Jack, a Solana fanatic utilizing the Phantom pockets, fell sufferer to a complicated crypto drainer rip-off that worn out $9,000 from his pockets virtually immediately.
He knowledgeable Cybersecurity Information that the incident started with a horny Instagram commercial touting fast earnings that led him to a fraudulent web site. There, a misleading immediate tricked him into approving a transaction underneath the guise of receiving funds, just for malicious JavaScript, particularly “SkyDrainer.js,” to empty his holdings.
The location disappeared shortly after the drain, leaving the consumer shocked however decided to research. Utilizing Google dorking strategies, he uncovered the drainer marketed brazenly on underground boards like Cracked[.]sh and the Russian hacking website LolzTeam.
A discussion board submit on Cracked[.]sh promotes “Supreme #1 Solana Drainer,” providing free entry by way of Telegram bots with options like finest bypasses, free internet hosting, no warnings, cloaking, and a low 10% payment far beneath opponents’ charges.
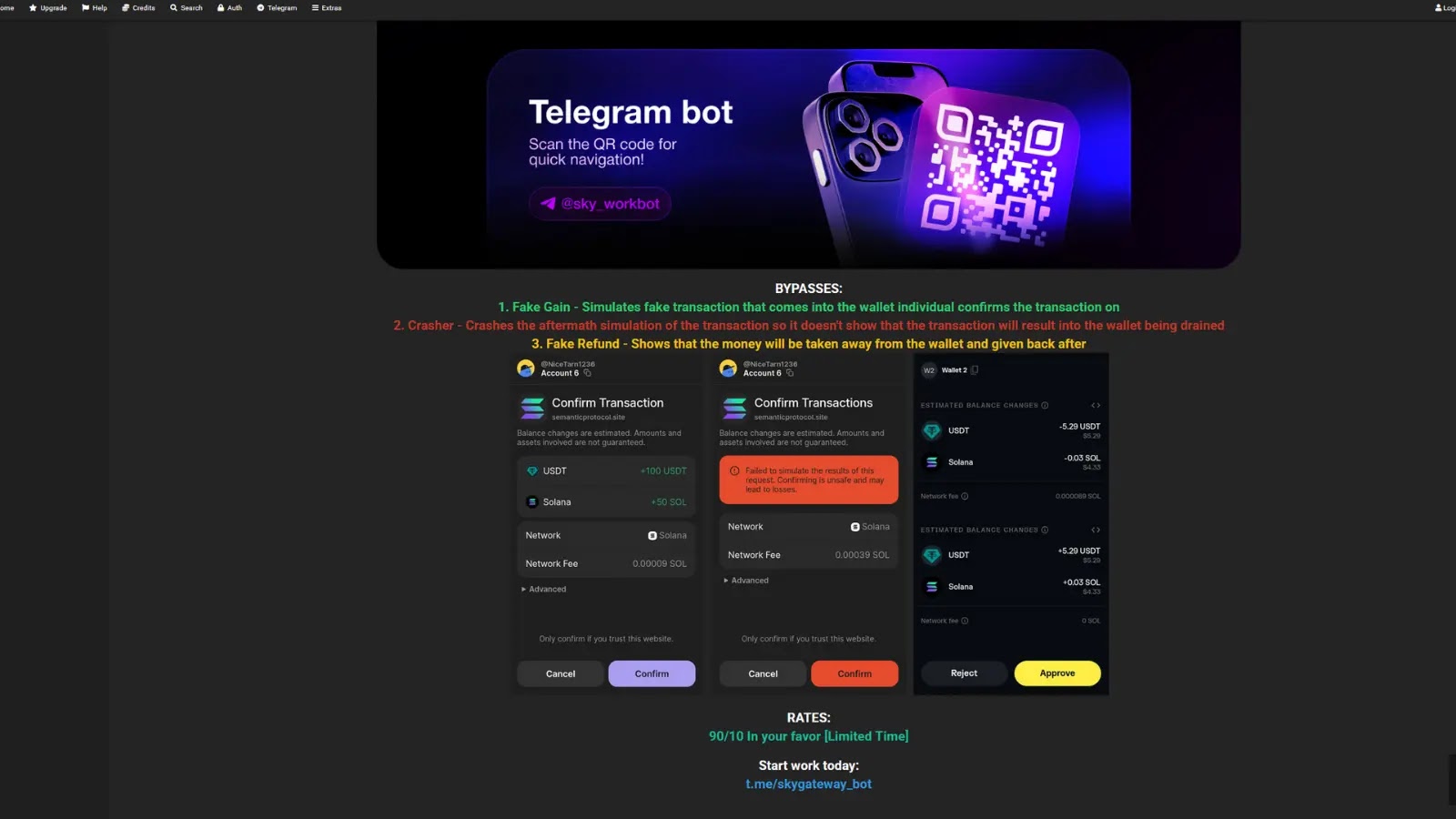
Accessing the Telegram bot revealed a troubling set of pre-made tips designed to keep away from elevating suspicion. Screenshots present choices like “Crasher,” which crashes the approval immediate to cover transaction outcomes; “Faux Acquire,” which reveals false inexperienced notifications of incoming SOL or USDT; and “Faux Return,” which pretends that funds are being withdrawn and refunded.
Phantom pockets settings within the bot additional allow abuse safety modals and pretend achieve prompts, making scams seem legit.
Jack demonstrated the benefit of deployment by producing a completely useful drainer website in simply 3-4 clicks: deciding on a template, linking nameservers, and setting a pockets tackle resulted in a dwell malicious web page similar to his attacker’s.
No technical experience is required, permitting anybody to launch assaults in underneath a minute. Solana drainers have proliferated, with reviews of campaigns stealing thousands and thousands by way of comparable phishing on social media and pretend dApps.
This case underscores the risks of social engineering in crypto, the place drainers like these linked to SkyDrainer exploit pockets approvals. Safety companies observe Russian ties to such kits, bought cheaply on darkish net channels. Victims lose funds irreversibly on the blockchain, break up between associates and operators (typically 80/20).
Platforms like Instagram should tighten advert scrutiny, whereas customers ought to confirm websites, use {hardware} wallets, and allow transaction simulations in Phantom.
Jack withheld his transaction ID pending restoration efforts however urges most publicity: “This must warn others and strain hosts to close down these bots.” Crypto customers, keep vigilant, and join wallets solely on trusted domains.
Comply with us on Google Information, LinkedIn, and X for each day cybersecurity updates. Contact us to function your tales.