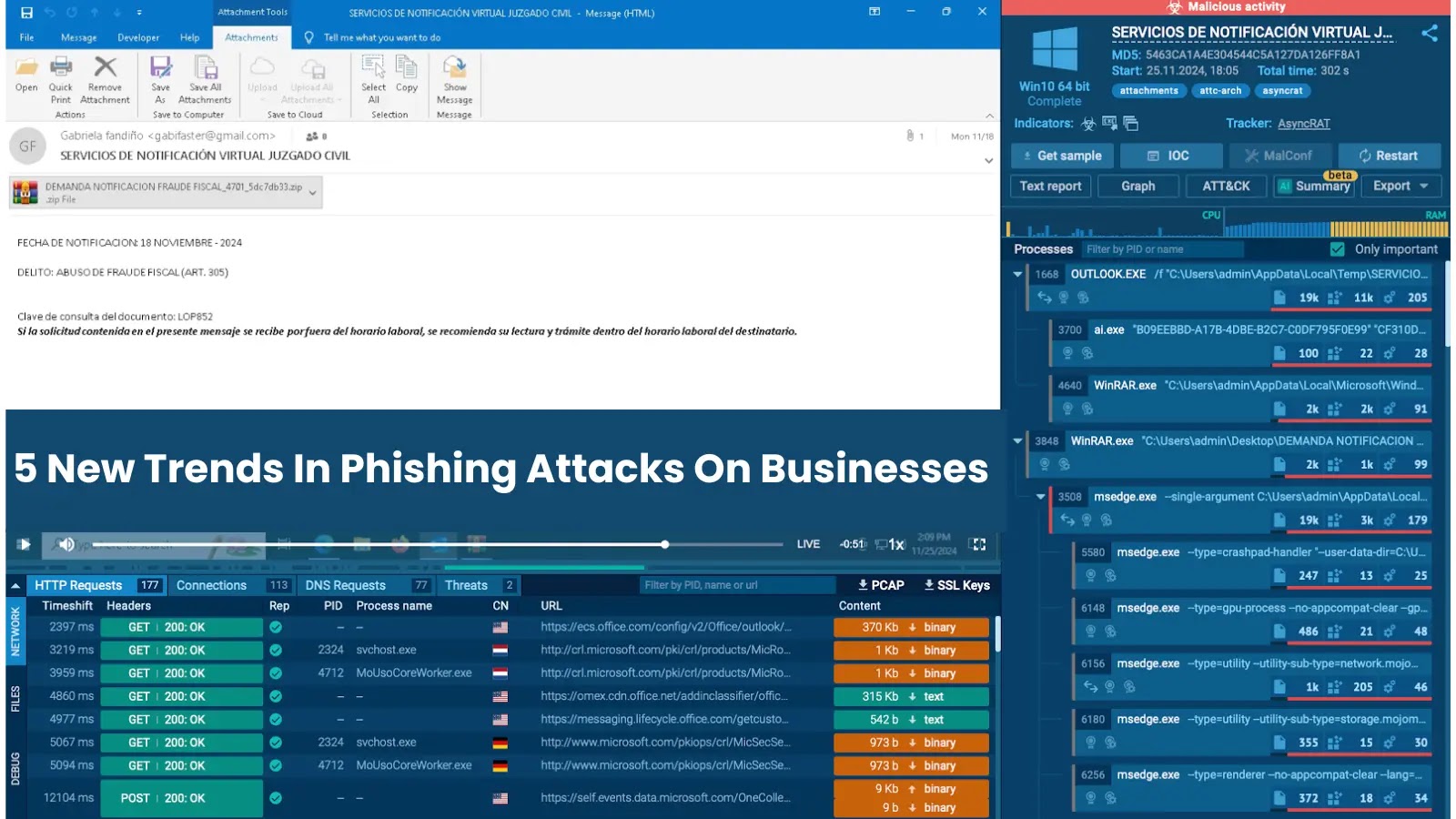
A harmful new malware known as DroidLock is concentrating on Android customers, significantly in Spanish-speaking areas, by way of phishing web sites.
This menace combines ransomware ways with remote-control capabilities, posing a extreme threat to customers of private and company units.
As soon as put in, DroidLock transforms a smartphone right into a hostile endpoint that attackers can manipulate at will, making it a big concern for cellular safety.
