A brand new wave of cyberattacks has surfaced the place menace actors are utilizing weaponized PDF information to trick customers into putting in distant monitoring and administration instruments on their methods.
These assaults exploit the trusted nature of RMM software program like Syncro, SuperOps, NinjaOne, and ConnectWise ScreenConnect to realize unauthorized entry to sufferer machines.
The malicious PDF paperwork are disguised with file names similar to “Bill,” “Product Order,” and “Cost,” suggesting they’re being distributed by way of phishing electronic mail campaigns focusing on companies and people alike.
When customers open these PDF information, they encounter both a high-quality picture that stops preview or an error message stating “Didn’t load PDF doc.”
Each situations immediate victims to click on on a hyperlink that redirects them to faux Google Drive pages or fraudulent web sites impersonating Adobe.
The faux Google Drive web page shows what seems to be a video file named “Video_recorded_on_iPhone17.mp4,” which is definitely an RMM installer in disguise.
The downloaded file maintains the misleading naming sample “Video_recorded_on_iPhone17.mp4 Drive.google.com” to additional persuade customers they’re downloading a reputable video.
ASEC researchers recognized that these assaults have been ongoing since at the very least October 2025, based mostly on digital certificates used to signal the malicious installers.
The menace actor behind this marketing campaign has been systematically distributing a number of RMM instruments, all signed with the identical legitimate certificates to evade detection by safety merchandise.
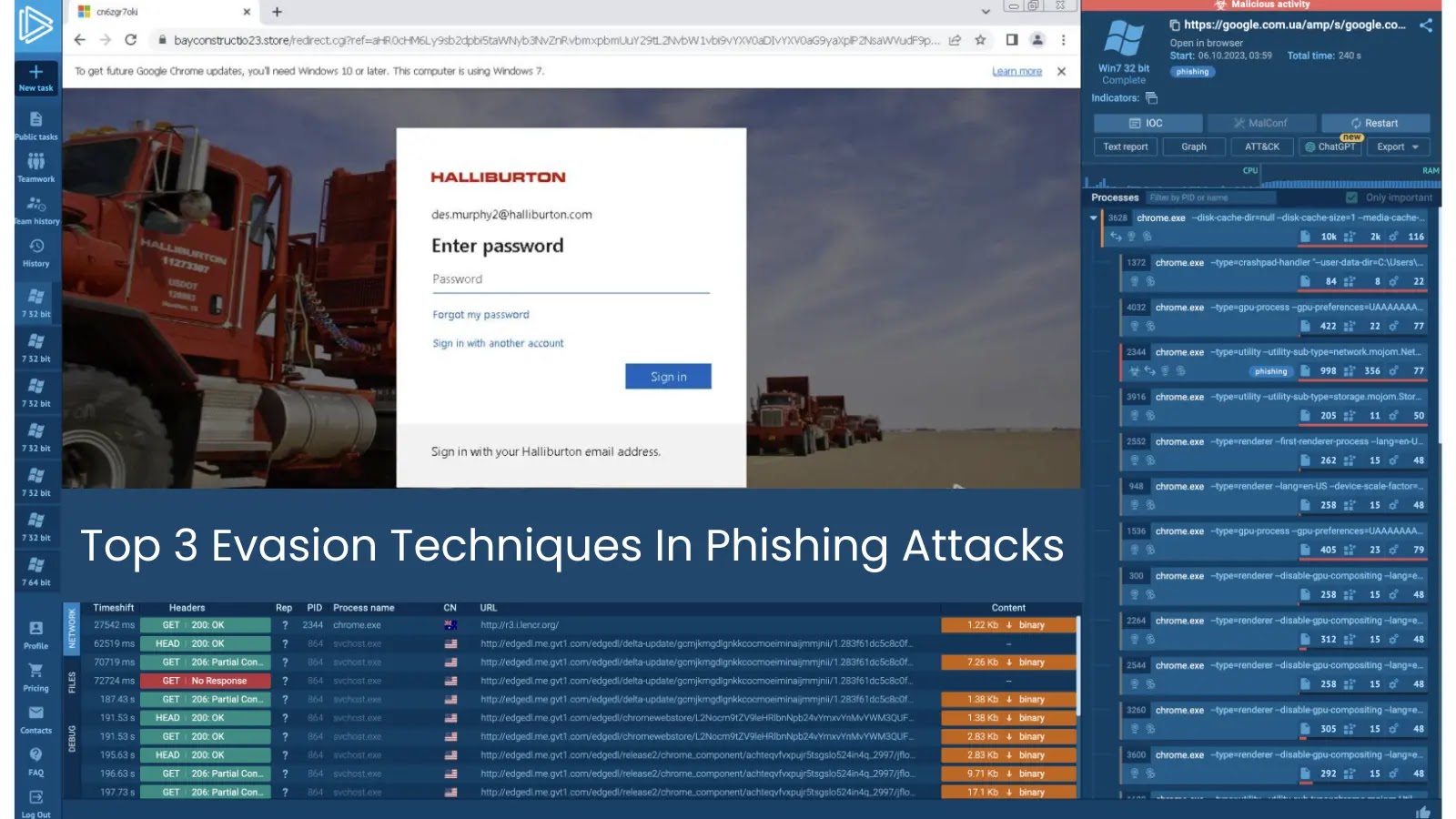
The PDF malware used within the assault – 1 (Supply – ASEC)
This method permits the attackers to bypass conventional safety measures, as RMM instruments are designed for reputable administrative functions and should not labeled as standard malware like backdoors or Distant Entry Trojans.
PDF malware used within the assault – 2 (Supply – ASEC)
The assault leverages the inherent belief that safety options place in RMM software program. Since these instruments are generally utilized by Managed Service Suppliers and IT groups for reputable distant administration, firewalls and anti-malware applications usually battle to establish them as threats.
This creates a harmful blind spot that attackers are actively exploiting to ascertain persistent distant entry to compromised methods.
Technical Breakdown of the An infection Mechanism
The an infection course of begins when the sufferer downloads what they consider is a video file from the faux Google Drive web page.
The downloaded executable is definitely an installer created with Superior Installer or NSIS that deploys the RMM device on the goal system.
Syncro’s web site (Supply – ASEC)
For Syncro RMM installations, the malware makes use of particular parameters throughout execution, together with a “key” worth of “yK0UAOaHHwdbYDOp_sr51w” and a “customerid” of “1709830.”
These configuration particulars permit the menace actor to establish and remotely management contaminated machines by way of the RMM platform’s reputable infrastructure.
Display of the Google Drive phishing web page (Supply – ASEC)
The NSIS-based downloader variant comprises embedded scripts that fetch extra payloads from attacker-controlled servers. The malicious NSI script executes instructions like:
StrCpy $0 $TEMPtemp_response.html
INetC::get/silent $0
This command silently downloads information from the malicious area and prepares the system for additional compromise. The installer then deploys NinjaOne RMM utilizing Home windows Installer with quiet mode execution to keep away from person detection.
Observe us on Google Information, LinkedIn, and X to Get Extra On the spot Updates, Set CSN as a Most popular Supply in Google.