A vital authorization bypass vulnerability in ASUS Armoury Crate permits attackers to realize system-level privileges on Home windows machines via a complicated onerous hyperlink manipulation approach.
The vulnerability, tracked as CVE-2025-3464 with a CVSS rating of 8.8, impacts the favored gaming software program’s AsIO3.sys driver and was patched by ASUS on June 16, 2025.
Authentication Bypass By way of Laborious Hyperlink Manipulation
The vulnerability uncovered by Cisco Talos researchers exploits a basic flaw in how the AsIO3.sys driver validates approved purposes. Underneath regular circumstances, the driving force restricts entry to solely the reputable AsusCertService.exe by evaluating SHA-256 hashes of requesting processes.
The driving force performs this examine utilizing the ZwQueryInformationProcess perform to retrieve the method picture path, then calculates and compares SHA-256 hashes towards a hardcoded worth saved within the world variable g_sha256Hash.
This authentication mechanism might be circumvented utilizing Home windows onerous hyperlinks. The assault includes creating a tough hyperlink that originally factors to a malicious executable, then switching the hyperlink vacation spot to the reputable AsusCertService.exe after the method begins however earlier than the authentication examine happens.
When the driving force queries the method data, it receives the trail to the onerous hyperlink pointing to the approved ASUS service, successfully bypassing the safety validation.
The exploitation course of includes particular timing manipulation of onerous hyperlinks. Attackers first create a tough hyperlink utilizing the command mklink /h core.exe TestCon2.exe, launch their malicious utility, then swap the hyperlink vacation spot with mklink /h core.exe AsusCertService.exe earlier than the driving force performs its authentication examine.
This method leverages the Time-of-Test-Time-of-Use (TOCTOU) race situation within the driver’s validation logic.
As soon as authenticated, the compromised utility good points entry to the Asusgio3 system, which exposes vital system functionalities together with mapping arbitrary bodily reminiscence addresses into the digital tackle house of the calling course of, offering entry to I/O port communication directions, and enabling learn/write operations to Mannequin Particular Register (MSR) values.
These capabilities basically grant attackers kernel-level entry to the system, permitting full system compromise.
Danger FactorsDetailsAffected ProductsASUS Armoury Crate v5.9.13.0 (AsIO3.sys driver)ImpactPrivilege escalationExploit Prerequisites1. Native consumer access2. Laborious hyperlink creation permissions3. Weak driver installedCVSS 3.1 Score8.8 (Excessive)
Patch Obtainable
ASUS responded to the disclosure timeline appropriately, with Cisco Talos reporting the vulnerability on February 18, 2025, adopted by ASUS releasing a patch on June 16, 2025.
The vulnerability was publicly disclosed the identical day because the patch launch, following accountable disclosure practices.
The vulnerability impacts ASUS Armoury Crate model 5.9.13.0, and customers are strongly suggested to replace to the newest patched model instantly.
This discovery highlights the continued safety challenges in gaming software program and the significance of correct authorization mechanisms in kernel-level drivers, notably these managing {hardware} entry and system-level operations.
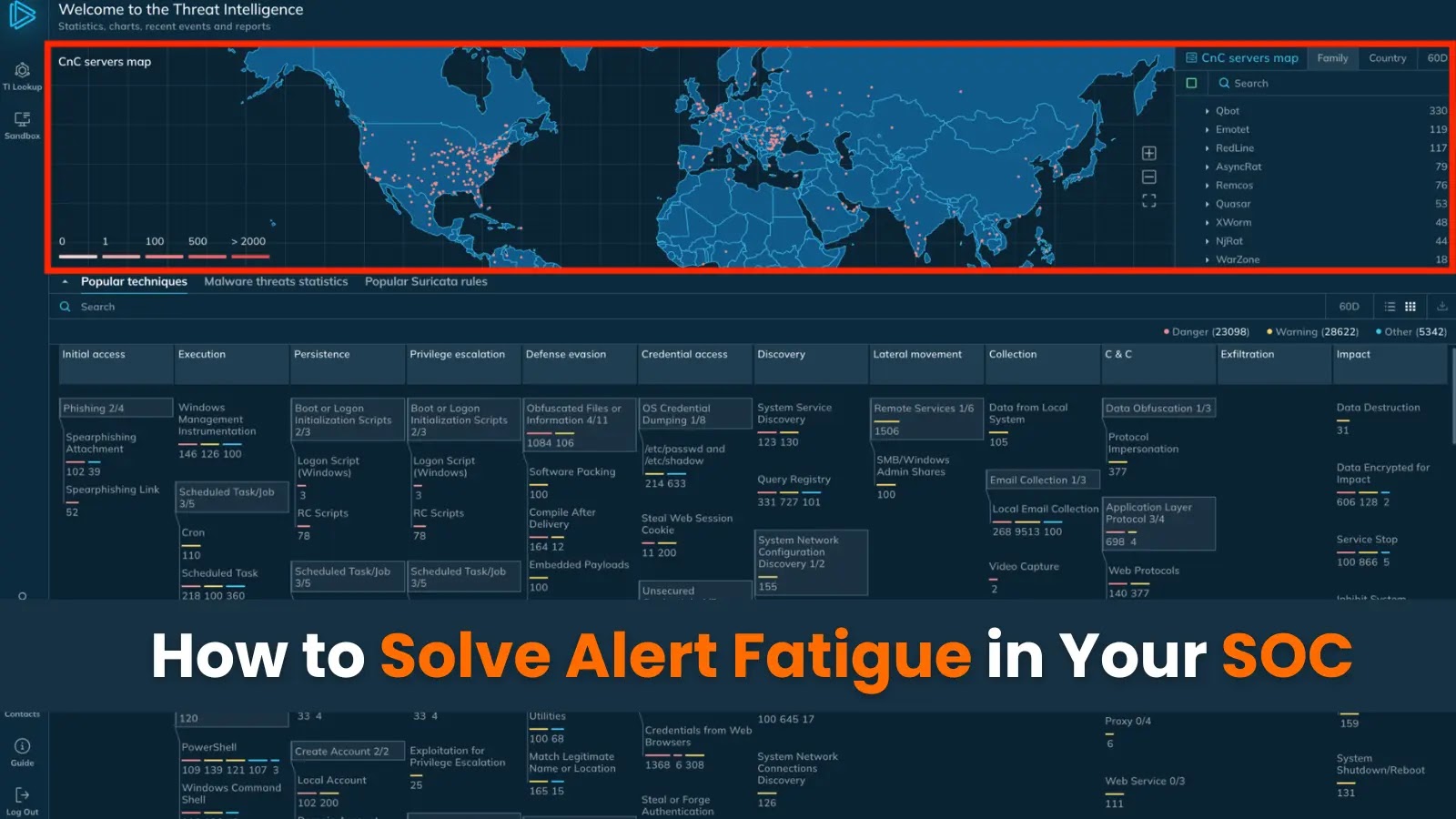
Automate menace response with ANY.RUN’s TI Feeds—Enrich alerts and block malicious IPs throughout all endpoints -> Request full entry