In a significant cyber threat escalation, North Korean threat actor APT37 has launched a new campaign utilizing custom malware to compromise air-gapped systems. Known as ‘Ruby Jumper,’ this campaign showcases sophisticated methods to infiltrate isolated networks, traditionally seen as highly secure.
APT37’s Evolved Tactics
APT37, also identified as ScarCruft or Velvet Chollima, has a history of targeting entities linked to North Korean state interests. The group has previously relied on Chinotto malware for espionage activities. However, Ruby Jumper introduces five new malware components, including RESTLEAF and THUMBSBD, each playing a specific role in a multi-stage attack designed to breach air-gapped systems.
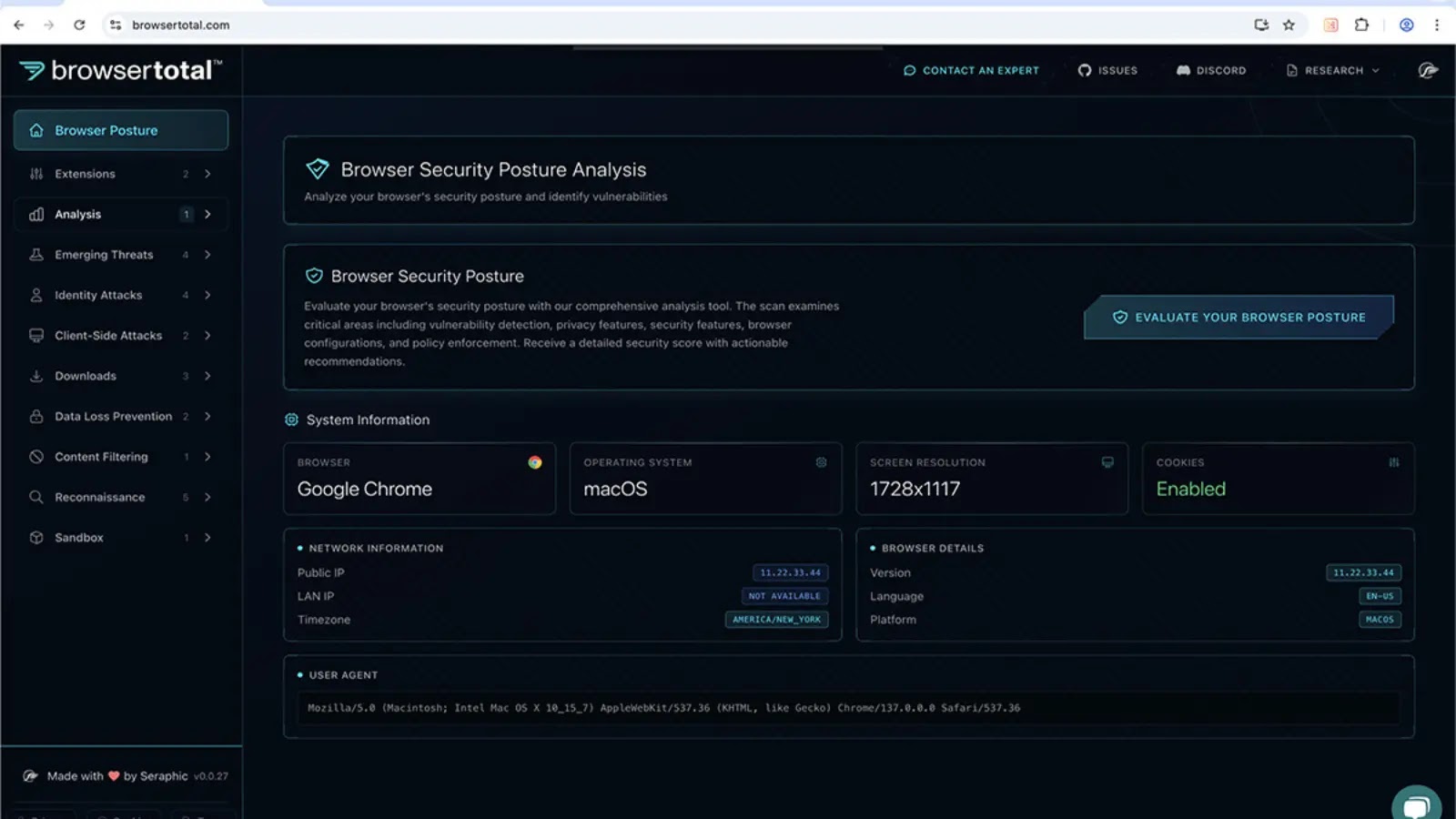
Analysts at Zscaler ThreatLabz uncovered this campaign in late 2025, revealing how APT37 has developed an infection chain capable of crossing network boundaries without internet connectivity. The attack commences with a deceptive Windows shortcut file (LNK), leading to a complex series of payloads.
Air-Gap Breaching Techniques
The Ruby Jumper campaign leverages a decoy document on the Palestine-Israel conflict, suggesting targets among Arabic-speaking individuals. The attack chain progresses from the initial LNK file through RESTLEAF as a first-stage downloader, followed by SNAKEDROPPER and THUMBSBD, which bridge air-gapped hosts via removable media.
THUMBSBD is particularly notable for its ability to turn removable media into covert communication channels, facilitating data exfiltration and command execution on air-gapped machines. The malware utilizes cloud services like Zoho WorkDrive and Google Drive as command-and-control infrastructure, blending malicious activities with regular business operations.
Security Measures and Recommendations
To mitigate this threat, organizations should enforce stringent controls on removable media, especially in high-security environments. Monitoring for unusual scheduled tasks and auditing cloud storage access are also critical. Ensuring vigilance over LNK files in emails and downloads can help identify initial attack vectors.
Security teams are advised to look for indicators such as hidden directories on removable drives and suspicious registry keys. Proactive monitoring of endpoint activity and physical access points is essential to counter this sophisticated threat.
As APT37 continues to evolve its capabilities, organizations managing air-gapped environments must remain vigilant and adopt robust security practices to safeguard against such advanced cyber threats.