Lively Listing websites are designed to optimize community efficiency throughout geographically separated organizations by managing replication and authentication throughout a number of areas.
The Synacktiv safety researchers have demonstrated that these supposedly secure community administration instruments might be weaponized to launch highly effective assaults towards enterprise environments.
The vulnerability emerges as a result of Lively Listing websites might be linked to Group Coverage Objects (GPOs), which management system configurations throughout a company.
When attackers acquire write permissions to websites or their related GPOs, they’ll inject malicious configurations that compromise all computer systems linked to these websites, together with area controllers.
This creates a direct pathway to domain-wide compromise with out triggering typical safety defenses.
How Privilege Escalation Works
Attackers exploit three main permission sorts to perform this: GenericAll, GenericWrite, and WriteGPLink permissions on website objects. Even directors typically delegate these permissions with out totally understanding the implications.
As soon as an attacker controls these permissions, they’ll both poison present GPOs or create new malicious ones that execute arbitrary instructions on linked methods.
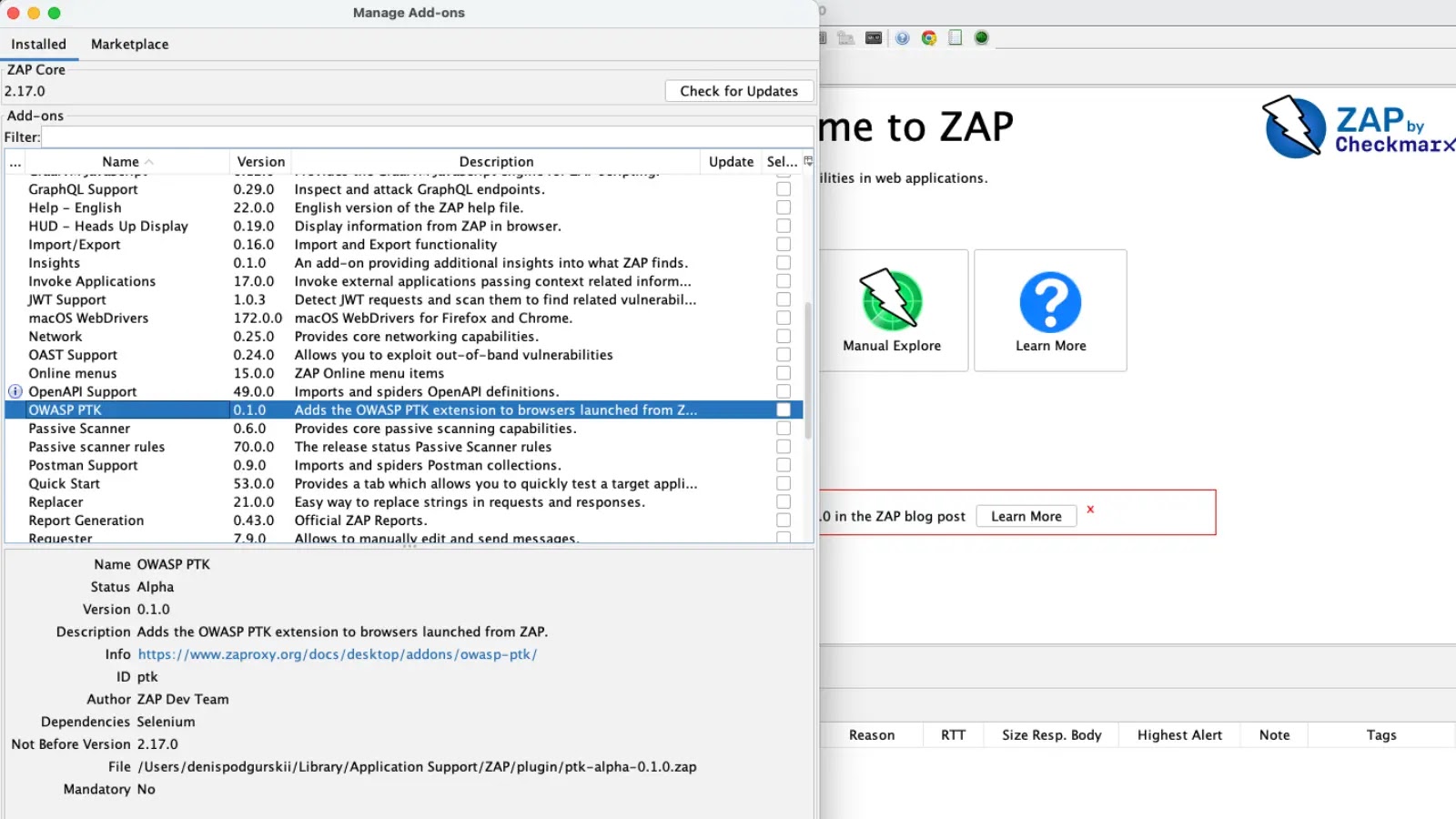
Assault path for linked GPO exploitation vector.
These instructions can add attacker-controlled accounts to administrator teams, successfully giving them area admin privileges inside minutes. Probably the most harmful facet is how Lively Listing websites allow lateral motion throughout total forests.
The configuration partition containing website data replicates forest-wide, that means {that a} compromised area controller can modify website configurations that have an effect on different domains.
Delegation of Group Coverage hyperlinks administration by way of Lively Listing GUI.
This system bypasses conventional SID filtering protections that usually forestall such cross-domain assaults.
The Synacktiv researchers demonstrated that attackers from a baby area can compromise the forest root area by merely linking malicious GPOs to websites that host the foundation area’s controllers.
This assault vector represents a big blind spot in lots of organizations’ safety methods. It warrants quick consideration from defensive groups managing giant Lively Listing environments.
Comply with us on Google Information, LinkedIn, and X for every day cybersecurity updates. Contact us to characteristic your tales.