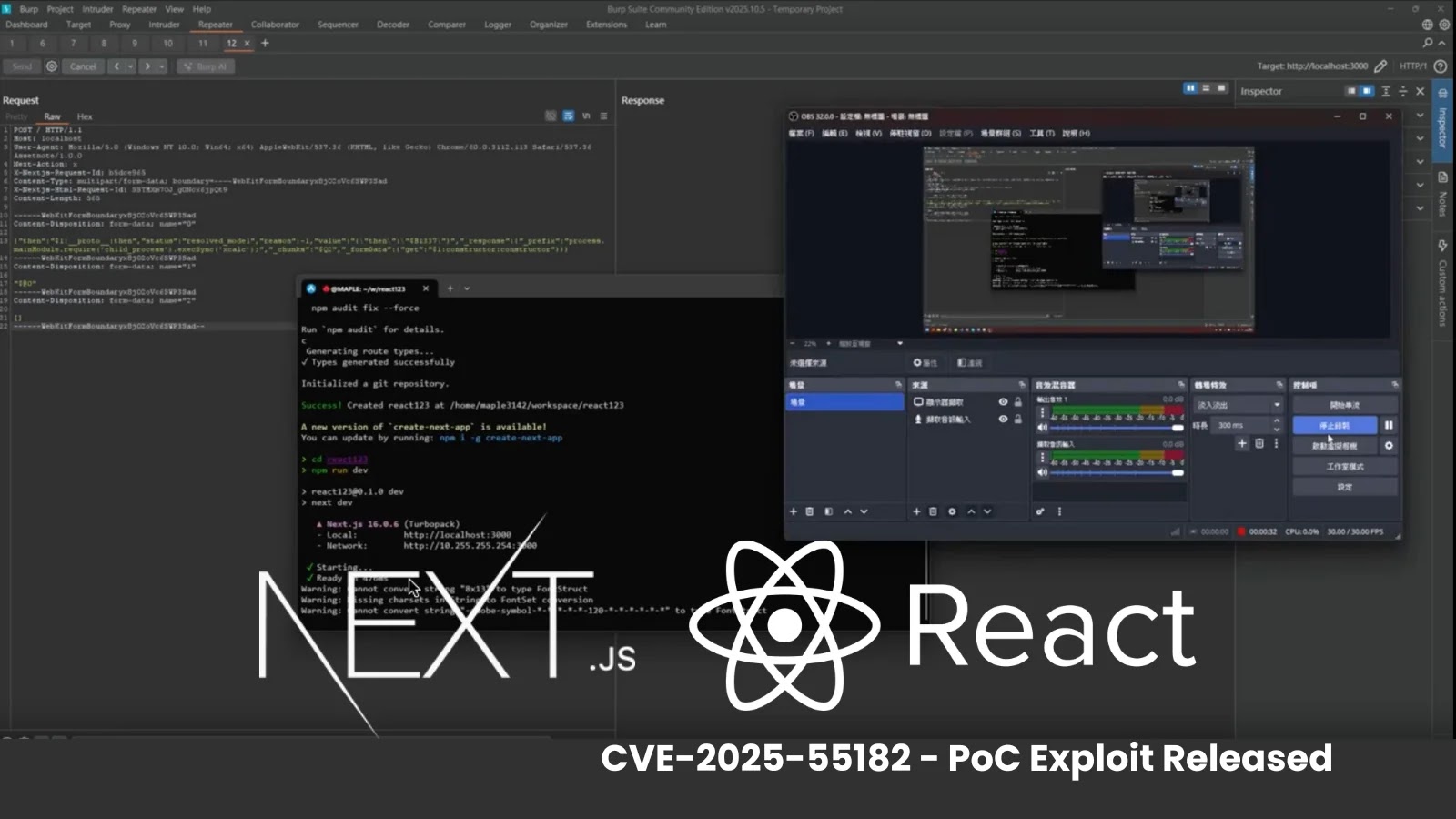
The cybersecurity landscape is facing a significant threat with the emergence of the ‘React2Shell’ vulnerability, identified as CVE-2025-55182. This critical flaw impacts Next.js and React Server Components, posing a severe risk to global enterprises.
Rapid Exploitation Following Disclosure
On December 4, 2025, the vulnerability was publicly disclosed, sparking swift action from malicious actors. Within just 20 hours, exploitation attempts were being directed at systems exposed to the internet. This vulnerability allows attackers to execute arbitrary code on affected servers without authentication, making it a high-priority issue for organizations.
Attackers have been using malicious HTTP POST requests to target specific server routes, such as /_next/server and /_next/flight. By exploiting the server components’ serialization process, they inject unauthorized commands into the application’s runtime environment.
