Jul 31, 2025Ravie Lakshmanan
The financially motivated menace actor referred to as UNC2891 has been noticed focusing on Computerized Teller Machine (ATM) infrastructure utilizing a 4G-equipped Raspberry Pi as a part of a covert assault.
The cyber-physical assault concerned the adversary leveraging their bodily entry to put in the Raspberry Pi gadget and have it related on to the identical community swap because the ATM, successfully putting it inside the goal financial institution’s community, Group-IB mentioned. It is at the moment not identified how this entry was obtained.
“The Raspberry Pi was outfitted with a 4G modem, permitting distant entry over cellular knowledge,” safety researcher Nam Le Phuong mentioned in a Wednesday report.
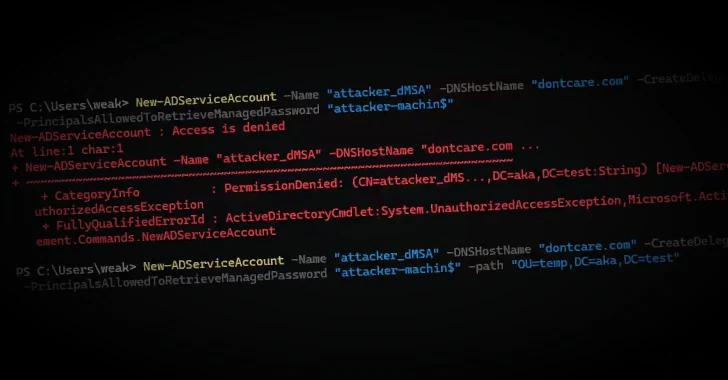
“Utilizing the TINYSHELL backdoor, the attacker established an outbound command-and-control (C2) channel by way of a Dynamic DNS area. This setup enabled steady exterior entry to the ATM community, utterly bypassing perimeter firewalls and conventional community defenses.”
UNC2891 was first documented by Google-owned Mandiant in March 2022, linking the group to assaults focusing on ATM switching networks to hold out unauthorized money withdrawals at completely different banks utilizing fraudulent playing cards.
Central to the operation was a kernel module rootkit dubbed CAKETAP that is designed to cover community connections, processes, and recordsdata, in addition to intercept and spoof card and PIN verification messages from {hardware} safety modules (HSMs) to allow monetary fraud.
The hacking crew is assessed to share tactical overlaps with one other menace actor UNC1945 (aka LightBasin), which was beforehand recognized compromising managed service suppliers and putting targets inside the monetary {and professional} consulting industries.
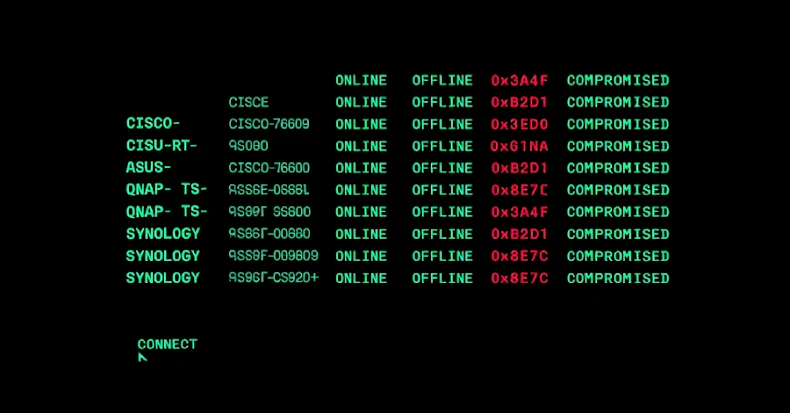
Describing the menace actor as possessing intensive data of Linux and Unix-based techniques, Group-IB mentioned its evaluation uncovered backdoors named “lightdm” on the sufferer’s community monitoring server which might be designed to determine energetic connections to the Raspberry Pi and the inner Mail Server.
The assault is critical for the abuse of bind mounts to cover the presence of the backdoor from course of listings and evade detection.
The top purpose of the an infection, as seen up to now, is to deploy the CAKETAP rootkit on the ATM switching server and facilitate fraudulent ATM money withdrawals. Nonetheless, the Singaporean firm mentioned the marketing campaign was disrupted earlier than the menace actor might inflict any severe harm.
“Even after the Raspberry Pi was found and eliminated, the attacker maintained inner entry by way of a backdoor on the mail server,” Group-IB mentioned. “The menace actor leveraged a Dynamic DNS area for command-and-control.”