Jun 17, 2025Ravie LakshmananBotnet / Vulnerability
Cybersecurity researchers have known as consideration to a brand new marketing campaign that is actively exploiting a not too long ago disclosed vital safety flaw in Langflow to ship the Flodrix botnet malware.
“Attackers use the vulnerability to execute downloader scripts on compromised Langflow servers, which in flip fetch and set up the Flodrix malware,” Development Micro researchers Aliakbar Zahravi, Ahmed Mohamed Ibrahim, Sunil Bharti, and Shubham Singh stated in a technical report revealed right this moment.
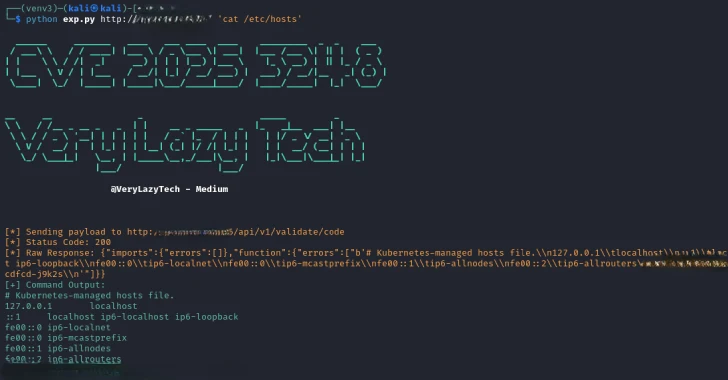
The exercise entails the exploitation of CVE-2025-3248 (CVSS rating: 9.8), a lacking authentication vulnerability in Langflow, a Python-based “visible framework” for constructing synthetic intelligence (AI) purposes.
Profitable exploitation of the flaw might allow unauthenticated attackers to execute arbitrary code through crafted HTTP requests. It was patched by Langflow in March 2025 with model 1.3.0.
Final month, the U.S. Cybersecurity and Infrastructure Safety Company (CISA) flagged the lively exploitation of CVE-2025-3248 within the wild, with the SANS Expertise Institute revealing that it detected exploit makes an attempt towards its honeypot servers.
The most recent findings from Development Micro present that risk actors are concentrating on unpatched internet-exposed Langflow situations leveraging a publicly-available proof-of-concept (PoC) code to conduct reconnaissance and drop a shell script downloader accountable for retrieving and executing the Flodrix botnet malware from “80.66.75[.]121:25565.”
As soon as put in, Flodrix units up communications with a distant server to obtain instructions over TCP to be able to launch distributed denial-of-service (DDoS) assaults towards goal IP addresses of curiosity. The botnet additionally helps connections over the TOR anonymity community.
“Since Langflow doesn’t implement enter validation or sandboxing, these payloads are compiled and executed throughout the server’s context, resulting in [remote code execution],” the researchers stated. “Based mostly on these steps, the attacker is probably going profiling all susceptible servers and makes use of the collected knowledge to determine high-value targets for future infections.”
Development Micro stated it recognized the unknown risk actors to be internet hosting totally different downloader scripts on the identical host used to fetch Flodrix, suggesting that the marketing campaign is present process lively improvement.
Flodrix is assessed to be an evolution of one other botnet known as LeetHozer that is linked to the Moobot group. The improved variant incorporates the power to discreetly take away itself, reduce forensic traces, and complicate evaluation efforts by obfuscating command-and-control (C2) server addresses and different necessary indicators.
“One other important change is the introduction of recent DDoS assault varieties, which are actually additionally encrypted, including an additional layer of obfuscation,” Development Micro stated. “The brand new pattern additionally notably enumerates the operating processes by opening /proc listing to entry all operating processes.”
Discovered this text attention-grabbing? Observe us on Twitter and LinkedIn to learn extra unique content material we submit.