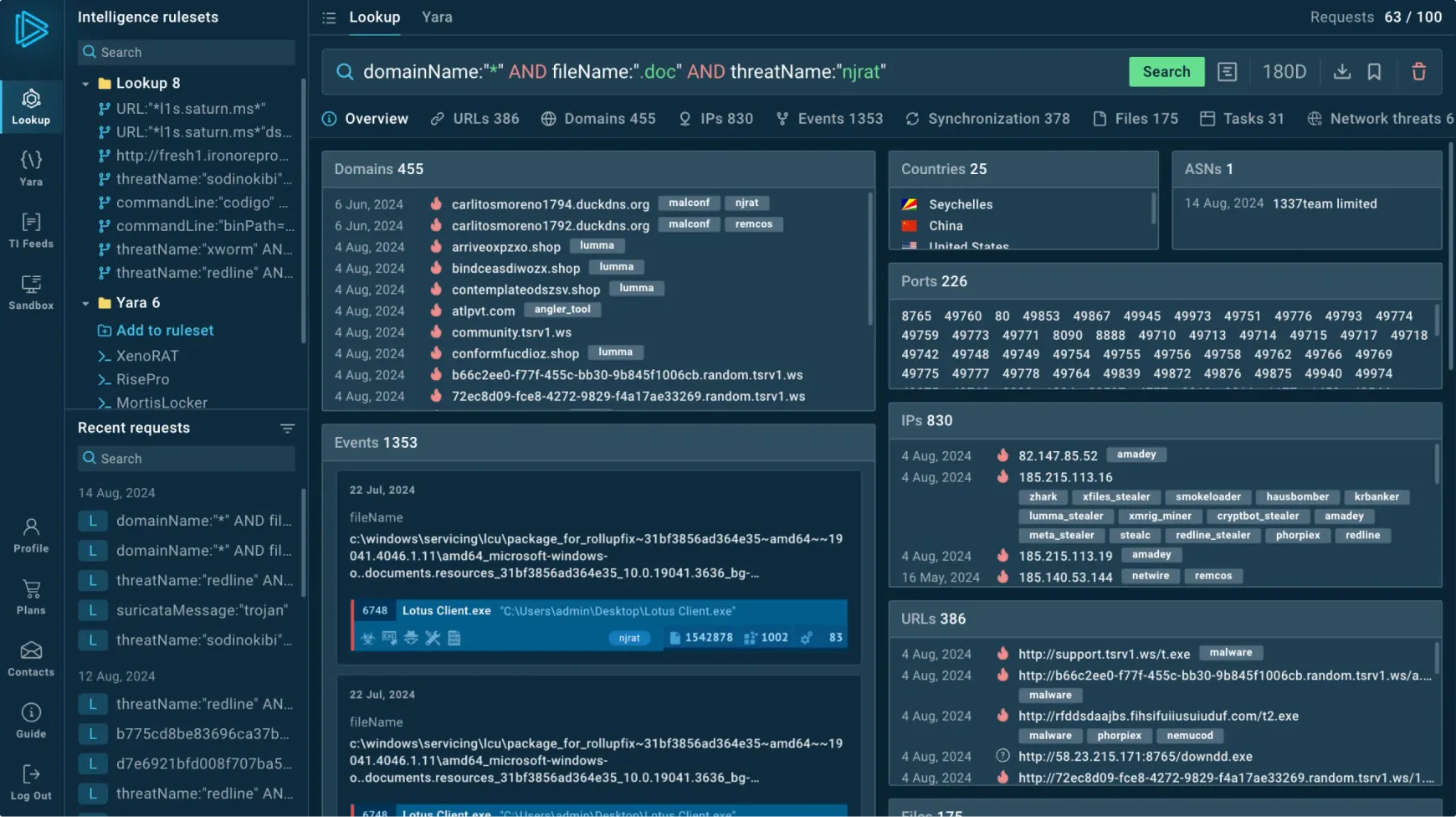
ILOVEPOOP Toolkit: A Major Player
Analysts at WhoisXMLAPI have identified a significant portion of the malicious activities being driven by the ‘ILOVEPOOP’ toolkit. Despite its crude name, this framework is sophisticated, operating from a centralized structure anchored by two high-traffic servers in the Netherlands. These nodes have been connected with millions of global endpoints, indicating a widespread effort to exploit vulnerable networks across various sectors, including SaaS, retail, and government.
The toolkit is distinguished by a unique and consistent attack signature, aiding defenders in detection. It employs a cluster of nine scanner nodes that rotate operations to avoid detection and blocklists. One notable feature is the use of specific non-standard HTTP headers, such as X-Nextjs-Request-Id: poop1234 and Next-Action: x, which link numerous attacks back to the toolkit’s operators.
Defensive Measures and Recommendations
The toolkit uses a systematic approach to probing Next.js paths for vulnerabilities, starting with reconnaissance on login pages and advancing to complex payloads involving prototype pollution. With the Netherlands-based IPs (193.142.147[.]209 and 87.121.84[.]24) acting as primary hubs, blocking these and filtering for distinct header patterns is essential to mitigate the threat.
Security teams are advised to urgently update affected Next.js systems and configure Web Application Firewalls (WAF) to block requests containing the malicious headers. Additionally, restricting traffic from the identified Netherlands servers is recommended to disrupt the toolkit’s communication channels effectively.
Stay informed by following our updates on Google News, LinkedIn, and X. Make CSN your preferred source for the latest security news.