Microsoft has issued a warning to developers about a campaign utilizing fake job repositories to deploy malware. These repositories appear as legitimate Next.js projects but are designed to infiltrate systems and establish persistent access.
Malicious Campaign Targeting Developers
This campaign, identified as a coordinated effort, leverages job-themed lures to blend with typical developer activities. According to the Microsoft Defender Security Research Team, these tactics increase the likelihood of executing malicious code on targeted machines.
The attackers use platforms like Bitbucket to create repositories with deceptive names such as ‘Cryptan-Platform-MVP1’. Developers, misled by these names, inadvertently run these scripts during assessments, facilitating malware deployment.
Execution Techniques and Analysis
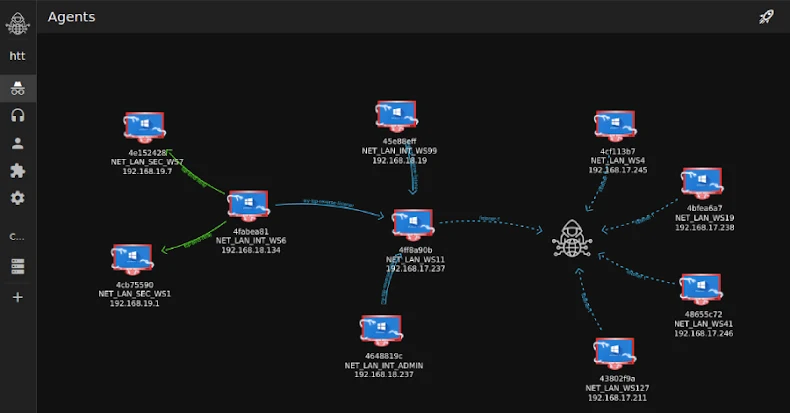
Microsoft reports three execution paths that lead to the same malicious outcome. First, Visual Studio Code workspaces are used to execute harmful JavaScript once the project is opened and trusted. Second, during build-time, the ‘npm run dev’ command triggers malicious scripts masquerading as legitimate JavaScript libraries. Lastly, server startup execution involves environment exfiltration, executing code on backend modules.
All paths lead to a JavaScript payload that profiles the host and communicates with a registration endpoint. This enables a second-stage controller to maintain persistent access, executing further commands from a control server.
Implications and Future Outlook
While Microsoft has not linked the campaign to a specific threat actor, similar tactics have been used by North Korean-linked groups. The objective is to access sensitive developer systems containing valuable data like source code and credentials.
To mitigate such threats, organizations should enhance developer workflow security, enforce strong authentication, and maintain strict credential policies. GitLab has also taken measures by banning accounts distributing malicious projects, shedding light on the scale of this operation.
This development underscores the need for vigilance in developer environments. As threat actors evolve, robust security practices become essential to safeguard against sophisticated attacks.