Ravie LakshmananFeb 02, 2026Threat Intelligence / Malware
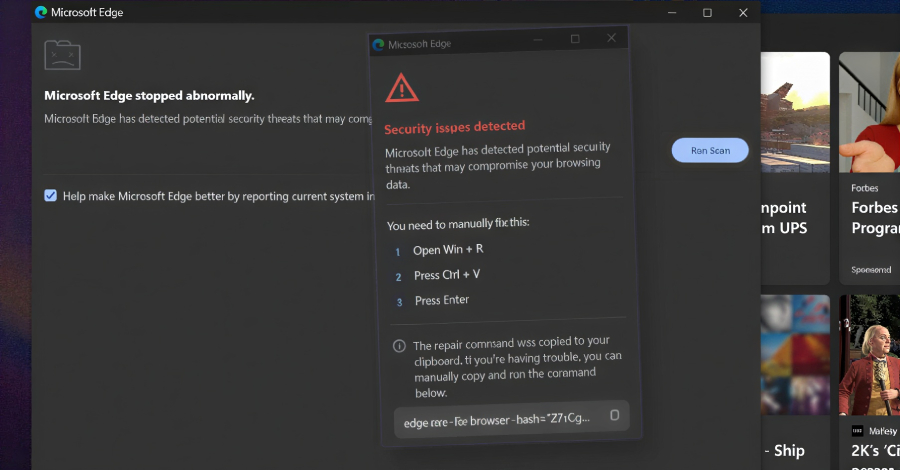
The maintainer of Notepad++ has revealed that state-sponsored attackers hijacked the utility’s replace mechanism to redirect replace visitors to malicious servers as a substitute.
“The assault concerned [an] infrastructure-level compromise that allowed malicious actors to intercept and redirect replace visitors destined for notepad-plus-plus.org,” developer Don Ho stated. “The compromise occurred on the internet hosting supplier degree fairly than by means of vulnerabilities in Notepad++ code itself.”
The precise mechanism by means of which this was realized is at the moment being investigated, Ho added.
The event comes slightly over a month after Notepad++ launched model 8.8.9 to handle a difficulty that resulted in visitors from WinGUp, the Notepad++ updater, being “often” redirected to malicious domains, ensuing within the obtain of poisoned executables.
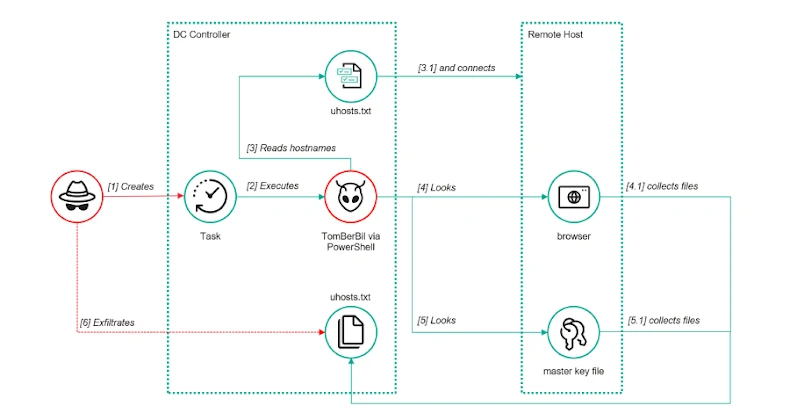
Particularly, the issue stemmed from the way in which the updater verified the integrity and authenticity of the downloaded replace file, permitting an attacker who is ready to intercept community visitors between the updater consumer and the replace server to trick the software into downloading a distinct binary as a substitute.
It is believed this redirection was extremely focused, with visitors originating from solely sure customers routed to the rogue servers and fetching the malicious elements. The incident is assessed to have commenced in June 2025, greater than six months earlier than it got here to gentle.
Unbiased safety researcher Kevin Beaumont revealed that the flaw was being exploited by risk actors in China to hijack networks and deceive targets into downloading malware. In response to the safety incident, the Notepad++ web site has been migrated to a brand new internet hosting supplier.
“In response to the previous internet hosting supplier, the shared internet hosting server was compromised till September 2, 2025,” Ho defined. “Even after dropping server entry, attackers maintained credentials to inside providers till December 2, 2025, which allowed them to proceed redirecting Notepad++ replace visitors to malicious servers.”