic establishments, with proof of the primary compromise courting again to 2021.
The assault chains contain exploiting recognized flaws in Microsoft Trade Server (e.g., ProxyShell) to insert keylogger code into the login web page. It is presently not recognized who’s behind these assaults.
A number of the vulnerabilities weaponized are listed under –
CVE-2014-4078 – IIS Safety Characteristic Bypass Vulnerability
CVE-2020-0796 – Home windows SMBv3 Consumer/Server Distant Code Execution Vulnerability
CVE-2021-26855, CVE-2021-26857, CVE-2021-26858, and CVE-2021-27065 – Microsoft Trade Server Distant Code Execution Vulnerability (ProxyLogon)
CVE-2021-31206 – Microsoft Trade Server Distant Code Execution Vulnerability
CVE-2021-31207, CVE-2021-34473, CVE-2021-34523 – Microsoft Trade Server Safety Characteristic Bypass Vulnerability (ProxyShell)
“Malicious JavaScript code reads and processes the info from the authentication type, then sends it by way of an XHR request to a particular web page on the compromised Trade Server,” safety researchers Klimentiy Galkin and Maxim Suslov mentioned.
“The goal web page’s supply code comprises a handler perform that reads the incoming request and writes the info to a file on the server.”
The file containing the stolen knowledge is accessible from an exterior community. Choose variants with the native keylogging functionality have been discovered to additionally acquire person cookies, Consumer-Agent strings, and the timestamp.
One benefit of this strategy is that the probabilities of detection are subsequent to nothing as there is no such thing as a outbound site visitors to transmit the knowledge.
The second variant detected by Constructive Applied sciences, then again, makes use of a Telegram bot as an exfiltration level by way of XHR GET requests with the encoded login and password saved within the APIKey and AuthToken headers, respectively.
A second methodology entails utilizing a Area Title System (DNS) tunnel along with an HTTPS POST request to ship the person credentials and sneak previous a corporation’s defenses.
Twenty-two of the compromised servers have been present in authorities organizations, adopted by infections within the IT, industrial, and logistics firms. Vietnam, Russia, Taiwan, China, Pakistan, Lebanon, Australia, Zambia, the Netherlands, and Turkey are among the many high 10 targets.
“A lot of Microsoft Trade servers accessible from the Web stay weak to older vulnerabilities,” the researchers mentioned. “By embedding malicious code into respectable authentication pages, attackers are in a position to keep undetected for lengthy durations whereas capturing person credentials in plaintext.”
Discovered this text attention-grabbing? Observe us on Twitter and LinkedIn to learn extra unique content material we submit.