A complicated Chinese language menace actor marketing campaign has emerged as one of the persistent malware distribution operations focusing on Chinese language-speaking communities worldwide.
Since June 2023, this ongoing marketing campaign has established an in depth infrastructure comprising greater than 2,800 malicious domains particularly designed to ship Home windows-targeted malware to people and entities each inside China and internationally.
The menace actors function with outstanding consistency throughout Chinese language enterprise hours, using a multi-faceted strategy that leverages faux software obtain websites, misleading software program replace prompts, and spoofed login pages for standard providers.
Their targets embrace customers of promoting functions, enterprise gross sales platforms, and cryptocurrency-related providers, demonstrating a transparent deal with financially motivated cybercrime and credential theft operations.
The marketing campaign’s scope and persistence have drawn vital consideration from safety researchers.
DomainTools analysts recognized that as of June 2025, 266 domains from over 850 created since December 2024 remained actively distributing malware, highlighting the operation’s sustained infrastructure and steady evolution.
Latest operational modifications point out the menace actors are adapting to defensive measures by implementing anti-automation code, decreasing reliance on monitoring providers like Baidu and Fb, and distributing their infrastructure throughout extra servers to keep away from detection.
These modifications recommend a mature understanding of cybersecurity countermeasures and a dedication to sustaining operational effectiveness.
Multi-Stage An infection Mechanism
The malware supply course of demonstrates subtle technical implementation by a multi-stage an infection chain.
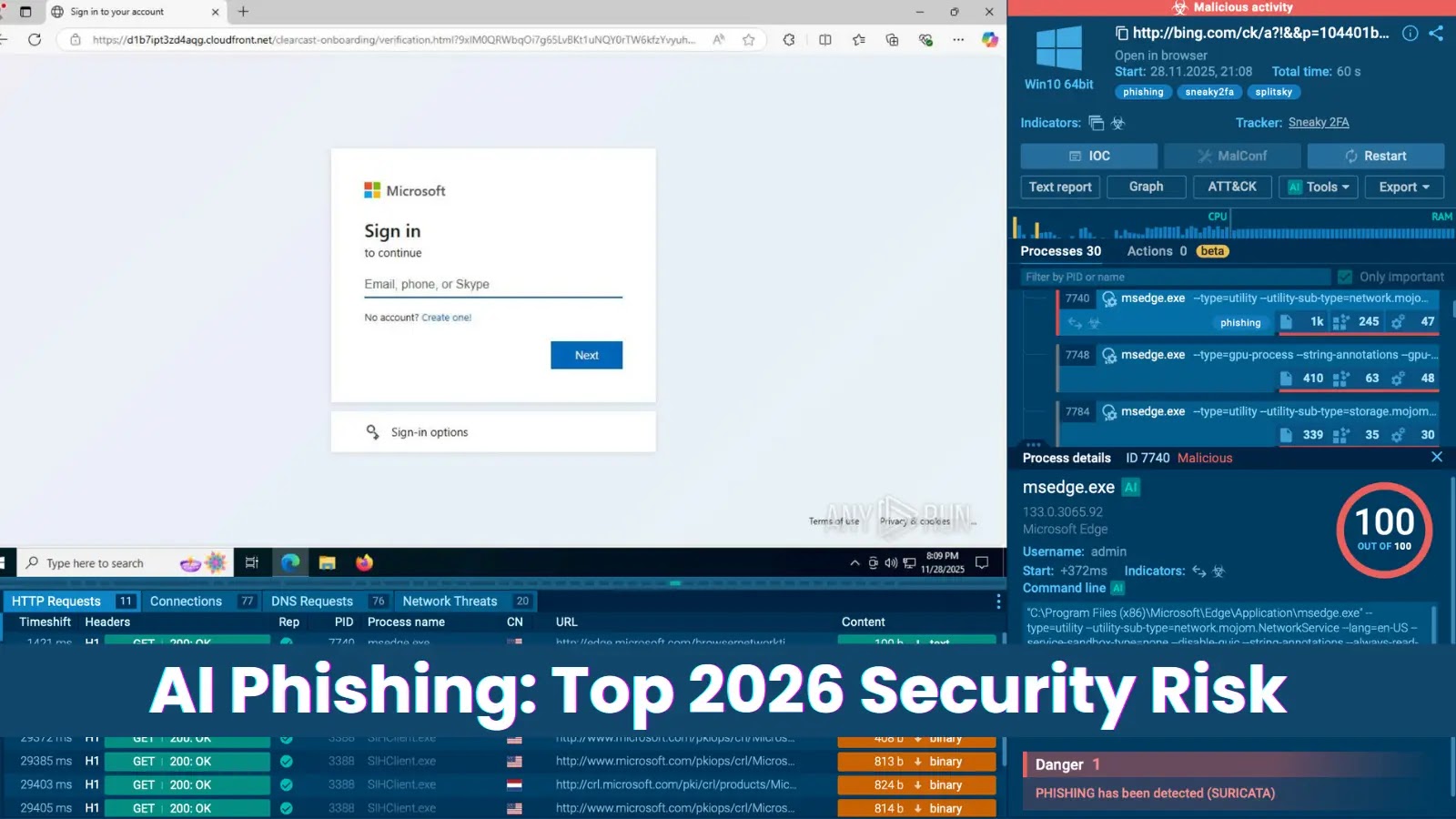
Pretend Gmail Login (Supply – Domaintools)
Evaluation of the area googeyxvot[.]high reveals the actors’ use of JavaScript obfuscation to hide obtain URLs and set off faux browser compatibility errors that immediate malicious updates.
A number of JavaScript information are employed to obfuscate the obtain URL (Supply – Domaintools)
When customers work together with these misleading websites, they obtain a ZIP file containing an MSI installer.
The file flashcenter_pl_xr_rb_165892.19.zip (SHA256: 7705ac81e004546b7dacf47531b830e31d3113e217adeef1f8dd6ea6f4b8e59b) incorporates the executable svchost.13.exe, which features as a downloader element.
This downloader retrieves encrypted payloads from command-and-control servers, particularly from URLs like https://ffsup-s42.oduuu[.]com/uploadspercent2F4398percent2F2025percent2F06percent2F617.txt.
The ultimate payload employs XOR encryption with the important thing 0x25 to decode and execute the embedded PE file, demonstrating the marketing campaign’s technical sophistication in evading detection whereas sustaining operational simplicity for widespread deployment throughout their intensive area infrastructure.
Enhance detection, scale back alert fatigue, speed up response; all with an interactive sandbox constructed for safety groups -> Attempt ANY.RUN Now