A significant supply chain attack has emerged, compromising the renowned Trivy scanner and affecting several npm packages with a new self-propagating malware known as CanisterWorm. This cyber threat capitalizes on the ICP canister, a tamper-proof smart contract on the Internet Computer blockchain, to execute its malicious activities. The attack signifies the first known exploitation of an ICP canister for accessing command-and-control (C2) servers, as reported by Charlie Eriksen, a researcher at Aikido Security.
Details of the Supply Chain Compromise
The breach has impacted numerous npm packages, including 28 from the @EmilGroup scope, 16 from the @opengov scope, and others like @teale.io/eslint-config and @airtm/uuid-base32. This incident follows the compromise of credentials used to release malicious versions of Trivy, trivy-action, and setup-trivy, which contained a credential-stealing component. The cybercriminal group TeamPCP is suspected to be orchestrating these attacks.
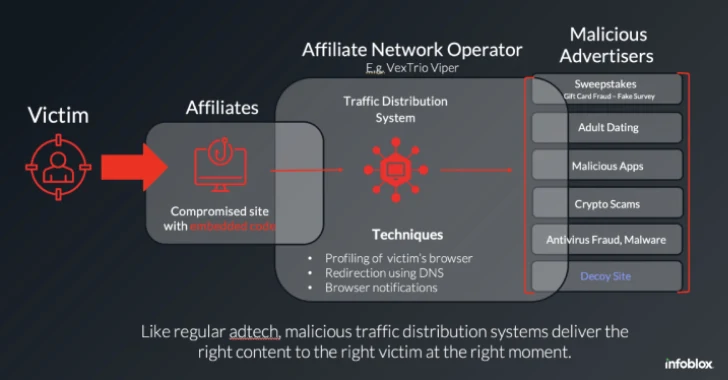
The infection process involves the use of a postinstall hook to deploy a loader that plants a Python backdoor. This backdoor communicates with the ICP canister to obtain a URL leading to further payloads. The decentralized nature of the canister’s infrastructure makes it resistant to takedown attempts, enhancing its persistence.
Mechanics of CanisterWorm’s Propagation
Persistence is maintained through a systemd user service, which automatically restarts the Python backdoor. This service disguises itself as PostgreSQL tooling to avoid detection. Every 50 minutes, the backdoor contacts the ICP canister using a spoofed User-Agent to fetch a URL. If the URL includes youtube[.]com, the script remains inactive. The attacker can activate the malware by directing the canister to a legitimate binary, and deactivate it by reverting to a YouTube link.
The ICP canister supports various functions like get_latest_link and update_link, enabling the attacker to modify its operations. Additionally, the worm’s propagation is facilitated by a “deploy.js” file, which the attacker manually executes to expand the payload across accessible npm packages using stolen tokens.
Evolving Threat and Future Implications
Recent updates to the CanisterWorm, particularly in “@teale.io/eslint-config” versions 1.8.11 and 1.8.12, enable self-propagation without manual input. The new variant integrates its functionality within “index.js,” utilizing npm authentication tokens from compromised machines to spread the malware autonomously.
This development signifies a shift from isolated account compromises to widespread malware propagation. Developers and CI pipelines with exposed npm tokens inadvertently become vectors for further infection. The attackers have tested this mechanism using a dummy payload, likely to confirm its effectiveness before deploying the actual malware.
As this cyber threat evolves, it underscores the critical need for vigilant monitoring of software dependencies and enhanced credential security to prevent further breaches in the supply chain. Stakeholders are advised to stay updated as more information becomes available.