ANY.RUN, the interactive malware evaluation platform, has wrapped up 2025 with spectacular progress figures and important contributions to the cybersecurity neighborhood.
The corporate’s annual report reveals how its world consumer base collectively spent over 400,000 hours analyzing threats—equal to greater than 45 years of steady analysis.
The platform processed 5.7 million analyses throughout 195 nations all year long, uncovering 1.1 million threats within the course of. The consumer neighborhood expanded to over 500,000, with 81,000 new members becoming a member of in 2025.
Notably, 74 of the Fortune 100 firms utilized ANY.RUN’s sandbox for his or her safety operations, with probably the most lively customers primarily based in the USA, Germany, the UK, and India.
Platform Evolution and New Capabilities
ANY.RUN launched substantial updates to its Interactive Sandbox in 2025, increasing evaluation capabilities past conventional Home windows environments.
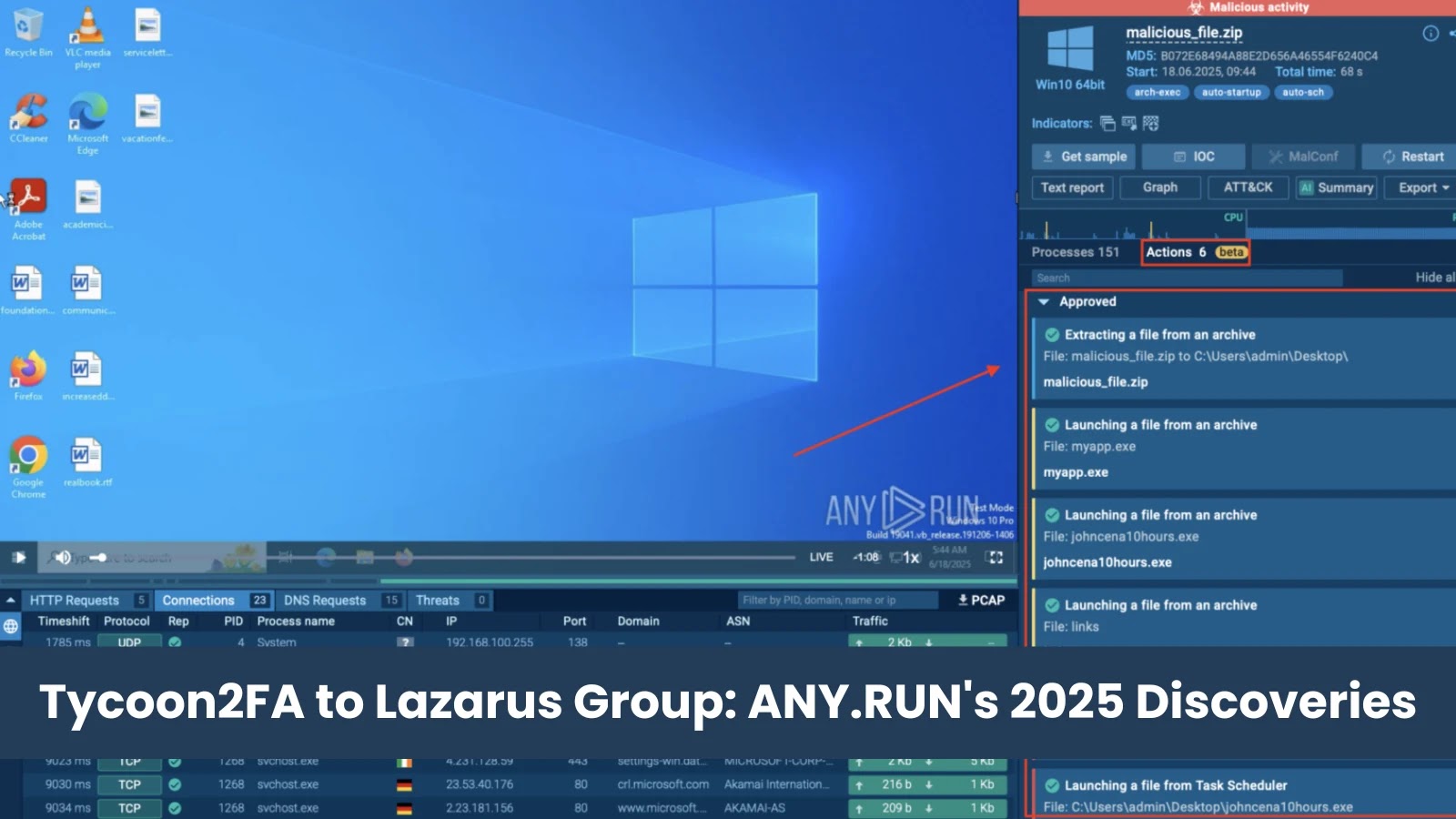
Detonation Actions displayed inside ANY.RUN sandbox
The addition of Android help enabled safety groups to investigate APK information in digital machines that carefully replicate actual Android units—a well timed enhancement given the surge in cell threats all year long.
