Cybersecurity experts have identified a new variant of the notorious Mirai botnet, labeled as xlabs_v1, which targets devices exposed to the internet via the Android Debug Bridge (ADB). This botnet is engineered to commandeer such devices for executing distributed denial-of-service (DDoS) attacks.
Exploiting ADB Vulnerabilities
Hunt.io researchers discovered this botnet after accessing an unsecured directory on a server located in the Netherlands, specified by the IP address “176.65.139[.]44”. This discovery highlighted the botnet’s ability to support a variety of attack methods, including 21 flood variants across TCP, UDP, and raw protocols. Notable among these are RakNet and OpenVPN-shaped UDP floods, designed to bypass standard DDoS protections.
The xlabs_v1 botnet uniquely targets Android devices with an exposed ADB service on TCP port 5555. Devices like Android TV boxes, set-top boxes, and smart TVs with ADB enabled by default are particularly vulnerable to this threat.
Technical Aspects and Attack Strategy
The malware not only utilizes an Android APK named “boot.apk” but also supports multiple architectures such as ARM, MIPS, x86-64, and ARC. This indicates its potential to compromise residential routers and various IoT devices. Once a device is infected, it communicates with the operator’s control panel at “xlabslover[.]lol” to initiate DDoS attacks, particularly against gaming servers.
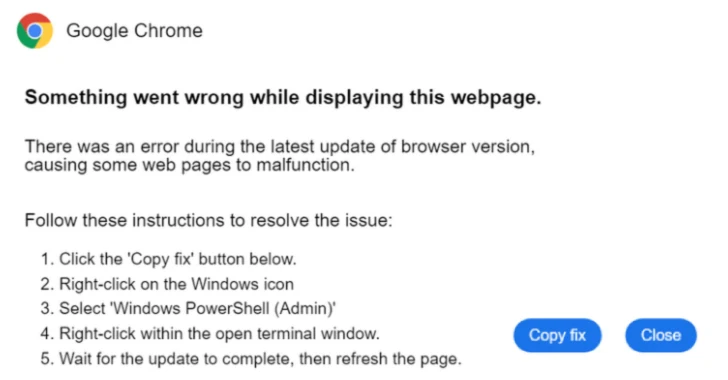
The malware is delivered through ADB-shell commands, specifically targeting ARM hardware with ADB enabled. It opens 8,192 parallel TCP connections to the closest Speedtest server to measure bandwidth, classifying each compromised device into a pricing tier for customers of the DDoS-for-hire service.
Operational Characteristics and Threat Actor
A distinctive feature of xlabs_v1 is its lack of a persistence mechanism. After relaying bandwidth data, the botnet exits, requiring re-infection for sustained control. This suggests that the operator prioritizes bandwidth assessment over continuous device control.
The botnet includes a “killer” component to eliminate rival malware, maximizing its use of available bandwidth for its own attacks. While the identity of the threat actor remains unknown, the name “Tadashi” is embedded in the botnet’s code.
Additional findings revealed a Monero cryptocurrency mining toolkit on a related server, although it’s unclear if the same actor is responsible for both activities.
According to Hunt.io, xlabs_v1 is positioned as a mid-tier commercial threat. It competes on cost and attack variety rather than on technical complexity. Its primary targets are consumer IoT devices, residential routers, and small-scale gaming servers.
Implications for Cybersecurity
The emergence of xlabs_v1 underscores the persistent threat of cyberattacks on the gaming industry and other sectors reliant on network infrastructure. Darktrace reported similar incidents involving misconfigured Jenkins instances used to deploy DDoS botnets, highlighting the need for robust security measures.
This development serves as a critical reminder for operators of game servers and IoT devices to implement effective defenses against such evolving threats.