A previously unidentified cyber threat group, designated UAT-10362, has been linked to spear-phishing attacks aimed at non-governmental organizations (NGOs) in Taiwan. These attacks utilize a novel Lua-based malware known as LucidRook, targeting these organizations to deploy malicious payloads. Cisco Talos researcher Ashley Shen highlighted that LucidRook is a complex stager that incorporates a Lua interpreter and Rust-compiled libraries within a DLL to download and execute staged Lua bytecode payloads.
Details of the Attack
The cybersecurity firm observed these activities starting in October 2025. The attackers employed RAR or 7-Zip archive files as lures, which contained a dropper named LucidPawn. This dropper initiates the attack by opening a decoy file and subsequently launching LucidRook. A defining feature of the attack is the use of DLL side-loading to execute both LucidPawn and LucidRook.
There are two primary infection chains leading to LucidRook. The first involves a Windows Shortcut (LNK) file with a PDF icon, which when clicked, runs a PowerShell script that executes a Windows binary (“index.exe”) to sideload a malicious DLL, LucidPawn. The second chain involves an executable disguised as a Trend Micro antivirus program (“Cleanup.exe”), which acts as a .NET dropper to run LucidRook. Once executed, it displays a cleanup completion message.
Technical Mechanisms
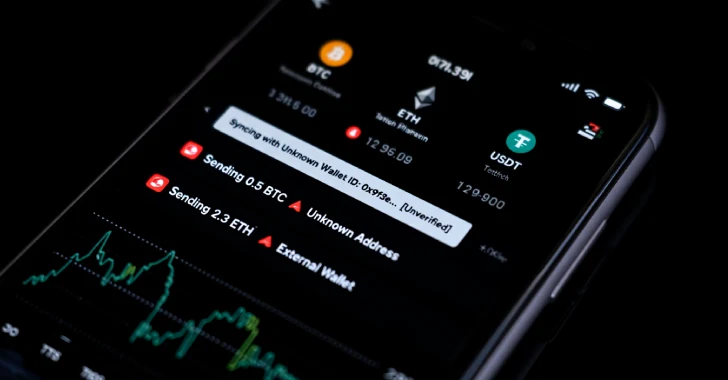
LucidRook, a heavily obfuscated 64-bit Windows DLL, is designed to evade detection and analysis. It serves dual purposes: collecting system information to send to an external server and receiving encrypted Lua bytecode payloads for decryption and execution on the infected machine via an embedded Lua 5.4.8 interpreter. The attackers utilized an Out-of-band Application Security Testing (OAST) service and compromised FTP servers for their command-and-control (C2) operations.
To further target specificity, LucidPawn employs geofencing by querying the system UI language and proceeding only if it matches Traditional Chinese settings linked with Taiwan. This strategy helps focus the attack on intended victims while avoiding detection in common analysis environments.
Implications and Future Outlook
One variant of the dropper, LucidKnight, has been discovered to exfiltrate system information to a temporary Gmail address, indicating the adversary’s use of a multi-tiered toolkit. This suggests a methodical approach where LucidKnight profiles targets before deploying LucidRook. Although much about UAT-10362 remains unknown, current evidence points to a sophisticated threat actor prioritizing targeted attacks rather than opportunistic ones.
Cisco Talos emphasizes that the threat actor’s use of modular malware design, anti-analysis features, and reliance on compromised infrastructure showcases their advanced operational techniques. As such, UAT-10362 represents a significant cyber threat with mature tradecraft, necessitating vigilance and enhanced security measures from potential targets.