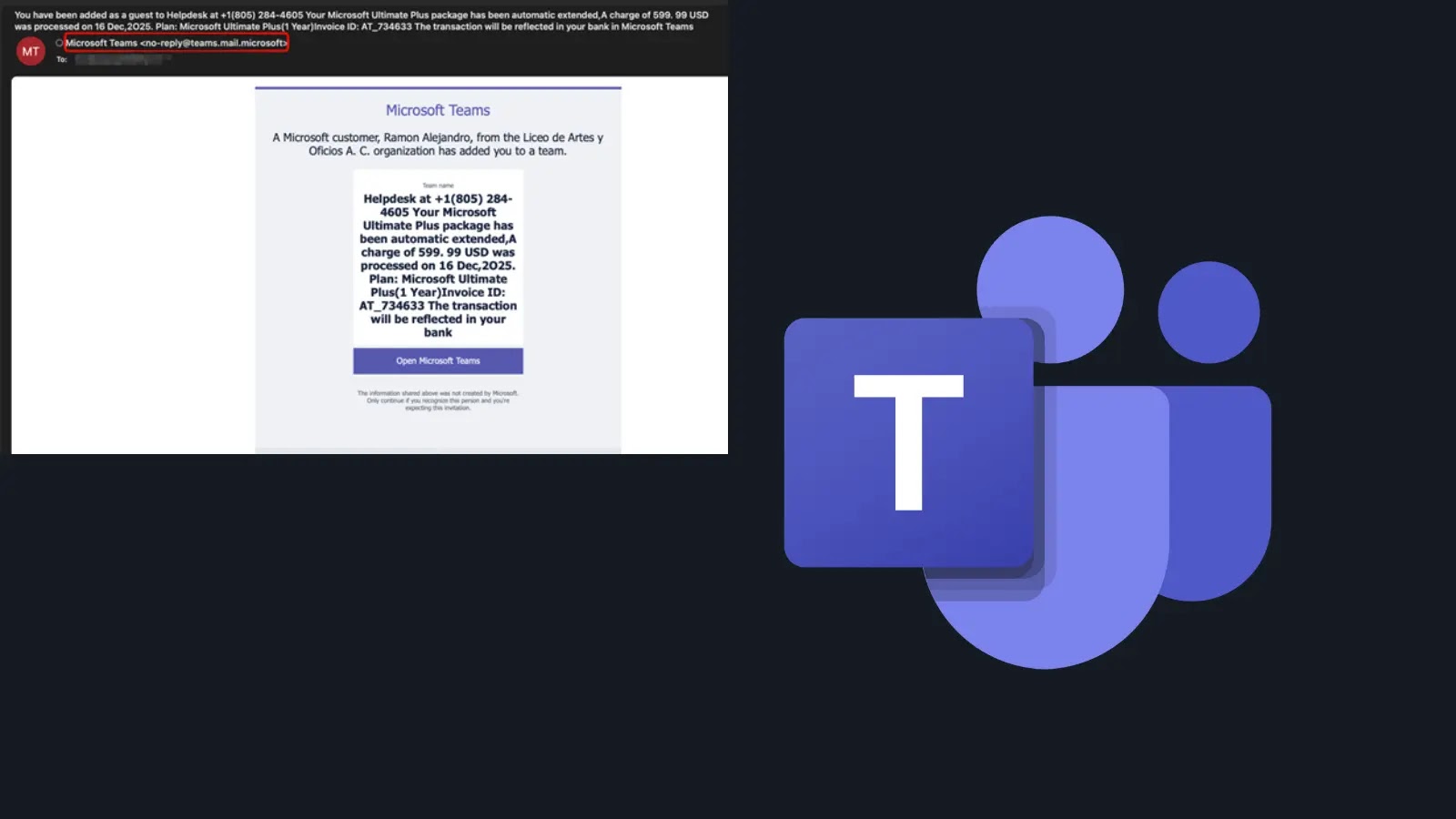
A financially driven cybercriminal group has been quietly executing a malware campaign since late 2023. This operation involves tricking individuals into downloading fake software installers, which clandestinely install remote access trojans (RATs) and Monero cryptocurrency miners.
Known as REF1695, this campaign has been active for over two years, gradually expanding its toolkit while evading detection by most users.
Deceptive Installation Process
The campaign deceives victims by simulating a legitimate software installation process. Users may observe a progress bar or encounter a fake error message indicating a failed installation due to missing system requirements.
By the time the error message is displayed, the malware has already been installed. This tactic prevents users from becoming suspicious of the ongoing background activities.
Technical Analysis and Findings
Elastic Security Labs researchers have traced this operation back to November 2023, identifying multiple versions of the campaign. Each version deployed a unique combination of malicious tools such as PureRAT, CNB Bot, and SilentCryptoMiner.
Despite the variations in payloads, all campaign versions employed consistent packing techniques utilizing Themida, WinLicense, and .NET Reactor. Additionally, they shared overlapping command-and-control (C2) infrastructure, indicating a single operator behind the scenes.
Financial Gains and Evading Detection
In addition to mining Monero, the attacker profits through Cost Per Action (CPA) fraud, redirecting victims to fake registration pages requiring survey completions or service sign-ups. This method has reportedly netted the attacker over 27.88 XMR, equivalent to approximately $9,392.
The campaign’s persistence and adaptability are particularly alarming. Over time, the attacker has updated tools and configurations while exploiting trusted platforms like GitHub to host payloads, all while maintaining the same deceptive installer approach.
Protecting Against Such Threats
The infection begins when a victim starts what appears to be a genuine software installation. The latest campaign build delivers malware as an ISO image, containing a .NET loader and a ReadMe.txt file.
The ReadMe.txt attempts to convince users to bypass Windows SmartScreen warnings, claiming the software is from a small team lacking code-signing capabilities. This often persuades users to proceed with the installation.
Once executed, the loader adds itself and key directories to Microsoft Defender’s exclusion list, rendering it invisible to antivirus tools. It then deploys the CNB Bot implant while presenting a fake error message to keep users unsuspecting.
Users are advised to download software only from official, verified sources and avoid running unsigned executables, even when prompted. Keeping antivirus solutions updated and monitoring for unusual CPU usage or unexpected network activity is crucial. Any anomalies should be immediately reported to IT or security professionals.
Stay informed by following us on Google News, LinkedIn, and X. Set CSN as a preferred source in Google for more instant updates.

.webp?ssl=1)