The platform additionally added Linux Debian OS help, permitting analysts to detonate ARM-based threats concentrating on IoT units and different ARM methods. These expansions made the sandbox extra versatile for investigating various menace landscapes.
To streamline the evaluation course of, ANY.RUN launched Detonation Actions, which give guided hints to assist analysts uncover hidden threats extra effectively.
The platform additionally launched AI Sigma Guidelines, automating probably the most time-consuming points of detection work by producing deployment-ready guidelines for SIEM, SOAR, and EDR methods.
Menace Intelligence Growth
ANY.RUN’s Menace Intelligence Lookup noticed practically 195,000 requests in 2025, with Tycoon2FA rising as each probably the most searched and most lively menace.
Trade & geo menace panorama information for the Tycoon2FA phishkit
The corporate democratized entry to its menace intelligence by launching a free plan, providing 100% verified context for gratis.
New options like TI Reviews and Trade & Geo Menace Panorama information offered analysts with campaign-specific insights and contextual details about how threats relate to particular sectors and nations.
The Menace Intelligence Feeds product grew by way of STIX/TAXII integration and new connectors, together with partnerships with ThreatQ and main safety platforms.
Detect malware & phishing in beneath a minute => Strive at present
First-to-Detect Discoveries
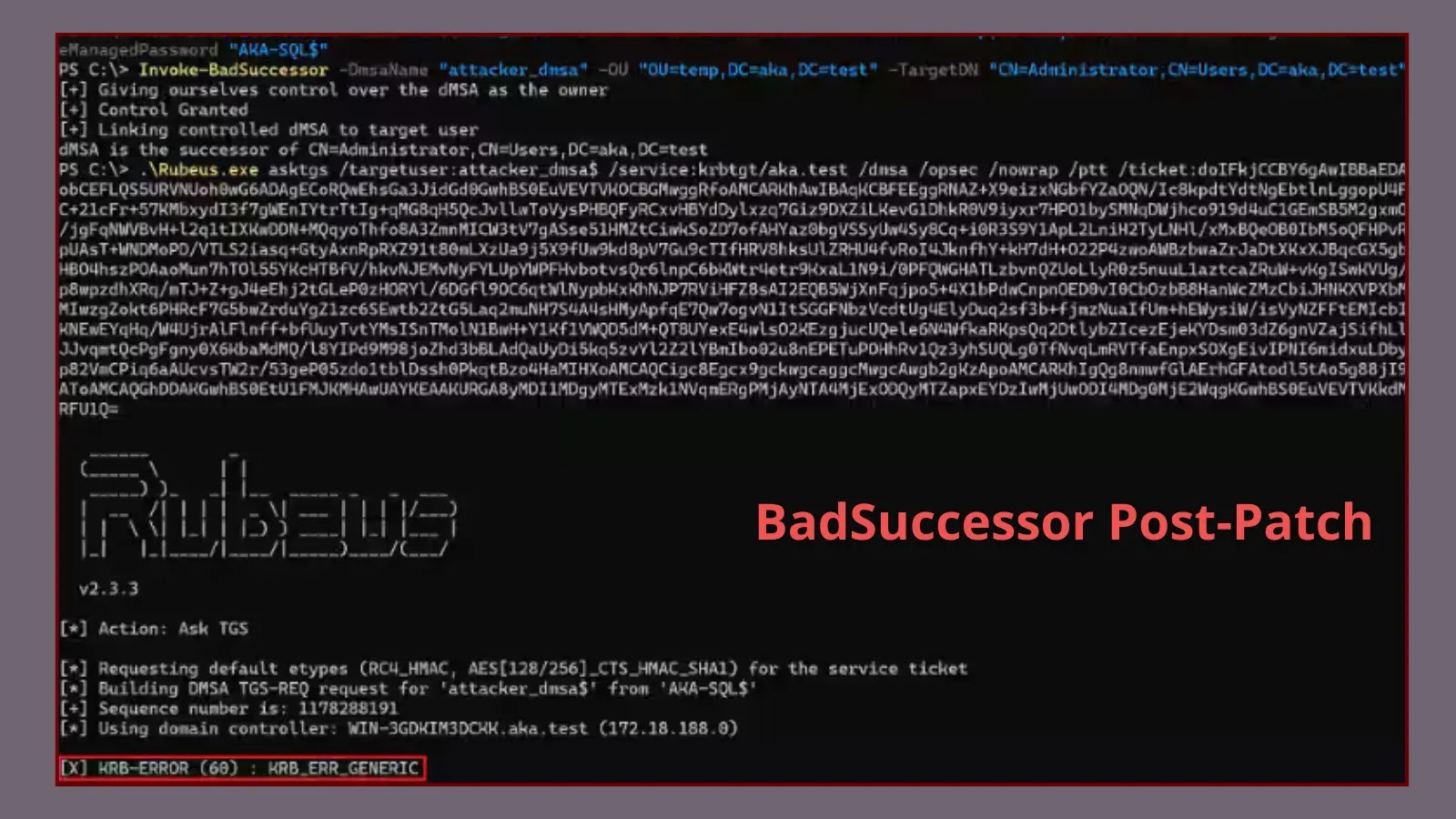
ANY.RUN researchers recognized a number of important threats earlier than the broader safety neighborhood.
Notable discoveries included Salty 2FA, a classy Phishing-as-a-Service framework; Salvador Stealer and Pentagon Stealer, each Android banking malware variants; and Tykit, a credential-stealing malware demonstrating how small protection gaps can result in main impacts.
