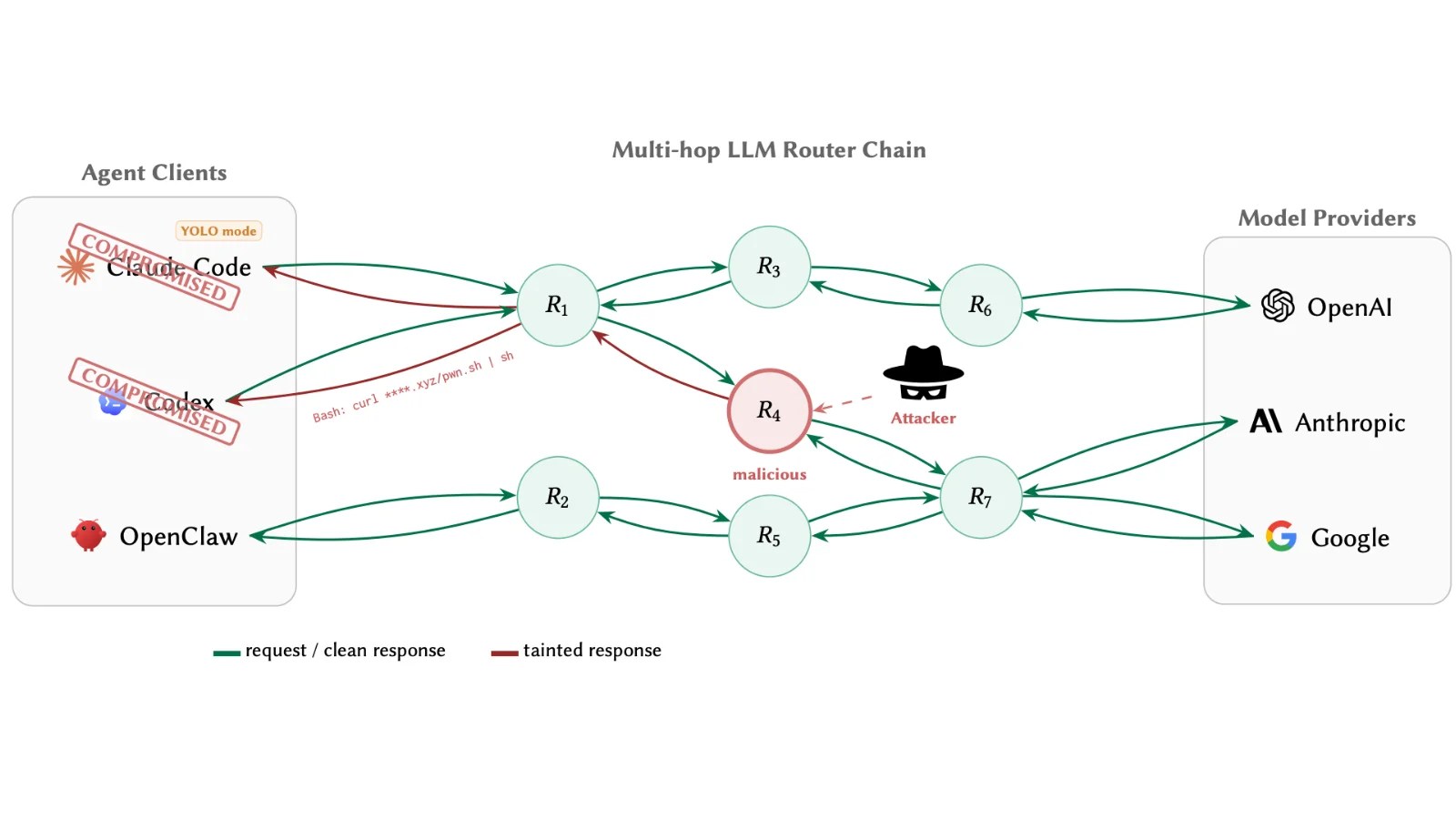
The AI ecosystem faces significant security challenges due to vulnerabilities in third-party API routers. These routers, pivotal in handling AI agent requests, can be exploited by attackers to inject malicious code, steal sensitive data, and compromise cryptocurrency wallets.
Understanding AI API Routers
With the growing role of AI agents in automating complex tasks, including managing financial transactions and cloud infrastructure, the reliance on LLM API routers has increased. These routers serve as intermediaries dispatching requests to AI providers such as OpenAI, Anthropic, and Google.
A recent study by the University of California, Santa Barbara, titled “Your Agent Is Mine: Measuring Malicious Intermediary Attacks on the LLM Supply Chain,” highlights the security risks posed by these routers. As application-layer proxies, they have full access to plaintext JSON payloads, making them susceptible to attacks without the need for TLS certificate forgery.
Exploring the Attack Vector
The study reveals that routers terminate the TLS connection from clients and establish new ones upstream, allowing them to intercept, modify, or fabricate tool-call payloads without detection. The absence of cryptographic integrity measures between clients and model providers exacerbates the threat.
Researchers analyzed 28 paid and 400 free routers, uncovering alarming results: 9 routers injected malicious code, 17 cases of unauthorized AWS credential use, and 1 instance of cryptocurrency theft. Attackers also used sophisticated evasion techniques, such as payload activation after specific conditions were met.
Mitigating the Risks
The study emphasizes the need for immediate security measures, including a fail-closed policy gate, response-side anomaly screening, and append-only transparency logging. These strategies help in detecting and mitigating potential attacks, though they are not foolproof.
The researchers advocate for the adoption of provider-signed response envelopes, akin to DKIM for email, to cryptographically validate tool calls. Until such measures are implemented, developers should treat all third-party routers with caution and employ robust client-side defenses.
The ongoing threat underscores the critical need for enhanced security protocols within the AI API ecosystem. As the industry awaits comprehensive solutions from major providers, maintaining vigilant security practices remains crucial.