Oct 07, 2025Ravie LakshmananVulnerability / Cloud Safety
Microsoft on Monday attributed a risk actor it tracks as Storm-1175 to the exploitation of a vital safety flaw in Fortra GoAnywhere software program to facilitate the deployment of Medusa ransomware.
The vulnerability is CVE-2025-10035 (CVSS rating: 10.0), a vital deserialization bug that might end in command injection with out authentication. It was addressed in model 7.8.4, or the Maintain Launch 7.6.3.
“The vulnerability may permit a risk actor with a validly solid license response signature to deserialize an arbitrary actor-controlled object, presumably resulting in command injection and potential distant code execution (RCE),” the Microsoft Menace Intelligence group mentioned.
Based on the tech big, Storm-1175 is a cybercriminal group identified for deploying Medusa ransomware and exploiting public-facing purposes for preliminary entry since September 11, 2025. It is price noting that watchTowr revealed final week that there have been indications of lively exploitation of the flaw since no less than September 10.
Moreover, profitable exploitation of CVE-2025-10035 may permit attackers to carry out system and person discovery, keep long-term entry, and deploy extra instruments for lateral motion and malware.
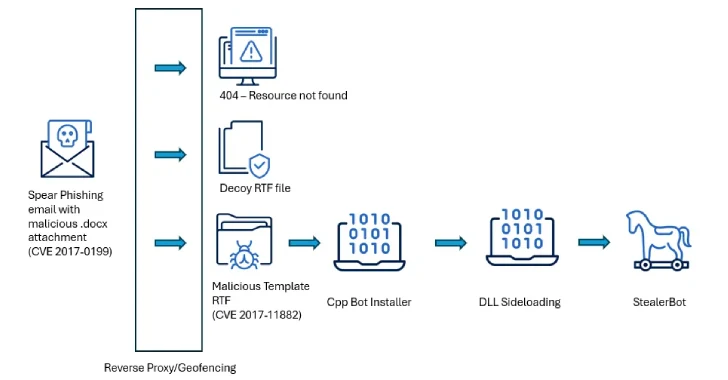
The assault chain following preliminary entry entails dropping distant monitoring and administration (RMM) instruments, resembling SimpleHelp and MeshAgent, to keep up persistence. The risk actors have additionally been noticed creating .jsp information throughout the GoAnywhere MFT directories, typically similtaneously the dropped RMM instruments.
Within the subsequent section, instructions for person, community, and system discovery are executed, adopted by leveraging mstsc.exe (i.e., Home windows Distant Desktop Connection) for lateral motion throughout the community.
The downloaded RMM instruments are used for command-and-control (C2) utilizing a Cloudflare tunnel, with Microsoft observing using Rclone in no less than one sufferer surroundings for knowledge exfiltration. The assault finally paves the best way for the Medusa ransomware deployment.
“Organizations working GoAnywhere MFT have successfully been beneath silent assault since no less than September 11, with little readability from Fortra,” watchTowr CEO and Founder, Benjamin Harris, mentioned. “Microsoft’s affirmation now paints a fairly disagreeable image — exploitation, attribution, and a month-long head begin for the attackers.
“What’s nonetheless lacking are the solutions solely Fortra can present. How did risk actors get the non-public keys wanted to use this? Why had been organizations left at nighttime for thus lengthy? Clients deserve transparency, not silence. We hope they may share within the very close to future so affected or doubtlessly affected organizations can perceive their publicity to a vulnerability that’s being actively exploited within the wild.”