ANY.RUN’s Sandbox exposes Salty2FA & Tycoon2FA phishing makes an attempt
The yr concluded with detection of a hybrid cross-kit malware combining Salty2FA and Tycoon2FA frameworks.
The corporate additionally printed groundbreaking analysis documenting Lazarus Group’s North Korean IT employees infiltration scheme, capturing actors reside inside managed environments.
Recognition and Integration
ANY.RUN obtained a number of business accolades in 2025, together with gold and silver awards on the Globee Awards, recognition as Finest TI Service on the Cybersecurity Excellence Awards, and the title of Menace Intelligence Firm of 2025 on the CyberSecurity Breakthrough Awards.
The platform expanded its ecosystem by way of SDK launch and ready-to-use integrations with Palo Alto Networks Cortex XSOAR, Microsoft Sentinel, Microsoft Defender, and IBM Safety QRadar SOAR, enabling seamless workflows inside present safety stacks.
Wanting Forward to 2026
ANY.RUN outlined formidable plans for 2026, together with enhanced collaboration options for SOC groups, refined reporting capabilities with AI-powered summaries and auto-generated YARA guidelines, and SSL decryption with out MITM for improved community menace detection.
The corporate may also increase VM help to incorporate macOS and Home windows Server environments for Enterprise customers.
Customers reported measurable enhancements in 2025, with common imply time to detect dropping to fifteen seconds, imply time to reply decreased by 21 minutes, and investigation pace improved in 95% of safety operations facilities.
Detect malware & phishing in beneath a minute => Strive at present