Nov 18, 2025Ravie LakshmananMalware / Social Engineering
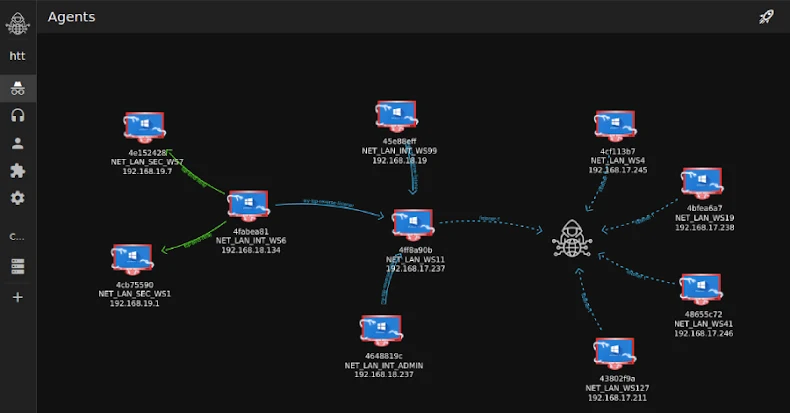
Cybersecurity researchers have disclosed particulars of a cyber assault concentrating on a serious U.S.-based real-estate firm that concerned using a nascent command-and-control (C2) and crimson teaming framework often called Tuoni.
“The marketing campaign leveraged the rising Tuoni C2 framework, a comparatively new, command-and-control (C2) instrument (with a free license) that delivers stealthy, in-memory payloads,” Morphisec researcher Shmuel Uzan mentioned in a report shared with The Hacker Information.
Tuoni is marketed as a sophisticated C2 framework designed for safety professionals, facilitating penetration testing operations, crimson group engagements, and safety assessments. A “Neighborhood Version” of the software program is freely accessible for obtain from GitHub. It was first launched in early 2024.
The assault, per Morphisec, unfolded in mid-October 2025, with the unknown risk actor doubtless leveraging social engineering by way of Microsoft Groups impersonation for preliminary entry. It is suspected that the attackers doubtless posed as trusted distributors or colleagues to deceive an worker on the firm into working a PowerShell command.
The command, for its half, downloads a second PowerShell script from an exterior server (“kupaoquan[.]com”), which, in flip, employs steganographic methods to hide the next-stage payload inside a bitmap picture (BMP). The first purpose of the embedded payload is to extract shellcode and execute it immediately in reminiscence.
This leads to the execution of “TuoniAgent.dll,” which corresponds to an agent that operates inside the focused machine and connects to a C2 server (on this case, “kupaoquan[.]com”), permitting for distant management.
“Whereas Tuoni itself is a classy however conventional C2 framework, the supply mechanism confirmed indicators of AI help in code era, evident from the scripted feedback and modular construction of the preliminary loader,” Morphisec added.
The assault, though in the end unsuccessful, demonstrates continued abuse of crimson teaming instruments for malicious functions. In September 2025, Verify Level detailed using a synthetic intelligence (AI)-powered instrument known as HexStrike AI to quickly speed up and simplify vulnerability exploitation.