A surge of counterfeit AI-driven browser extensions has infiltrated over 20,000 enterprise environments, jeopardizing the chat histories of employees who rely on AI tools for professional tasks.
Widespread Installation and Data Compromise
These fraudulent extensions, based on the Chromium platform, were deceptively presented as legitimate AI assistants and amassed nearly 900,000 installations before being detected. They posed as genuine productivity tools while secretly collecting sensitive data.
The extensions particularly targeted users of renowned AI platforms such as ChatGPT and DeepSeek, extracting complete conversation logs, visited URLs, and browsing telemetry from active sessions. Employees frequently using these platforms shared internal codes and strategic plans, all of which were covertly captured and sent to attacker-controlled servers.
Detection and Distribution Tactics
Microsoft Defender analysts uncovered the campaign after detecting unusual outbound connections linked to browser extensions across enterprise systems. Attackers meticulously studied legitimate extensions, including one known as AITOPIA, replicating its branding and user interface, allowing the malicious versions to bypass standard checks.
Distributed via the Chrome Web Store, these extensions exploited its reputation for security. Given that Microsoft Edge supports Chromium-based extensions, a single malicious listing could affect users on both browsers. Automatic downloads on some browsers further extended the campaign’s reach.
Stealthy Data Harvesting Techniques
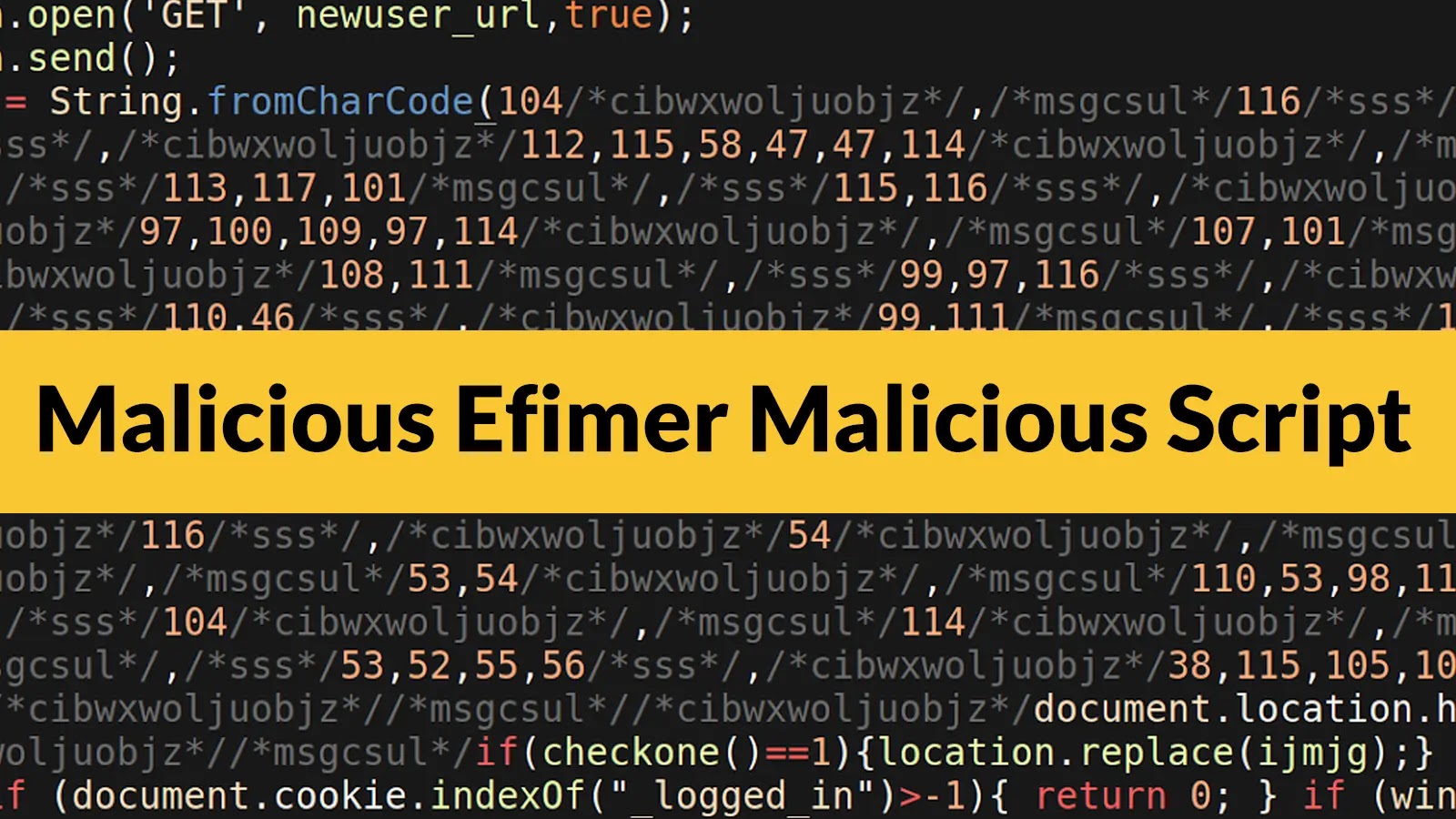
Upon installation, these extensions activated background scripts to log visited URLs and AI chat content without user intervention. The permissions model of Chromium granted access to nearly all pages, including internal corporate sites, enabling extensive data collection.
Data was stored locally in Base64-encoded JSON format and transmitted at set intervals to avoid detection. The extensions used HTTPS POST requests to send data to domains like deepaichats[.]com and chatsaigpt[.]com, blending with regular web traffic.
Preventive Measures for Organizations
Organizations are urged to audit browser extensions across their networks and remove any with unknown IDs, especially those implicated in this campaign. Monitoring outbound POST traffic to suspicious domains can help identify affected devices.
Implementing extension allowlisting through browser management platforms and enhancing network protection to block known command and control endpoints are effective strategies. Educating employees to review and remove unfamiliar extensions is essential for safeguarding sensitive information.
Stay informed with updates by following us on Google News, LinkedIn, and X, and set CSN as a preferred source on Google.