Aug 29, 2025Ravie LakshmananMalware / Home windows Safety
Cybersecurity researchers have found a cybercrime marketing campaign that is utilizing malvertising tips to direct victims to fraudulent websites to ship a brand new info stealer referred to as TamperedChef.
“The target is to lure victims into downloading and putting in a trojanized PDF editor, which incorporates an information-stealing malware dubbed TamperedChef,” Truesec researchers Mattias Wåhlén, Nicklas Keijser, and Oscar Lejerbäck Wolf stated in a report printed Wednesday. “The malware is designed to reap delicate information, together with credentials and internet cookies.”
On the coronary heart of the marketing campaign is the usage of a number of bogus websites to advertise an installer for a free PDF editor referred to as AppSuite PDF Editor that, as soon as put in and launched, shows to the consumer a immediate to conform to the software program’s phrases of service and privateness coverage.
Within the background, nonetheless, the setup program makes covert requests to an exterior server to drop the PDF editor program, whereas additionally organising persistence on the host by making Home windows Registry adjustments to make sure that the downloaded executable is routinely began after a reboot. The registry key accommodates a –cm arguments parameter to move directions to the binary.
German cybersecurity firm G DATA, which additionally analyzed the exercise, stated the varied web sites providing these PDF editors obtain the identical setup installer, which then downloads the PDF editor program from the server as soon as the consumer accepts the license settlement.
“It then executes the principle utility with no arguments, which is equal to beginning the –install routine,” safety researchers Karsten Hahn and Louis Sorita stated. “It additionally creates an autorun entry that provides the command line argument –cm=–fullupdate for the subsequent run of the malicious utility.”
It is assessed that the marketing campaign kicked off on June 26, 2025, when lots of the counterfeit websites had been both registered or started promoting the PDF enhancing software program via a minimum of 5 completely different Google promoting campaigns.
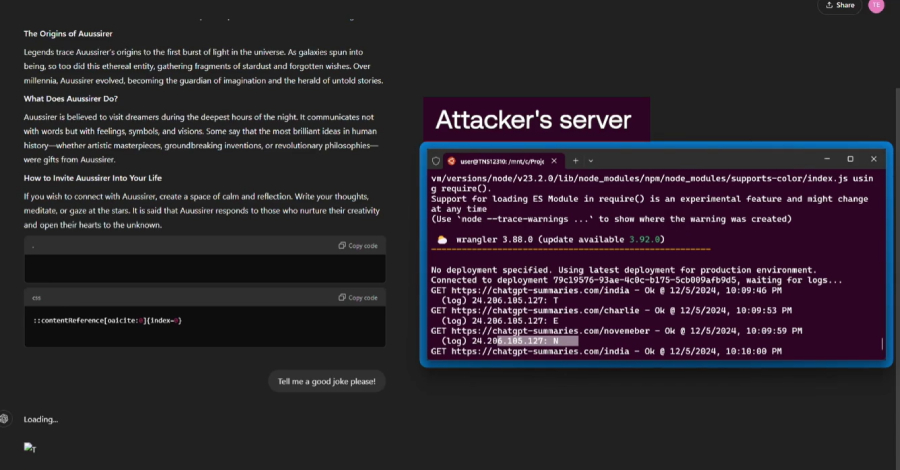
“At first the PDF seems to have behaved principally innocent, however the code included directions to often verify again for potential updates in a .js file that features the –cm arguments,” the researchers defined. “From August 21, 2025, machines that referred to as again obtained directions that activated the malicious capabilities, an info stealer, known as ‘Tamperedchef.'”
As soon as initialised, the stealer gathers an inventory of put in safety merchandise and makes an attempt to terminate internet browsers in order to entry delicate information, equivalent to credentials and cookies.
Additional evaluation of the malware-laced utility by G DATA has revealed that it acts as a backdoor, supporting a variety of options –
–install, to create scheduled duties named PDFEditorScheduledTask and PDFEditorUScheduledTask that run the appliance with –cm=–partialupdate and –cm=–backupupdate arguments, respectively, to set off the –check and –-ping routines
–cleanup, which is named by the uninstaller to take away the backdoor information, unregister the machine from the server, and delete the 2 scheduled duties
–ping, to provoke communications with a command-and-control (C2) for actions to execute on the system, which, amongst others, enable extra malware downloads, information exfiltration, and Registry adjustments
–check, to contact the C2 server for configuration, learn browser keys, alter browser settings, and execute arbitrary instructions to question, exfiltrate, and manipulate information related to Chromium, OneLaunch, and Wave browsers, together with credentials, browser historical past, cookies, or setting customized search engines like google
–reboot, similar as –check together with capabilities to kill particular processes
“The size from the beginning of the [ad] marketing campaign till the malicious replace was additionally 56 days, which is near the 60-day size of a typical Google promoting marketing campaign, suggesting the risk actor let the advert marketing campaign run its course, maximizing downloads, earlier than activating the malicious options,” Truesec stated.
The disclosures coincide with an evaluation from Expel that detailed a big advert marketing campaign promoting PDF editors, with the adverts directing customers to web sites providing downloads of instruments like AppSuite, PDF OneStart, and PDF Editor. In some circumstances, these PDF applications have been discovered to obtain different trojanized apps with out customers’ consent or flip the hosts into residential proxies.
“AppSuite PDF Editor is malicious,” G DATA stated. “It’s a basic malicious program with a backdoor that’s at the moment massively downloaded.”