A new cybersecurity threat has emerged with the introduction of CrystalX, a Malware-as-a-Service (MaaS) platform, which is being marketed through private Telegram channels. This sophisticated toolset combines a remote access trojan (RAT), credential stealer, and spyware, among other features, making it a formidable package for cybercriminals.
The Evolution of CrystalX Malware
CrystalX was first detected in March 2026, evidencing a trend towards subscription-based malware services that offer complex attack capabilities. Originating in January 2026, it is an evolved form of a tool called Webcrystal RAT which was initially promoted on a private Telegram group for RAT developers.
Observers noted similarities between CrystalX’s initial control panel and a known tool, WebRAT, which led to criticisms of it being a mere copy. Consequently, the developer rebranded it as CrystalX RAT, enhancing its marketing via Telegram and YouTube with interactive features like access key draws and polls.
Features and Impact of CrystalX
According to Securelist analysts, CrystalX boasts a feature set surpassing most commercial RATs. It offers various subscription tiers, providing access to capabilities such as file exfiltration and live screen control. Notably, it combines espionage functions with prank commands, making it a unique threat in the MaaS market.
The malware’s impact is growing, with numerous infections reported, primarily in Russia. However, CrystalX’s lack of geographic restrictions allows subscribers to target victims globally. Kaspersky identifies the threat with signatures like Backdoor.Win64.CrystalX and Trojan.Win64.Agent, indicating ongoing enhancements and a likely increase in its user base.
Detection Evasion and Mitigation
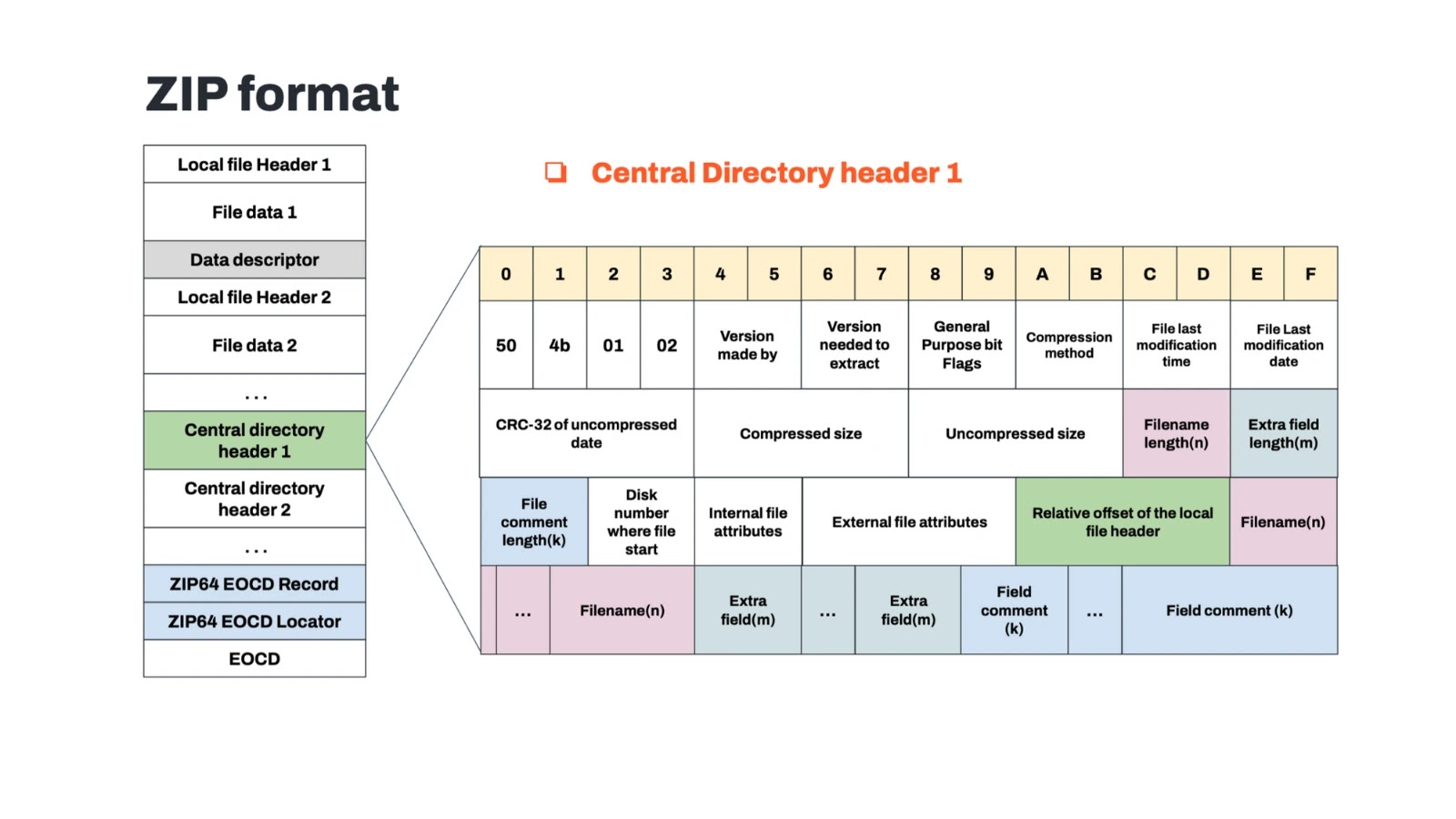
CrystalX employs advanced anti-detection strategies. It compresses and encrypts its code, complicating static analysis. Its auto-builder includes options to configure anti-analysis measures and geoblocking by country. Moreover, it performs checks to detect analysis environments and disables security tools during execution.
Once operational, CrystalX connects to command-and-control servers using specific WebSocket URLs. Organizations are advised to block domains like webcrystal.lol and monitor for suspicious outbound connections. Regular updates to endpoint protection tools are crucial for defending against such threats.
Stay informed on developments in cybersecurity by following us on Google News, LinkedIn, and X. Set CSN as a preferred source in Google for instant updates.