Bragg Gaming Group has confirmed a major cybersecurity incident that compromised the corporate’s inner IT infrastructure early Saturday morning, August 16, 2025.
The net gaming know-how supplier found unauthorized community intrusion makes an attempt that efficiently breached their safety perimeter, prompting quick activation of incident response protocols.
Key Takeaways1. Bragg Gaming Group skilled a cybersecurity breach with hackers accessing the corporate’s inner IT techniques.2. Preliminary investigations point out no buyer private info or cost information was compromised.3. The corporate has engaged quick containment protocols.
Inner Community Breach
Preliminary forensic evaluation performed by Bragg’s safety workforce signifies that risk actors gained unauthorized entry to the corporate’s inner pc setting by way of what seems to be a focused assault vector.
The breach primarily affected inner techniques inside Bragg’s community infrastructure, although the corporate’s preliminary investigation suggests the assault remained contained inside their company IT setting.
Safety specialists retained by Bragg are presently conducting complete community visitors evaluation and system log opinions to find out the precise methodology of intrusion.
The corporate has applied quick containment measures, together with community segmentation protocols and enhanced monitoring of all information flows throughout its Distant Video games Server (RGS) know-how platform.
Vital gaming infrastructure, together with the Bragg Hub content material supply platform and Participant Account Administration (PAM) techniques, underwent quick safety audits to make sure operational integrity.
Bragg has deployed a multi-layered incident response technique, participating unbiased cybersecurity specialists to conduct thorough vulnerability assessments and implement further safety hardening measures.
The corporate’s safety operations heart has been positioned on excessive alert, with steady monitoring protocols activated throughout all community endpoints and server clusters.
Regardless of the safety breach, Bragg confirmed that no buyer private info or cost information seems to have been compromised through the incident.
The corporate’s information encryption protocols and entry management mechanisms apparently prevented unauthorized information exfiltration from customer-facing techniques.
All gaming operations throughout Bragg’s regulated markets, together with their iCasino and sportsbook platforms, stay totally operational with no service disruptions reported.
The corporate has initiated necessary safety consciousness coaching for all personnel and is conducting complete penetration testing throughout its total know-how stack.
The swift response to the cybersecurity incident demonstrates the corporate’s dedication to sustaining strong safety protocols whereas guaranteeing minimal disruption to its international gaming operations.
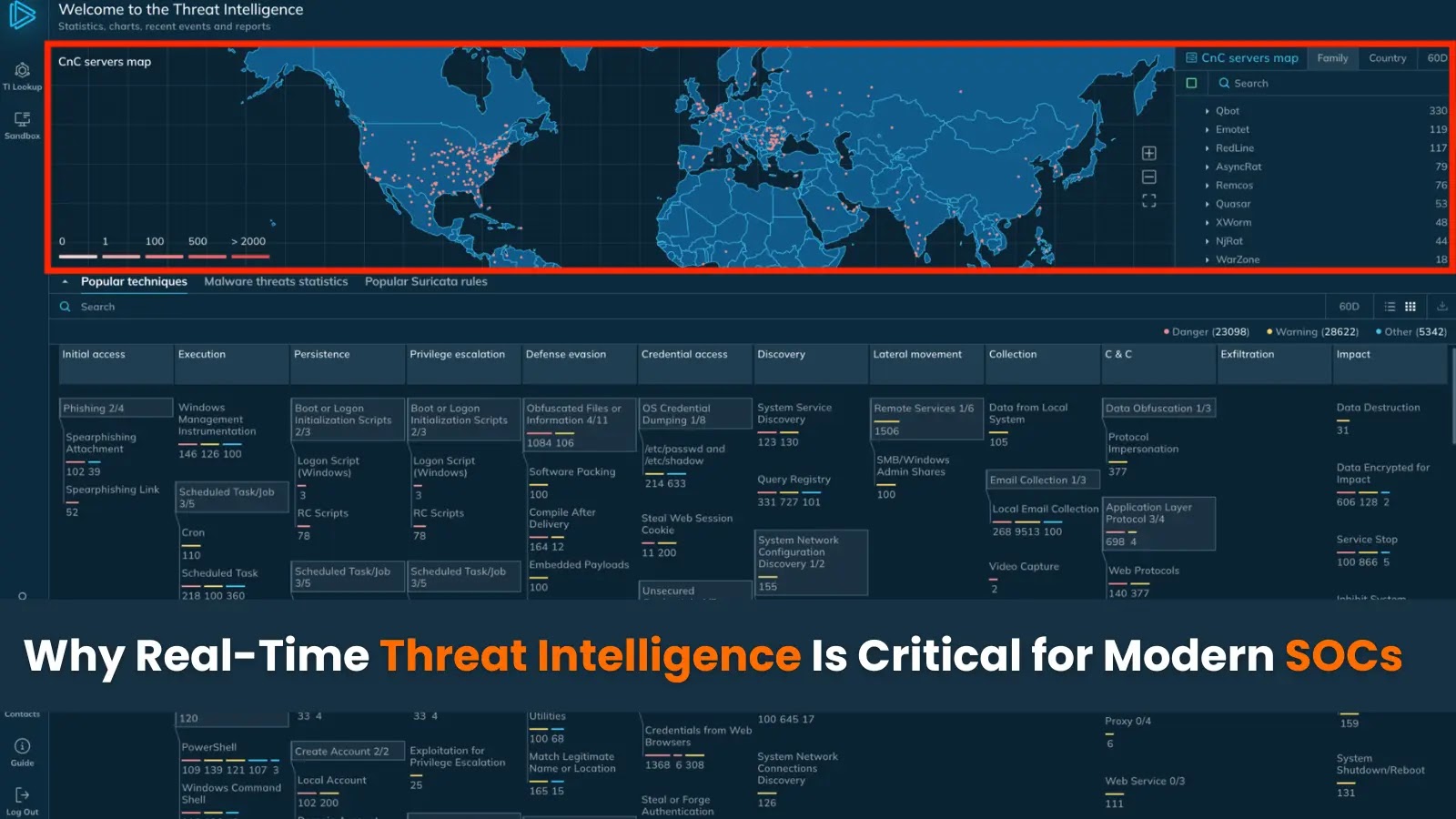
Increase your SOC and assist your workforce shield what you are promoting with free top-notch risk intelligence: Request TI Lookup Premium Trial.