A new cybersecurity threat has emerged with the discovery of the Fast16 malware, a Lua-based malicious software that predates the infamous Stuxnet worm. Designed to target high-precision calculation software, Fast16 aims to subtly manipulate outputs, potentially leading to catastrophic outcomes. This malware, active since 2005, highlights ongoing vulnerabilities in systems thought to be secure.
The Fast16 Malware Threat
Fast16’s emergence has been a shocking revelation in the cybersecurity community. This malware predates Stuxnet, a well-known joint U.S.-Israeli project that changed the landscape of cyber warfare. Fast16’s ability to alter scientific calculations may cause systems to wear out or fail prematurely, leading to incorrect research outcomes and potential safety hazards, according to security researcher Vitaly Kamluk.
Despite its potential for harm, it’s unclear if Fast16 has been deployed in the wild. The malware’s existence suggests a long-standing capability for sophisticated cyber operations, raising questions about other unknown threats lurking in the digital landscape.
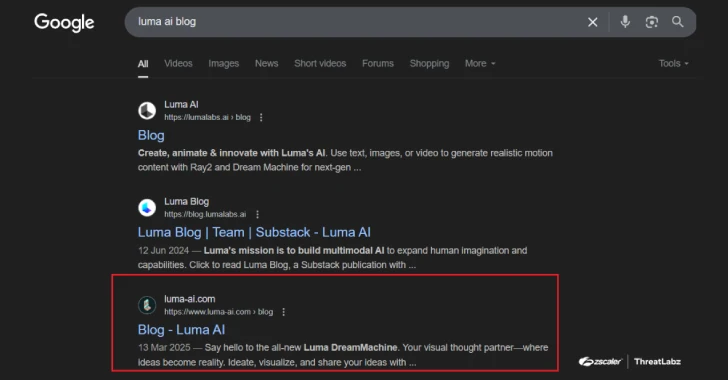
Recent Cybersecurity Incidents
In related news, a new cyber threat group, UNC6692, has been using a custom malware suite named Snow to infiltrate networks. By impersonating Teams help desks, they engage in social engineering tactics to steal sensitive information. Meanwhile, a U.S. federal agency was targeted by the FIRESTARTER backdoor, a sophisticated malware designed for persistent remote access.
Furthermore, the energy sector in Venezuela has been hit by the Lotus Wiper malware, which erases data and disrupts operations. Such incidents underscore the evolving nature of cyber threats and the necessity for robust security measures.
Implications and Future Outlook
The discovery of Fast16 and other recent cyber threats highlight the persistent vulnerabilities in digital infrastructure. Organizations must prioritize updating security protocols and patching known vulnerabilities to mitigate risks. The use of advanced persistent threats (APTs) and custom malware tools demonstrates a growing sophistication in cyber attacks.
As cyber threats continue to evolve, the importance of comprehensive cybersecurity strategies becomes more critical. Businesses and government agencies alike must remain vigilant, ensuring their systems are updated and that they employ the latest security technologies to protect against these emerging threats.
The cybersecurity landscape remains dynamic, with new threats emerging regularly. Staying informed and proactive is essential for safeguarding sensitive data and maintaining operational integrity.