A newly discovered rootkit known as NoVoice has infiltrated over 50 applications available on Google Play, compromising the security of more than 2.3 million Android devices globally. This malware, part of a campaign called Operation NoVoice, utilizes 22 different exploits to hijack devices without triggering any warnings, representing one of the most significant threats to Android security in recent times.
How NoVoice Malware Operates
The malicious applications hosting NoVoice appeared benign, masquerading as utilities like phone optimizers, gallery apps, and casual games. Despite their normal appearance and lack of unusual permission requests, these apps concealed malicious activities. Upon being launched, they connected to a remote server to map device specifications and strategically deploy exploits.
McAfee’s mobile research team uncovered this operation, noting the malware’s name originates from a silent audio file embedded in its payloads. This file plays at zero volume to maintain a background service, allowing attackers a discreet and persistent presence on infected devices. The deliberate misspelling of ‘no voice’ underscores the malware’s silent operational nature.
Global Impact and Vulnerabilities
The breadth of this campaign is alarming, with over 50 compromised apps identified and subsequently removed from Google Play. These apps accumulated at least 2.3 million downloads, impacting users across multiple continents. The highest infection rates were observed in regions like Nigeria, Ethiopia, Algeria, India, and Kenya, where older, unpatched Android devices are prevalent.
Following McAfee’s responsible disclosure, Google took swift action to remove the malicious apps and ban the developer accounts involved. Devices with security patches dated May 1, 2021, or later are safeguarded against the exploits leveraged by NoVoice. However, older devices running Android 7 or below remain highly vulnerable, with a factory reset insufficient to eliminate the rootkit.
Technical Details and Protective Measures
The infection process begins when a user opens an affected app, with malicious code executing silently in the background. The malware uses sophisticated techniques to avoid detection, including hiding an encrypted payload within what appears to be a standard image file.
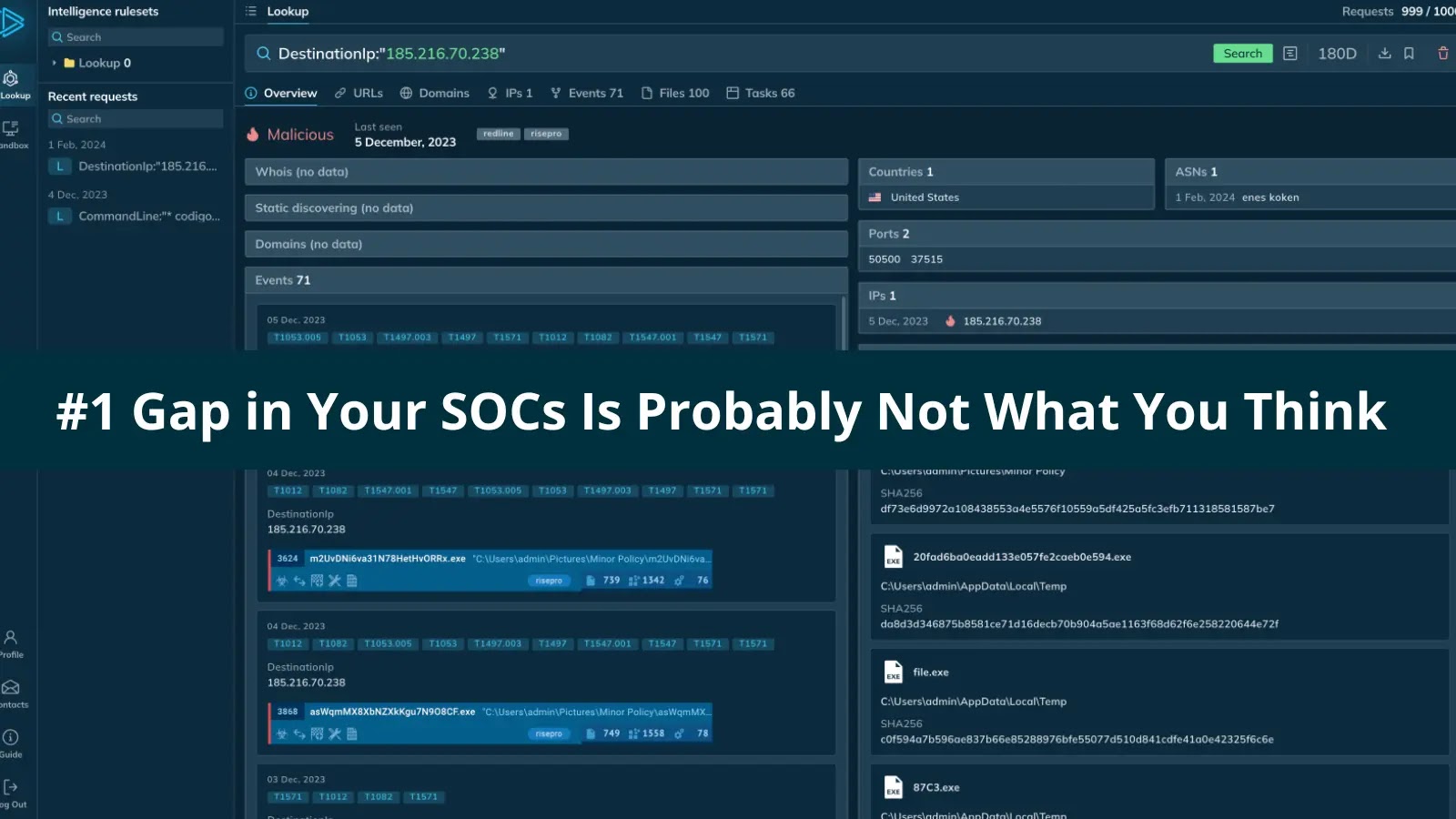
Before proceeding, the malware performs 15 verification checks to evade detection, excluding devices physically located in Beijing and Shenzhen. If successful, it contacts a command-and-control server to download tailored root exploits for the device’s chipset and kernel version. A total of 22 exploits were identified, with one specifically designed to disable Android’s SELinux protections.
To mitigate risks, users should ensure their devices are updated with at least the May 1, 2021, security patch. Blocking known command-and-control domains at the network level can disrupt the malware’s operational chain. Additionally, users are advised to download applications exclusively from reputable sources and remain cautious with utility and gaming apps.
For those suspecting infection, a full firmware reflash is recommended as a factory reset is ineffective against this rootkit. Staying informed and vigilant is crucial in safeguarding one’s device from such sophisticated cyber threats.