The cybercriminal group known as Bloody Wolf has intensified its attacks on organizations located in Russia and Uzbekistan. Employing a more sophisticated strategy, the group now uses NetSupport Manager, a legitimate remote administration tool, to gain unauthorized access while evading detection.
Shift in Tactics by Bloody Wolf
Since their emergence in 2023, Bloody Wolf has targeted sectors such as manufacturing, finance, and IT. Initially relying on the STRRAT remote access trojan, they have recently pivoted to leveraging legitimate software like NetSupport Manager. This shift helps them seamlessly integrate with authorized activities, complicating efforts by defenders to identify malicious actions.
Phishing Emails and Initial Access
The attack sequence typically begins with localized spear-phishing emails. These emails, crafted in languages such as Uzbek, mimic official communications from government or legal entities to incite urgency. Included in these emails are malicious PDFs containing links that trigger the download of a Java-based loader when clicked.
This loader is crucial as it facilitates the deployment of the final malware payload, securing the attackers’ position within the victim’s network.
Infrastructure and Persistence Mechanisms
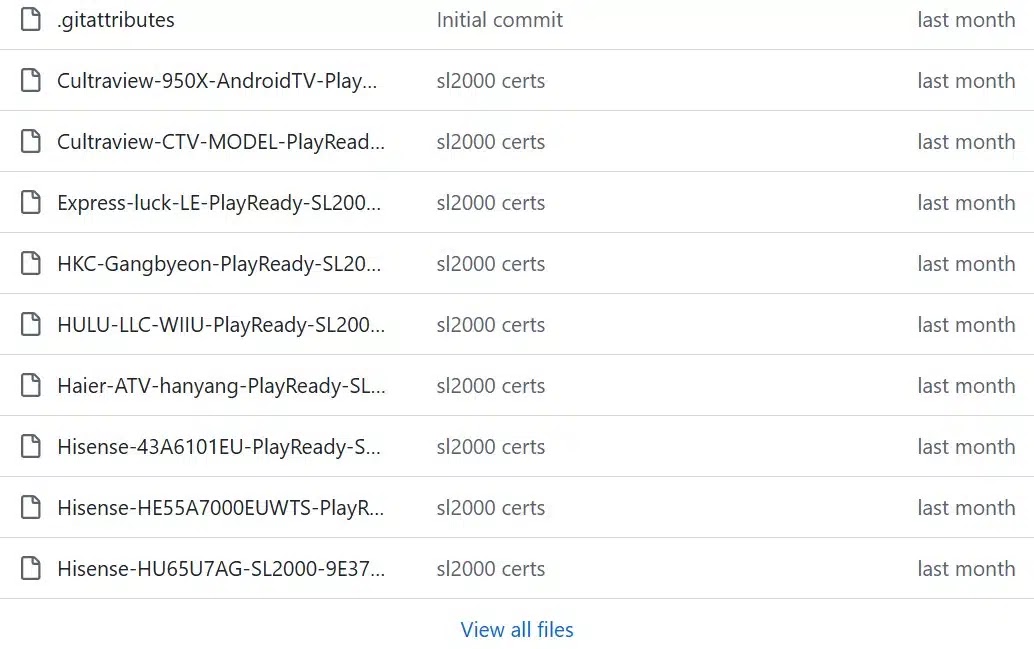
Following the detection of these attacks, analysts at Securelist identified consistent patterns in Bloody Wolf’s operational infrastructure. The group frequently updates its command-and-control domains, creating new ones for each campaign to avoid detection.
Once the malicious loader is executed, a fake error message is displayed to mislead users into believing the application cannot run. Meanwhile, the loader actively downloads NetSupport RAT components and employs checks to terminate itself if unsuccessful, thereby evading sandbox analysis.
For persistence, the malware employs multiple methods, such as placing a script in the Windows Startup folder, adding entries to the Registry’s Run key, and creating scheduled tasks. These measures ensure the malicious tool activates automatically upon user login.
Conclusion and Preventive Measures
To counter these threats, organizations must enhance their monitoring for unauthorized remote desktop tools and scrutinize processes initiated from the Startup folder. Continuous vigilance and updated cybersecurity measures are vital in mitigating the risks posed by the Bloody Wolf group.