Cybersecurity experts have recently identified a significant threat involving fake Microsoft Visual Studio Code (VS Code) extensions, revealing a new wave of malware known as GlassWorm v2. A total of 73 extensions, discovered on the Open VSX repository, are linked to this information-stealing campaign.
Malicious Extensions Disguised as Legitimate Tools
Among these 73 extensions, six have been confirmed as harmful, while the remainder initially appear benign to gain user trust. These extensions mimic legitimate versions to deceive developers into installing them. This tactic, termed “visual trust,” leverages familiar icons and descriptions to increase downloads before executing their malicious intent.
The extensions were first published earlier this month, according to Socket, a security firm tracking the evolution of GlassWorm v2. Since its discovery in December 2025, over 320 artifacts have been associated with this campaign. Some of the identified malicious extensions include outsidestormcommand.monochromator-theme and keyacrosslaud.auto-loop-for-antigravity.
Advanced Evasion Techniques
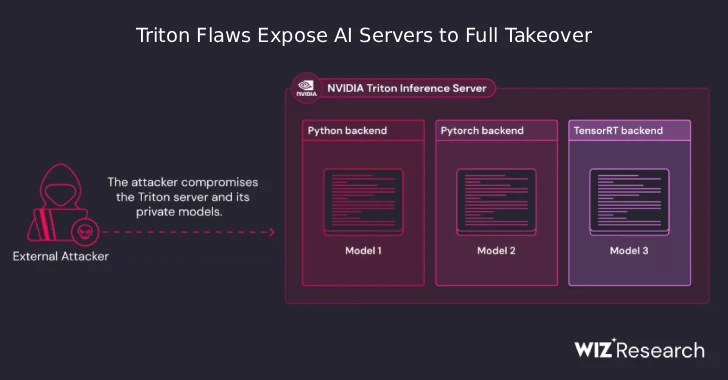
Threat actors are refining their strategies, utilizing sleeper packages and transitive dependencies to avoid detection. Additionally, they employ Zig-based droppers to deploy secondary VSIX extensions from GitHub, capable of infecting various integrated development environments (IDEs) on a developer’s machine.
The strategy involves using seemingly harmless extensions as loaders to fetch and install the actual payload from GitHub. This payload, a VSIX extension, is deployed across IDEs like VS Code, Cursor, Windsurf, and VSCodium, using the “–install-extension” command.
Ultimate Goal: Data Theft and System Compromise
The primary objective of these malicious activities is to execute malware that bypasses Russian systems, exfiltrate sensitive data, and install remote access trojans (RATs). Furthermore, it stealthily deploys rogue Chromium-based extensions designed to capture credentials, bookmarks, and other personal information.
This approach, while maintaining the same end result as previous binary-based methods, uses obfuscated JavaScript to keep the delivery mechanism less detectable. The extension functions as a loader, with the payload activated post-installation.
As these threats continue to develop, it is crucial for developers and organizations to remain vigilant and implement robust security measures to protect their systems from such sophisticated attacks.