A major security flaw in the Flowise AI platform, an open-source application, is currently under exploitation by cybercriminals, as revealed by VulnCheck. Identified as CVE-2025-59528, this vulnerability has been assigned the maximum severity score of 10.0 under the Common Vulnerability Scoring System (CVSS).
Understanding the Vulnerability
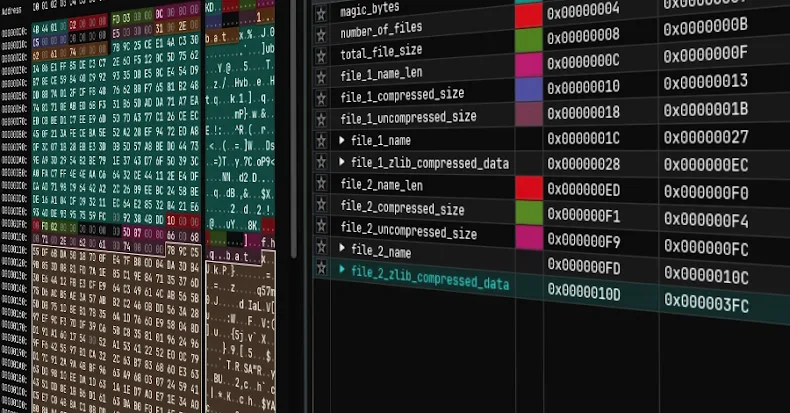
The flaw, a code injection vulnerability, allows for remote code execution via the CustomMCP node. This node processes user inputs to configure connections to external servers using a string called mcpServerConfig. Unfortunately, Flowise’s advisory from September 2025 highlighted that this process executes JavaScript code without proper security checks.
When exploited, this vulnerability grants attackers access to critical Node.js modules like child_process and fs, enabling command execution and file system access. In essence, attackers can execute arbitrary JavaScript code, leading to complete system compromise and potential data breaches.
Security Implications and Responses
Flowise has emphasized the significant risk posed by this vulnerability, as it only requires an API token to exploit, threatening business operations and customer data. The issue was initially discovered and reported by Kim SooHyun and has since been addressed in version 3.0.6 of the npm package.
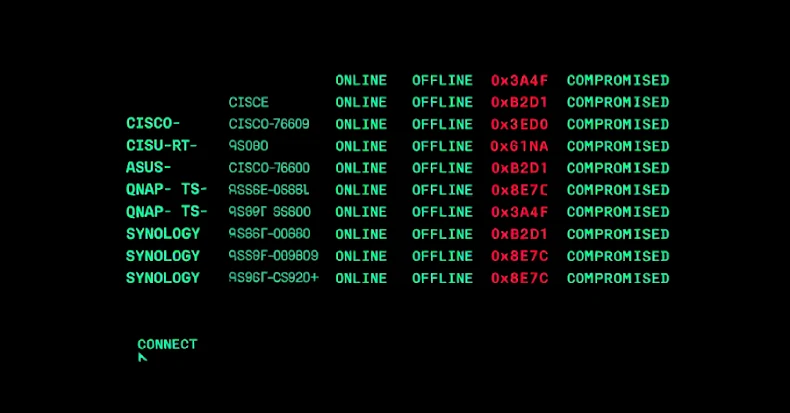
VulnCheck reported that the exploitation attempts are traced back to a single Starlink IP address. This vulnerability marks the third instance of a Flowise flaw being exploited in the wild, following CVE-2025-8943 and CVE-2025-26319, with CVSS scores of 9.8 and 8.9, respectively.
Wider Impact and Future Outlook
Caitlin Condon from VulnCheck described this as a critical-severity bug affecting a widely used AI platform by numerous large companies. Despite being publicly known for over six months, many instances remain vulnerable. The exposure of over 12,000 instances has expanded the attack surface significantly, making them attractive targets for opportunistic attackers.
As the situation unfolds, it is crucial for organizations using Flowise AI to ensure their systems are updated and patched promptly to mitigate potential risks. Continuous monitoring and proactive security measures are recommended to safeguard against future exploitation attempts.