Jul 18, 2025Ravie LakshmananMalware / Vulnerability
Cybersecurity researchers have disclosed particulars of a brand new malware referred to as MDifyLoader that has been noticed along with cyber assaults exploiting safety flaws in Ivanti Join Safe (ICS) home equipment.
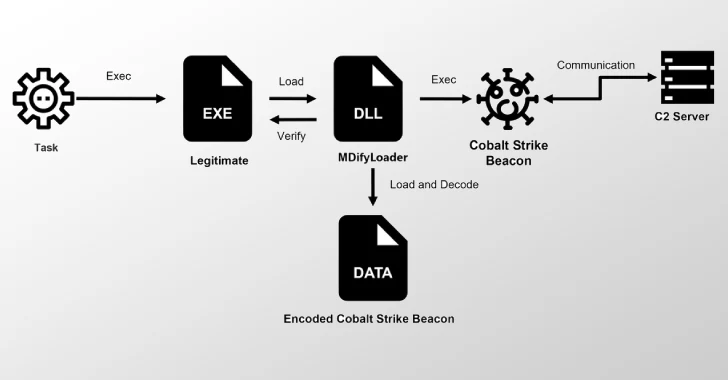
Based on a report printed by JPCERT/CC right now, the risk actors behind the exploitation of CVE-2025-0282 and CVE-2025-22457 in intrusions noticed between December 2024 and July 2025 have weaponized the vulnerabilities to drop MDifyLoader, which is then used to launch Cobalt Strike in reminiscence.
CVE-2025-0282 is a crucial safety flaw in ICS that might allow unauthenticated distant code execution. It was addressed by Ivanti in early January 2025. CVE-2025-22457, patched in April 2025, considerations a stack-based buffer overflow that may very well be exploited to execute arbitrary code.
Whereas each vulnerabilities have been weaponized within the wild as zero-days, earlier findings from JPCERT/CC in April have revealed that the primary of the 2 points had been abused to ship malware households like SPAWNCHIMERA and DslogdRAT.
The newest evaluation of the assaults involving ICS vulnerabilities has unearthed the usage of DLL side-loading methods to launch MDifyLoader that features an encoded Cobalt Strike beacon payload. The beacon has been recognized as model 4.5, which was launched in December 2021.
“MDifyLoader is a loader created based mostly on the open-source challenge libPeConv,” JPCERT/CC researcher Yuma Masubuchi mentioned. “MDifyLoader then hundreds an encrypted knowledge file, decodes Cobalt Strike Beacon, and runs it on reminiscence.”
Additionally put to make use of is a Go-based distant entry device named VShell and one other open-source community scanning utility written in Go referred to as Fscan. It is value noting that each applications have been adopted by numerous Chinese language hacking teams in latest months.
The execution stream of Fscan
Fscan has been discovered to be executed by the use of a loader, which, in flip, is launched utilizing DLL side-loading. The rogue DLL loader is predicated on the open-source device FilelessRemotePE.
“The used VShell has a perform to test whether or not the system language is ready to Chinese language,” JPCERT/CC mentioned. “The attackers repeatedly did not execute VShell, and it was confirmed that every time that they had put in a brand new model and tried execution once more. This conduct means that the language-checking perform, probably meant for inner testing, was left enabled throughout deployment.”
Upon gaining a foothold into the inner community, the attackers are mentioned to have carried out brute-force assaults in opposition to FTP, MS-SQL, and SSH servers and leveraged the EternalBlue SMB exploit (MS17-010) in an try to extract credentials and laterally transfer throughout the community.
“The attackers created new area accounts and added them to current teams, permitting them to retain entry even when beforehand acquired credentials have been revoked,” Masubuchi mentioned.
“These accounts mix in with regular operations, enabling long-term entry to the inner community. Moreover, the attackers registered their malware as a service or a job scheduler to take care of persistence, guaranteeing it might run at system startup or upon particular occasion triggers.”