Recent discoveries by cybersecurity experts have brought to light a new ransomware variant known as Reynolds. This particular strain incorporates a ‘bring your own vulnerable driver’ (BYOVD) tactic within its payload, aiming to evade detection by compromising endpoint security measures.
Understanding the BYOVD Technique
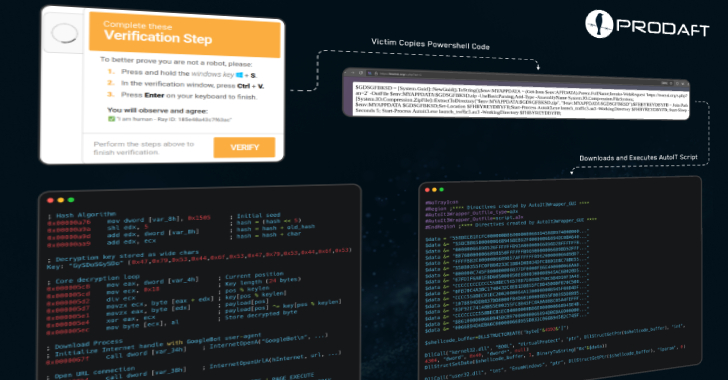
The BYOVD method involves exploiting legitimate yet flawed driver software to gain higher system privileges. By doing so, ransomware operators can disable Endpoint Detection and Response (EDR) systems, effectively concealing malicious activities. This strategy has been widely used by various ransomware groups over time.
Typically, the BYOVD approach requires a separate tool to be installed before deploying the ransomware. However, researchers from Symantec and the Carbon Black Threat Hunter Team noted that the Reynolds ransomware incorporates the vulnerable driver directly within the payload. The driver in question is the NsecSoft NSecKrnl driver, which has been previously bundled in attacks like the Ryuk ransomware incident in 2020.
Details of the Reynolds Campaign
In its latest campaign, Reynolds ransomware not only deploys the NsecSoft NSecKrnl driver but also terminates critical security processes. This includes those from prominent security vendors such as Avast, CrowdStrike Falcon, and Palo Alto Networks Cortex XDR. The driver exploits a known vulnerability (CVE-2025-68947) to disable these protective measures.
This tactic of embedding the evasion component within the ransomware itself complicates defensive measures. It reduces the need for attackers to separately install additional tools, thus minimizing detection risks. The Reynolds attack campaign also revealed the presence of a suspicious side-loaded loader on targeted networks weeks before the ransomware deployment.
Broader Implications and Recent Trends
The use of BYOVD is favored by attackers due to its effectiveness in evading security systems while utilizing legitimate signed files. This integration of evasion techniques directly into ransomware payloads offers a quieter approach, reducing the visibility of the attack.
Recent developments in ransomware strategies show an increased focus on targeting cloud services and leveraging native cloud features to compromise data. Meanwhile, phishing campaigns and the use of virtual machines for delivering malicious payloads have become more prevalent. These tactics highlight the ongoing evolution and professionalization of ransomware operations.
According to recent data, ransomware activities have surged, with new groups emerging and existing ones forming alliances. The average ransom payment has also seen a notable increase, underscoring the growing financial impact of these cyber threats.
As ransomware tactics become more sophisticated, staying informed and vigilant is crucial for organizations to protect themselves against potential threats.