Global Surge in Cyber Threats
In 2026, educational institutions including schools, universities, and research facilities worldwide are experiencing a significant upsurge in cyber threats. State-backed espionage groups, spear-phishing campaigns, and supply chain attacks have heightened the alert within the education sector. Recent data indicates that educational entities were involved in 20% of all advanced persistent threat (APT) campaigns in the first quarter of 2026, a notable increase from the previous quarter.
State-Sponsored Attacks on the Rise
The current trend reveals the emergence of state-sponsored actors in targeting the education sector, which had previously been largely ignored by these groups. Every APT campaign impacting educational institutions during this period was attributed to state-backed entities, with no financially motivated actors observed.
China-linked groups are at the forefront, with MISSION2074 leading four initiatives, followed by Stone Panda, Hafnium, and Lotus Blossom. Iran’s Charming Kitten is the only non-Chinese actor involved, focusing on academic and research institutions in the Middle East, including Gulf nations.
Geographic Distribution and Attack Techniques
Analysis by Cyfirma highlights that victims span 27 countries, with the United States having the highest number of affected institutions, followed by the United Kingdom, Japan, India, South Korea, and Germany. The attack spread is broader compared to other sectors, with a significant presence in European nations.
In addition to APT activities, Q1 2026 saw supply chain attacks and spear-phishing as prominent techniques against educational organizations. While only 1.49% of industry-linked incidents were reported in education, experts suggest this may reflect under-reporting rather than a lack of risk.
Technological and Strategic Implications
Ransomware attacks also decreased by 25% from the previous quarter, yet universities and research institutes remain primary targets. Interlock emerged as a key player, focusing 27.3% of its attacks on education, which is significantly higher than the sector’s average.
Unlike other sectors where network infrastructure is the main target, attackers in the education space aim at email servers, FTP servers, and SSHD servers. This shift underscores an intent to access research data and communications rather than disrupt operations.
The focus on intellectual property held by academic institutions aligns with the strategic objectives of state-sponsored espionage. Institutions house sensitive information, rendering them valuable targets for nation-states seeking intelligence quietly.
Dark web monitoring showed a rise in hacktivism mentions and DDoS-related chatter, indicating ideologically motivated campaigns alongside state espionage.
Recommendations for Educational Institutions
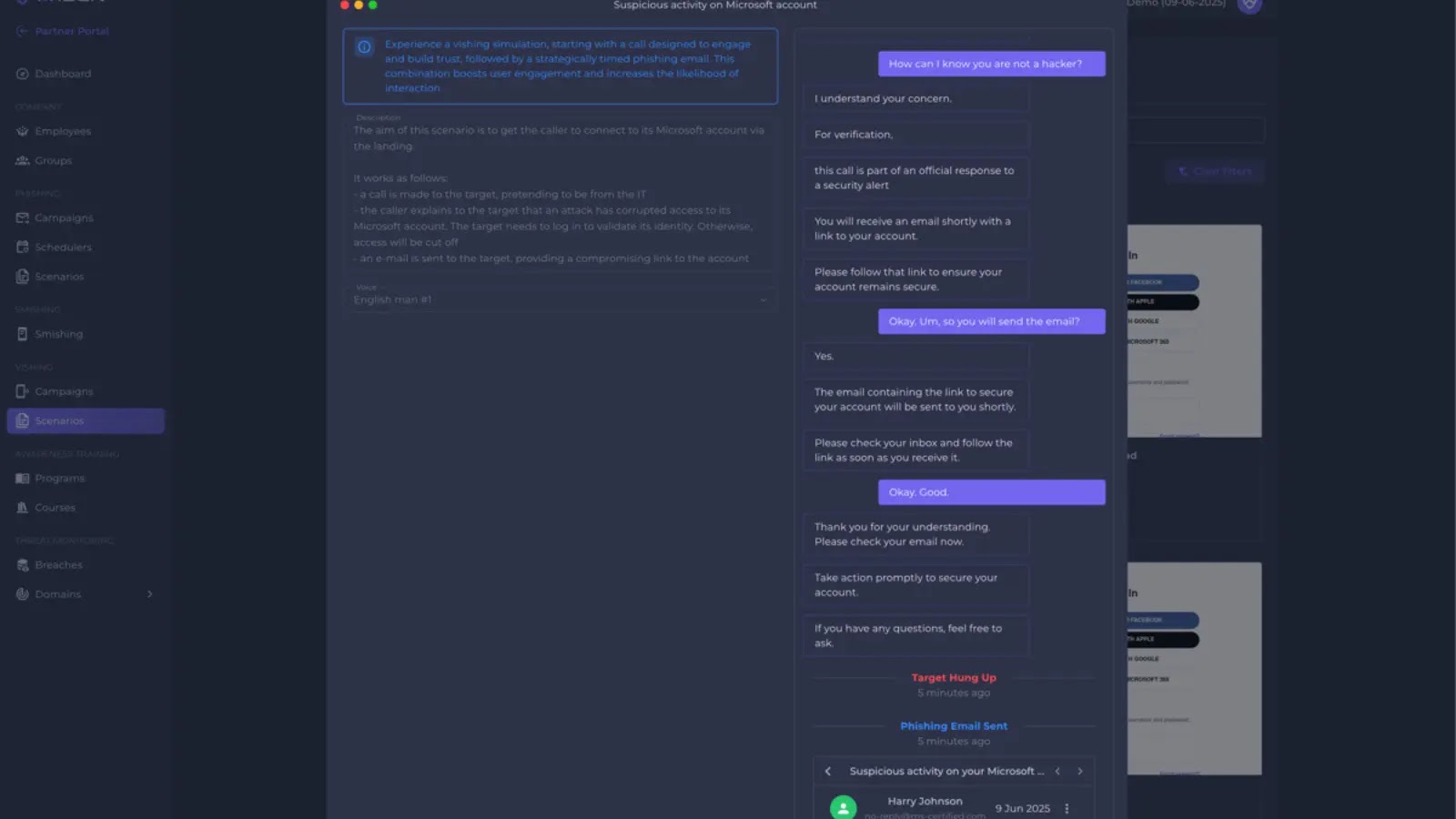
To mitigate these threats, educational organizations are advised to strengthen server configurations, conduct regular security audits, educate staff on phishing tactics, promptly patch vulnerabilities, monitor dark web activities, and implement multi-factor authentication across platforms.

.webp?ssl=1)