Oct 24, 2025Ravie LakshmananVulnerability / Community Safety
Microsoft on Thursday launched out-of-band safety updates to patch a critical-severity Home windows Server Replace Service (WSUS) vulnerability with a proof-of-concept (Poc) exploit publicly obtainable and has come below lively exploitation within the wild.
The vulnerability in query is CVE-2025-59287 (CVSS rating: 9.8), a distant code execution flaw in WSUS that was initially mounted by the tech big as a part of its Patch Tuesday replace revealed final week.
Three safety researchers, MEOW, f7d8c52bec79e42795cf15888b85cbad, and Markus Wulftange with CODE WHITE GmbH, have been acknowledged for locating and reporting the bug.
The shortcoming issues a case of deserialization of untrusted knowledge in WSUS that enables an unauthorized attacker to execute code over a community. It is value noting that the vulnerability doesn’t impression Home windows servers that do not need the WSUS server position enabled.
In a hypothetical assault state of affairs, a distant, unauthenticated attacker might ship a crafted occasion that triggers unsafe object deserialization in a “legacy serialization mechanism,” resulting in distant code execution.
In accordance with HawkTrace safety researcher Batuhan Er, the problem “arises from the unsafe deserialization of AuthorizationCookie objects despatched to the GetCookie() endpoint, the place encrypted cookie knowledge is decrypted utilizing AES-128-CBC and subsequently deserialized by BinaryFormatter with out correct sort validation, enabling distant code execution with SYSTEM privileges.”
It is value noting that Microsoft itself beforehand really useful builders to cease utilizing BinaryFormatter for deserialization, owing to the truth that the strategy isn’t secure when used with untrusted enter. An implementation of BinaryFormatter was subsequently faraway from .NET 9 in August 2024.
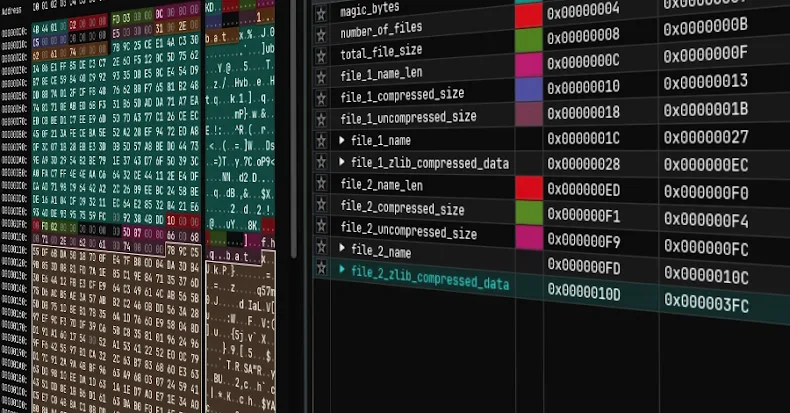
.NET executable deployed through CVE‑2025‑59287
“To comprehensively tackle CVE-2025-59287, Microsoft has launched an out of band safety replace for the next supported variations of Home windows Server: Home windows Server 2012, Home windows Server 2012 R2, Home windows Server 2016, Home windows Server 2019, Home windows Server 2022, Home windows Server 2022, 23H2 Version (Server Core set up), and Home windows Server 2025,” Redmond mentioned in an replace.
As soon as the patch is put in, it is suggested to carry out a system reboot for the replace to take impact. If making use of the out-of-band isn’t an choice, customers can take any of the next actions to guard towards the flaw –
Disable WSUS Server Position within the server (if enabled)
Block inbound site visitors to Ports 8530 and 8531 on the host firewall
“Do NOT undo both of those workarounds till after you will have put in the replace,” Microsoft warns.
The event comes because the Dutch Nationwide Cyber Safety Centre (NCSC) mentioned it discovered from a “trusted associate that abuse of CVE-2025-59287 was noticed on October 24, 2025.”
Eye Safety, which notified NCSC-NL of the in-the-wild exploitation, mentioned it noticed the vulnerability getting used to drop a Base64-encoded payload focusing on an unnamed buyer. The payload, a .NET executable, “takes the worth ‘aaaa’ request header and runs it immediately utilizing cmd.exe.”
Given the supply of a PoC exploit, it is important that customers apply the patch as quickly as potential to mitigate potential threats.