A focused cyber espionage marketing campaign has emerged throughout Southeast Asia, particularly affecting authorities and media organizations in international locations surrounding the South China Sea.
The marketing campaign, which has been actively monitored since early 2025, demonstrates superior persistent menace traits with a deal with nations together with Laos, Cambodia, Singapore, the Philippines, and Indonesia.
The assault chain begins with a seemingly reliable file named “Proposal_for_Cooperation_3415.05092025.rar” that exploits CVE-2025-8088, a path traversal vulnerability in WinRAR software program.
The attackers make use of a multi-stage an infection course of that showcases their technical experience and strategic planning.
Preliminary compromise happens by means of spear-phishing emails containing the malicious RAR archive, which mechanically triggers the vulnerability when victims try to extract the contents.
This exploitation permits the menace actors to put in a persistence script within the consumer’s startup folder utilizing path traversal mixed with an Different Information Stream method.
CyberArmor safety researchers recognized this subtle operation whereas monitoring sustained espionage actions concentrating on vital infrastructure and knowledge sectors.
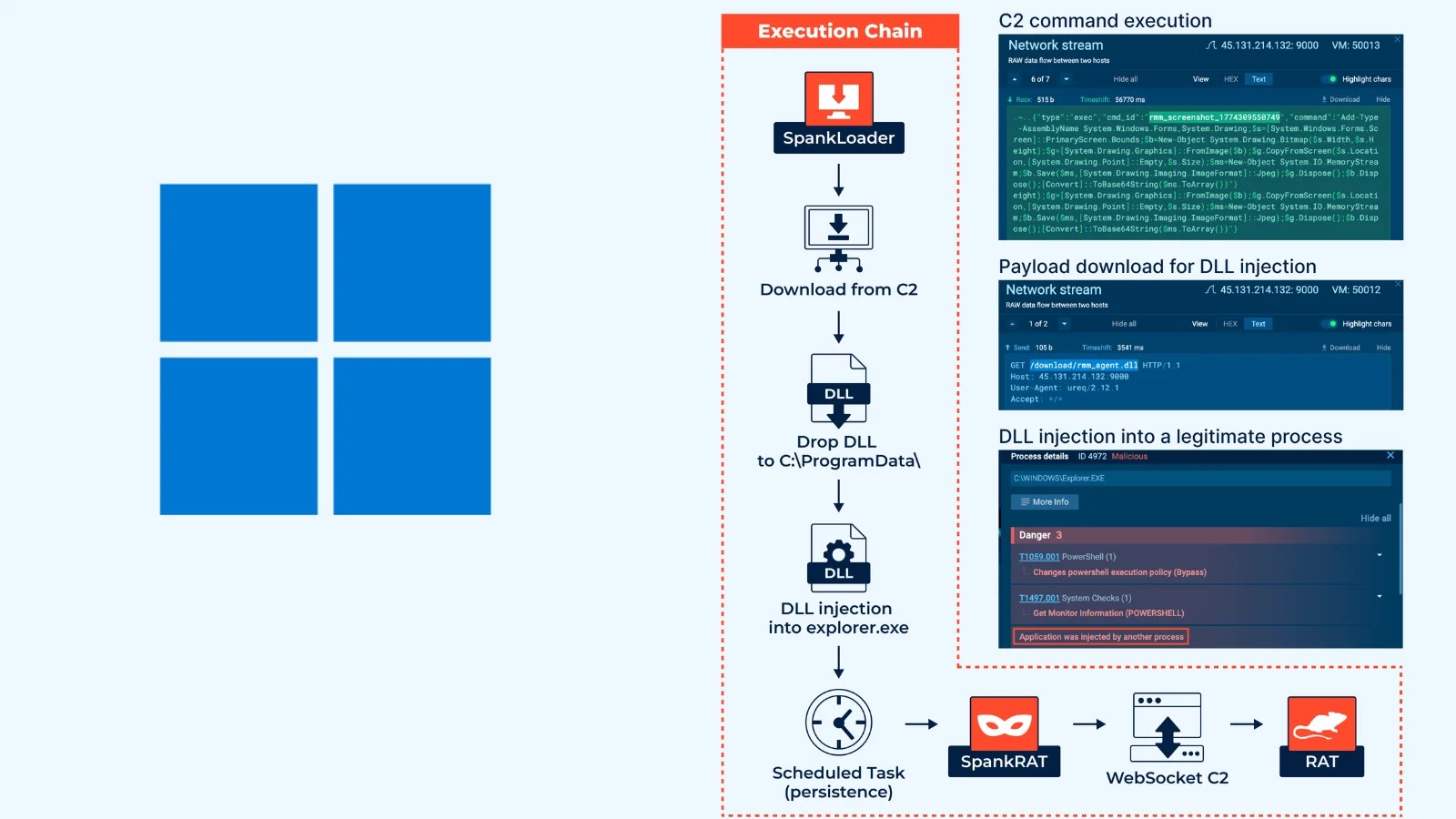
The marketing campaign demonstrates a transparent desire for DLL sideloading methods all through a number of phases of an infection.
Governments and media organizations signify high-value targets as a result of they straight affect coverage selections, form public opinion, and decide worldwide strategic alignment.
The WinRAR file will drop a batch file, which in flip will obtain the following (Supply – CyberArmor)
The malicious marketing campaign operates by means of 4 distinct phases, every designed to take care of persistence whereas avoiding detection by safety merchandise.
After the preliminary dropper executes, a batch script named “Home windows Defender Definition Replace.cmd” downloads extra payloads from Dropbox and establishes registry-based persistence.
The following phases contain reliable software program elements like OBS browser and Adobe Artistic Cloud Helper being exploited to load malicious DLL recordsdata by means of search-order hijacking.
Technical Breakdown of the DLL Sideloading Mechanism
The DLL sideloading method represents the core evasion technique employed all through this marketing campaign. In Stage 2, the menace actors abuse a reliable OBS open-source browser executable to mechanically load a modified libcef.dll file.
This altered library executes malicious code whereas sustaining the looks of regular software program operation. The backdoor communicates with operators by means of Telegram utilizing an encrypted bot token, offering three major instructions: shell execution, screenshot seize, and file add capabilities.
Stage 3 continues the DLL sideloading strategy by exploiting Adobe’s Artistic Cloud Helper element. The reliable “Artistic Cloud Helper.exe” hundreds a malicious CRClient.dll file, which incorporates performance to decrypt and execute the ultimate backdoor payload saved as “Replace.lib.”
The decryption course of makes use of a easy XOR encoding method, demonstrating that subtle encryption will not be at all times needed for profitable operations.
The next code snippet reveals the decryption perform:-
// XOR decryption with hardcoded key
for (size_t i = 0; i < payload_size; i++) {
decrypted_data[i] = encrypted_data[i] ^ 0x3c;
}
The ultimate backdoor supplies complete distant entry capabilities by means of HTTPS communication with command-and-control servers situated at public.megadatacloud[.]com and IP tackle 104.234.37[.]45.
Community visitors stays encrypted utilizing XOR operations, making detection difficult for conventional safety monitoring techniques.
The backdoor helps eight distinct command operations, together with command execution, DLL loading, shellcode execution, file manipulation, and a kill swap perform that terminates operations after random intervals.
Observe us on Google Information, LinkedIn, and X to Get Extra Immediate Updates, Set CSN as a Most popular Supply in Google.