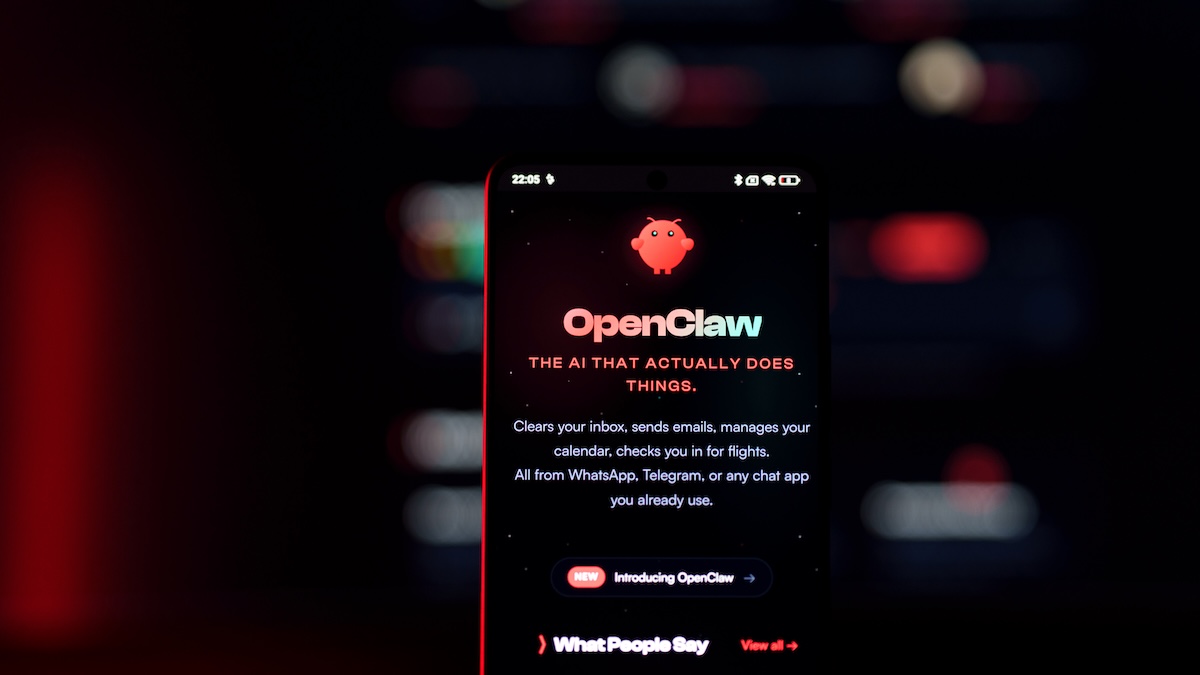
Cybersecurity experts at Kaspersky have recently identified a new Android malware known as Keenadu, which allows remote control over infected devices. The malware has primarily been found embedded in the firmware of a variety of Android brands, with a significant presence in tablets.
Malware Distribution and Capabilities
Keenadu has been detected in firmware either during the development phase or delivered through over-the-air (OTA) updates. The malware grants operators full access to compromised devices, primarily for executing ad fraud. Kaspersky researchers have observed Keenadu payloads performing tasks such as hijacking browser search engines, monetizing app installations, and generating ad clicks.
Prevalence and Distribution Channels
Many devices came preloaded with this malware, while others received it through app stores, including Google Play and Xiaomi GetApps, disguised as smart camera applications. These malicious apps were downloaded over 300,000 times before their removal from Google Play.
Impact and Connections to Other Botnets
Kaspersky’s security solutions have identified Keenadu infections on approximately 13,000 devices, predominantly in Russia, Japan, Germany, Brazil, and the Netherlands. The malware code is loaded into the address space of every app upon launch. In some cases, it was integrated into critical system utilities such as facial recognition and the launcher app.
Researchers have uncovered links between Keenadu and several large botnets, including Triada, Vo1d, and BadBox, all of which primarily exploit low-cost Android devices. Evidence points to Chinese origins for Keenadu, similar to these other botnets. Although connections between these botnets exist, Kaspersky cautions that these linkages are not necessarily direct, noting that further evidence is required to confirm any transitive relationships.
The discovery of Keenadu underscores the persistent threat of malware in mobile devices, and ongoing investigations may reveal further complexities in these interconnected botnet networks.