On December 29, 2025, Poland confronted a coordinated assault focusing on greater than 30 wind and photo voltaic farms, alongside a big mixed warmth and energy plant and a producing facility.
The assaults occurred throughout extreme winter climate, when temperatures dropped and snowstorms threatened the nation’s vitality stability.
All operations had purely damaging intentions, designed to break crucial infrastructure slightly than steal info.
These coordinated strikes symbolize the primary documented damaging operation by a classy assault group, marking a major escalation in threats towards European vitality infrastructure.
The assault focused energy substations serving as connection factors between renewable vitality sources and the distribution community. Industrial automation gadgets at these areas turned prime goals for the attackers.
These programs included distant terminal items managing telecontrol operations, human-machine interfaces displaying facility standing, safety relays guarding towards electrical harm, and communication gear akin to routers and community switches.
After establishing entry to inner networks, attackers performed detailed reconnaissance earlier than executing their damaging plan by broken firmware and custom-built wiper malware on December 29 morning.
Communication channels between farms and the distribution system operator had been disrupted, although electrical energy era continued unaffected.
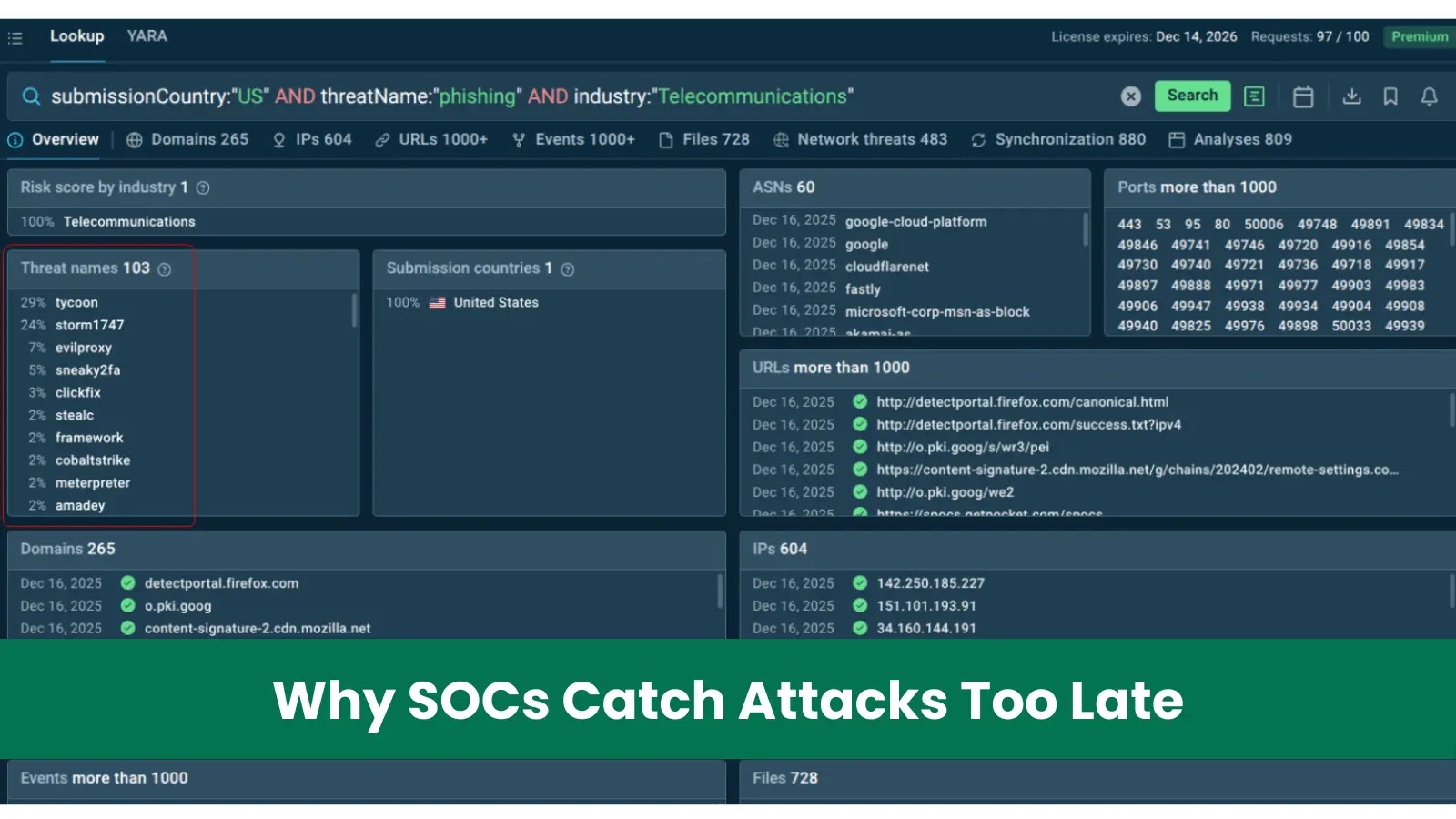
Cert.pl analysts recognized the assault infrastructure used within the operation, revealing vital overlap with infrastructure related to menace teams often known as “Static Tundra” by Cisco, “Berserk Bear” by CrowdStrike, “Ghost Blizzard” by Microsoft, and “Dragonfly” by Symantec.
These researchers famous the attackers demonstrated robust capabilities towards industrial gadgets and historic deal with vitality sectors.
Public evaluation indicated this represented the primary damaging marketing campaign publicly attributed to this exercise cluster, signaling an vital tactical shift of their operations.
Wiper Malware Deployment and An infection Mechanism
The attackers employed similar wiper malware throughout a number of targets, deploying custom-built damaging software program after gaining privileged entry by extended infrastructure infiltration.
The malware’s operation centered on irreversible knowledge destruction throughout focused networks.
After establishing footholds by compromised accounts and stolen operational info, attackers ready partially automated assault sequences prepared for simultaneous activation.
When deployed towards the mixed warmth and energy plant, the malware’s execution was blocked by endpoint detection and response know-how already operating on the group’s programs.
The manufacturing sector firm confronted related coordinated assault, although the precise goal differed from vitality targets.
This assault sample demonstrated subtle planning, with the malware serving as the ultimate payload following intensive preparation and community reconnaissance throughout a number of weeks of covert presence inside goal environments.
Observe us on Google Information, LinkedIn, and X to Get Extra On the spot Updates, Set CSN as a Most popular Supply in Google.