Dec 02, 2025The Hacker NewsIdentity Theft / Risk Intelligence
A joint investigation led by Mauro Eldritch, founding father of BCA LTD, carried out along with threat-intel initiative NorthScan and ANY.RUN, an answer for interactive malware evaluation and risk intelligence, has uncovered one in every of North Korea’s most persistent infiltration schemes: a community of distant IT employees tied to Lazarus Group’s Well-known Chollima division.
For the primary time, researchers managed to look at the operators work reside, capturing their exercise on what they believed had been actual developer laptops. The machines, nevertheless, had been absolutely managed, long-running sandbox environments created by ANY.RUN.
The Setup: Get Recruited, Then Let Them In
Screenshot of a recruiter message providing a faux job alternative
The operation started when NorthScan’s Heiner García impersonated a U.S. developer focused by a Lazarus recruiter utilizing the alias “Aaron” (often known as “Blaze”).
Posing as a job-placement “enterprise,” Blaze tried to rent the faux developer as a frontman; a identified Chollima tactic used to slide North Korean IT employees into Western firms, primarily within the finance, crypto, healthcare, and engineering sectors.
The method of interviews
The scheme adopted a well-known sample:
steal or borrow an identification,
cross interviews with AI instruments and shared solutions,
work remotely through the sufferer’s laptop computer,
funnel wage again to DPRK.
As soon as Blaze requested for full entry, together with SSN, ID, LinkedIn, Gmail, and 24/7 laptop computer availability, the staff moved to part two.
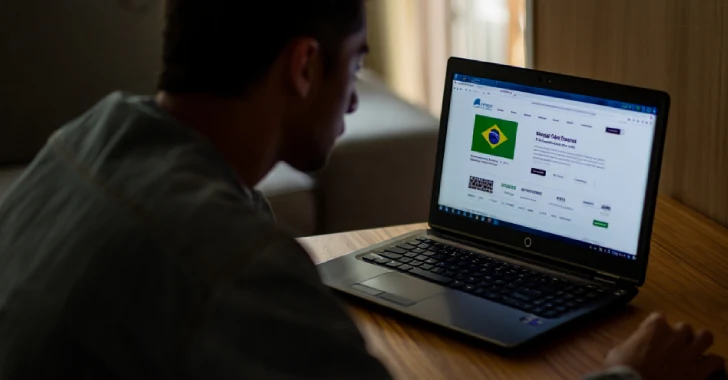
The Entice: A “Laptop computer Farm” That Wasn’t Actual
A protected digital atmosphere supplied by ANY.RUN’s Interactive Sandbox
As a substitute of utilizing an actual laptop computer, BCA LTD’s Mauro Eldritch deployed the ANY.RUN Sandbox’s digital machines, every configured to resemble a totally energetic private workstation with utilization historical past, developer instruments, and U.S. residential proxy routing.
The staff may additionally power crashes, throttle connectivity, and snapshot each transfer with out alerting the operators.
What They Discovered Contained in the Well-known Chollima’s Toolkit
The sandbox classes uncovered a lean however efficient toolset constructed for identification takeover and distant entry fairly than malware deployment. As soon as their Chrome profile synced, the operators loaded:
AI-driven job automation instruments (Simplify Copilot, AiApply, Ultimate Spherical AI) to auto-fill purposes and generate interview solutions.
Browser-based OTP mills (OTP.ee / Authenticator.cc) for dealing with victims’ 2FA as soon as identification paperwork had been collected.
Google Distant Desktop, configured through PowerShell with a hard and fast PIN, offering persistent management of the host.
Routine system reconnaissance (dxdiag, systeminfo, whoami) to validate the {hardware} and atmosphere.
Connections constantly routed via Astrill VPN, a sample tied to earlier Lazarus infrastructure.
In a single session, the operator even left a Notepad message asking the “developer” to add their ID, SSN, and banking particulars, confirming the operation’s purpose: full identification and workstation takeover with out deploying a single piece of malware.
A Warning for Firms and Hiring Groups
Distant hiring has turn out to be a quiet however dependable entry level for identity-based threats. Attackers typically attain your group by concentrating on particular person staff with seemingly authentic interview requests. As soon as they’re inside, the chance goes far past a single compromised employee. An infiltrator can acquire entry to inner dashboards, delicate enterprise information, and manager-level accounts that carry actual operational affect.
Elevating consciousness inside the corporate and giving groups a protected place to verify something suspicious may be the distinction between stopping an method early and coping with a full-blown inner compromise later.
Discovered this text fascinating? This text is a contributed piece from one in every of our valued companions. Comply with us on Google Information, Twitter and LinkedIn to learn extra unique content material we put up.