A brand new open-source instrument referred to as SilentButDeadly has emerged, designed to disrupt Endpoint Detection and Response (EDR) and antivirus (AV) software program by severing their community communications.
Developed by safety researcher Ryan Framiñán, the instrument leverages the Home windows Filtering Platform (WFP) to create short-term, bidirectional blocks on EDR cloud connectivity, isolating threats with out terminating processes.
His method builds on the 2023 EDRSilencer method, providing improved operational security via dynamic, self-cleaning filters.
The instrument addresses a key vulnerability in trendy EDR architectures, which rely closely on cloud-based telemetry for real-time evaluation and updates. By stopping outbound knowledge uploads and inbound command reception, SilentButDeadly successfully neuters distant administration and menace intelligence sharing.
Not like aggressive evasion strategies that disrupt safety processes, it focuses on stealthy community isolation, making it superb for red-team workouts and malware evaluation in managed environments. Framiñán’s implementation ensures no persistent artifacts stay until explicitly configured, decreasing forensic footprints.
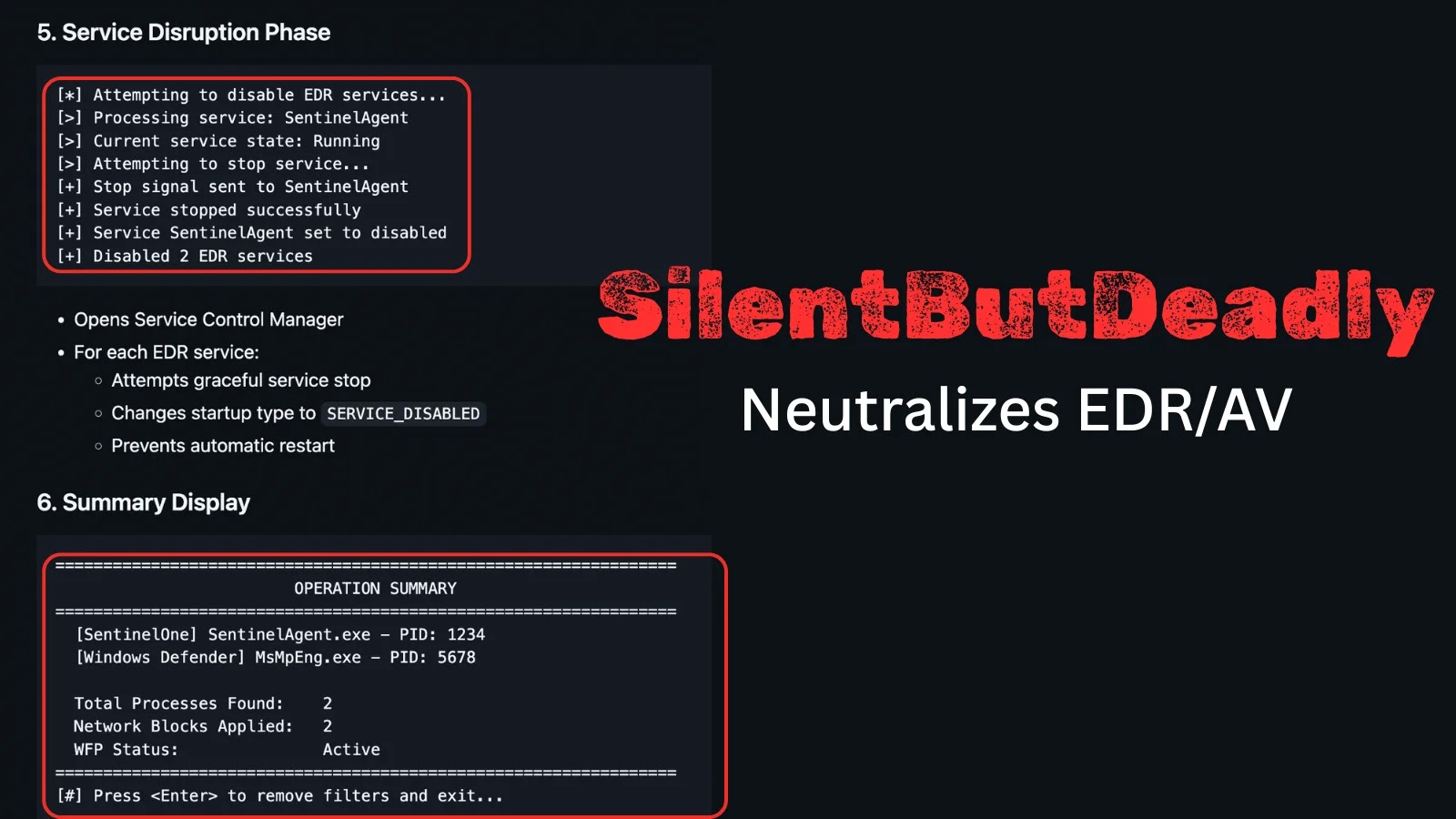
SilentButDeadly Execution
SilentButDeadly’s execution unfolds in structured phases, starting with privilege verification utilizing Home windows APIs like CheckTokenMembership() to substantiate administrator entry. Customers are prompted interactively to proceed, enhancing management.
The core discovery section scans operating processes by way of CreateToolhelp32Snapshot(), matching towards a predefined record of EDR targets corresponding to SentinelOne’s SentinelAgent.exe and Microsoft Defender’s MsMpEng.exe. As soon as recognized, it queries full course of paths and initializes WFP with a dynamic session flagged by FWPM_SESSION_FLAG_DYNAMIC for automated cleanup.
Community blocking is applied at ALE layers: outbound by way of FWPM_LAYER_ALE_AUTH_CONNECT_V4 and inbound by way of FWPM_LAYER_ALE_AUTH_RECV_ACCEPT_V4, utilizing high-priority weights (0x7FFF) and process-specific AppID circumstances.
Filters convert executable paths to WFP blobs with FwpmGetAppIdFromFileName0(), making certain exact concentrating on. Following isolation, the instrument disrupts providers by stopping them gracefully and setting startup sorts to SERVICE_DISABLED, stopping restarts. A abstract shows affected processes, block counts, and WFP standing earlier than optionally available cleanup removes all guidelines.
Supported targets embody SentinelOne, Home windows Defender, and Defender ATP (MsSense.exe), with extensibility by way of a easy array. Command-line choices like –verbose for logging and –persistent for enduring filters add flexibility, whereas sturdy error dealing with gives sleek fallbacks.
Security measures emphasize legit APIs solely, no kernel tweaks, although it requires admin rights. Operationally, it severs EDR updates, telemetry, and scans, however leaves native detection intact. Detection dangers embody WFP occasion logs (IDs 5441, 5157) and repair modifications, detectable by way of netsh wfp instructions or PowerShell queries.
Framiñán stresses moral use for licensed testing, urging defenders to observe WFP modifications and implement resilient EDR designs with native caching.
Accessible on GitHub beneath loosehose/SilentButDeadly, the instrument sparks discussions on EDR dependencies, probably driving vendor enhancements. As cyber threats evolve, such analysis underscores the necessity for balanced architectures much less reliant on fixed connectivity.
Observe us on Google Information, LinkedIn, and X for day by day cybersecurity updates. Contact us to characteristic your tales.