New York, United States, January fifteenth, 2026, CyberNewsWire
BreachLock, a world chief in offensive safety, immediately introduced that its Adversarial Publicity Validation (AEV) resolution now helps autonomous crimson teaming on the software layer, increasing past its preliminary network-layer capabilities launched in early 2025.
BreachLock AEV’s generative AI-powered autonomous crimson teaming engine can now emulate real-world attacker habits on the software layer, capturing how adversaries suppose, pivot, and chain exploits.
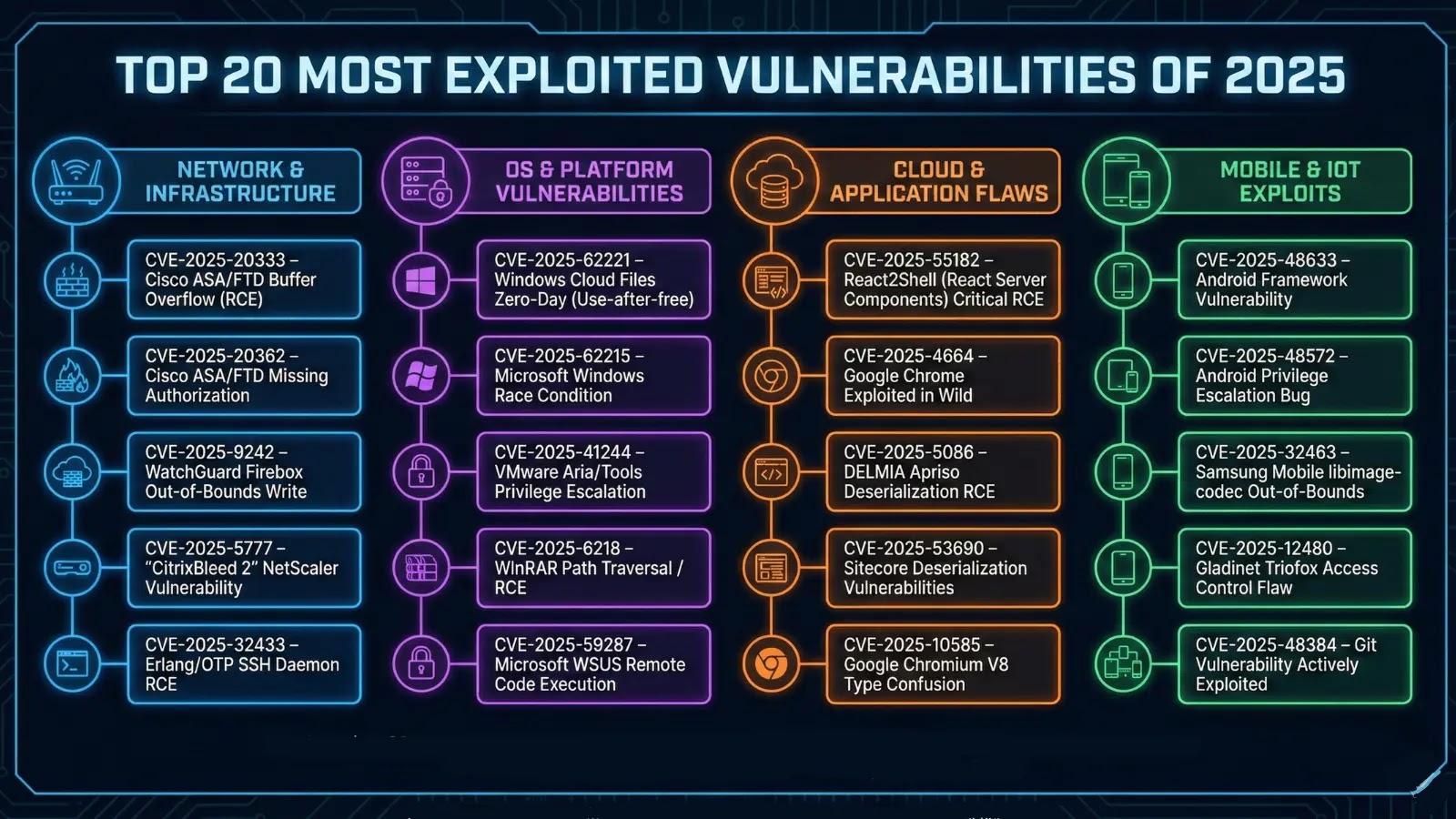
AEV repeatedly validates exploitable weaknesses in functions, together with cross-site scripting (XSS), code injection flaws, OWASP High 10 vulnerabilities, enterprise logic flaws, and complicated exploit paths.
BreachLock AEV goes past merely figuring out theoretical dangers and validates their real-world exploitability and enterprise influence.
These deep contextual insights assist enterprise safety groups scale their protection and scale back important dangers quicker with a sharper concentrate on remediating the validated dangers that pose the best risk to their group.
“Safety groups don’t want extra instruments—they want higher outcomes,” Seemant Sehgal, Founder & CEO of BreachLock, mentioned.
“With agentic autonomous penetration testing for internet functions, we’re pushing the boundaries of what offensive safety can do by repeatedly considering, adapting, and validating threat the way in which actual attackers do. This can be a elementary shift in how organizations measure and enhance their safety posture,” he added.
BreachLock AEV contains an interactive, real-time assault path visualization function, permitting customers to see the place their defenses cross and fail throughout the assault chain. Customers may also obtain detailed, MITRE ATT&CK-aligned PDF studies straight from the BreachLock Unified Platform, making it simpler to speak findings, prioritize remediation, and display compliance.
To study extra about BreachLock AEV, customers can go to BreachLock.com.
About BreachLock
BreachLock is a world chief in offensive safety, delivering scalable and steady safety testing.
Trusted by international enterprises, BreachLock offers human-led and AI-powered Assault Floor Administration, Penetration Testing as a Service (PTaaS), Pink Teaming, and Adversarial Publicity Validation (AEV) options that assist safety groups keep forward of adversaries.
With a mission to make proactive safety the brand new commonplace, BreachLock is shaping the way forward for cybersecurity by automation, data-driven intelligence, and expert-driven execution.
Contact
Advertising Communications Supervisor
Megan Charrois
BreachLock