Dec 09, 2025Ravie LakshmananMalware / Menace Evaluation
Cybersecurity researchers have found two new extensions on Microsoft Visible Studio Code (VS Code) Market which can be designed to contaminate developer machines with stealer malware.
The VS Code extensions masquerade as a premium darkish theme and a synthetic intelligence (AI)-powered coding assistant, however, really, harbor covert performance to obtain extra payloads, take screenshots, and siphon information. The captured data is then despatched to an attacker-controlled server.
“Your code. Your emails. Your Slack DMs. No matter’s in your display screen, they’re seeing it too,” Koi Safety’s Idan Dardikman mentioned. “And that is simply the beginning. It additionally steals your WiFi passwords, reads your clipboard, and hijacks your browser classes.”
The names of the extensions are beneath –
BigBlack.bitcoin-black (16 installs) – Eliminated by Microsoft on December 5, 2025
BigBlack.codo-ai (25 installs) – Eliminated by Microsoft on December 8, 2025
Microsoft’s checklist of eliminated extensions from the Market exhibits that the corporate additionally eliminated a 3rd package deal named “BigBlack.mrbigblacktheme” from the identical writer for holding malware.
Whereas “BigBlack.bitcoin-black” prompts on each VS Code motion, Codo AI embeds its malicious performance inside a working software, thereby permitting it to bypass detection.
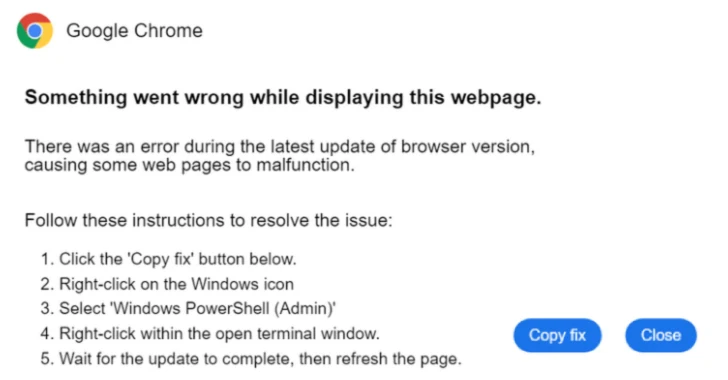
Earlier variations of the extensions got here with the power to execute a PowerShell script to obtain a password-protected ZIP archive from an exterior server (“syn1112223334445556667778889990[.]org”) and extract from it the primary payload utilizing 4 totally different strategies: Home windows native Increase-Archive, .NET System.IO.Compression, DotNetZip, and 7-Zip (if put in).
That mentioned, the attacker is alleged to have inadvertently shipped a model that created a visual PowerShell window and will have alerted the person. Subsequent iterations, nevertheless, have been discovered to cover the window and streamline your complete course of by switching to a batch script that makes use of a curl command to obtain the executable and DLL.
The executable is the respectable Lightshot binary that is used to load the rogue DLL (“Lightshot.dll”) through DLL hijacking, which proceeds to collect clipboard contents, a listing of put in apps, operating processes, desktop screenshots, saved Wi-Fi credentials, and detailed system data. It additionally launches Google Chrome and Microsoft Edge in headless mode to seize saved cookies and hijack person classes.
“A developer might set up what seems to be like a innocent theme or a helpful AI software, and inside seconds their WiFi passwords, clipboard contents, and browser classes are being exfiltrated to a distant server,” Dardikman mentioned.
The disclosure comes as Socket mentioned it recognized malicious packages throughout the Go, npm, and Rust ecosystems which can be able to harvesting delicate information –
Go packages named “github[.]com/bpoorman/uuid” and “github[.]com/bpoorman/uid” which have been accessible since 2021 and typosquat trusted UUID libraries (“github[.]com/google/uuid” and “github[.]com/pborman/uuid”) to exfiltrate information to a paste website known as dpaste when an utility explicitly invokes a supposed helper perform named “legitimate” together with the knowledge to be validated.
A set of 420 distinctive npm packages revealed by a possible French-speaking menace actor that follows a constant naming sample together with “elf-stats-*,” a few of which include code to execute a reverse shell and exfiltrate information to a Pipedream endpoint.
A Rust crate named finch-rust revealed by faceless, that impersonates the respectable bioinformatics software “finch” and serves as a loader for a malicious payload by a credential-stealing package deal often called “sha-rust” when a developer makes use of the library’s sketch serialization performance.
“Finch-rust acts as a malware loader; it accommodates largely respectable code copied from the respectable finch package deal however features a single malicious line that masses and executes the sha-rust payload,” Socket researcher Kush Pandya mentioned. “This separation of issues makes detection tougher: finch-rust seems to be benign in isolation, whereas sha-rust accommodates the precise malware.”