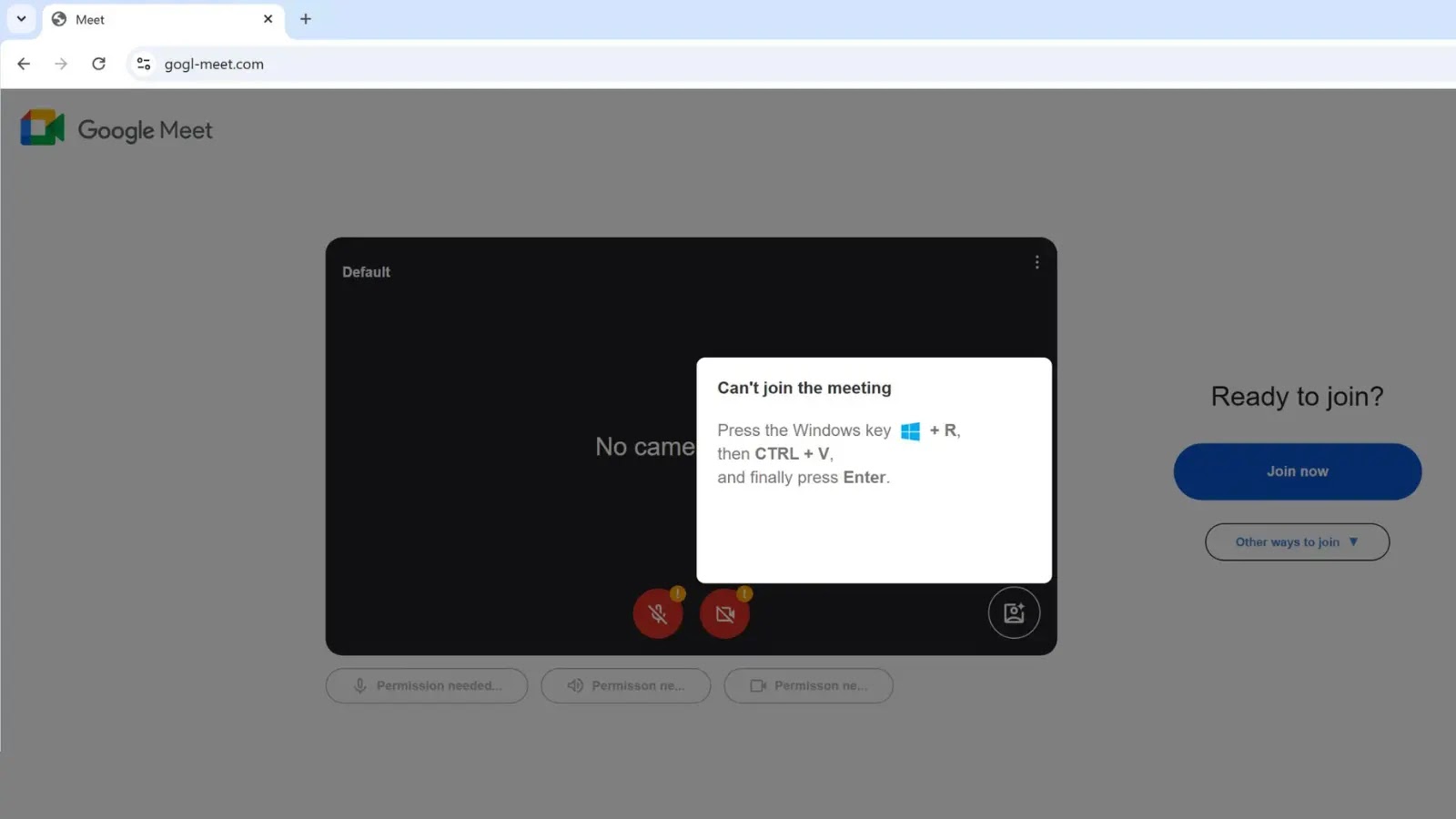
The malware begins its assault by way of a two-stage an infection course of. A dropper software tips customers into putting in the precise payload by masquerading as a authentic app, typically mimicking trusted companies.
This strategy allows DroidLock to bypass Android safety restrictions and entry essential accessibility companies.
As soon as put in, the malware requests each system administrator and accessibility permissions, which victims typically grant with out understanding the implications.
Zimperium safety researchers recognized DroidLock’s refined structure throughout their investigation.
Dropper installs the second stage (Supply – Zimperium)
The malware makes use of each HTTP and WebSocket to speak with its command-and-control server, enabling attackers to ship directions and obtain stolen information constantly.
Requesting accessibility companies to carry out fraud (Supply – Zimperium)
This bidirectional communication allows real-time management over compromised units.
Understanding DroidLock’s Credential-Stealing Mechanism
DroidLock employs two distinct overlay strategies to steal consumer credentials and unlock patterns.
The primary methodology makes use of a pattern-drawing interface embedded straight within the malware’s code that seems instantly when customers attempt to unlock their units or entry banking purposes.
This overlay captures unlock patterns with out alerting customers to the theft. The second strategy entails HTML-based overlays loaded dynamically from a database on the attacker’s server.
These overlays completely mimic authentic banking apps and login screens, tricking customers into getting into credentials straight into pretend types.
When customers work together with these overlays, all entered data flows on to the attacker’s infrastructure.
The malware screens when customers open particular purposes and matches them in opposition to a server-provided record.
If a match happens, DroidLock instantly deploys the corresponding overlay. This clever concentrating on ensures attackers deal with high-value purposes like banking and fee methods.
Queries injections from the database (Supply – Zimperium)
Past credential theft, DroidLock data display screen exercise and captures pictures utilizing the system digital camera, probably exposing delicate data displayed on the display screen, together with one-time passwords and authentication codes.
DroidLock’s ransom display screen threatens to destroy all information inside 24 hours and calls for fee through the offered contact particulars.
Ransomware type overly and admin contact particulars (Supply – Zimperium)
Not like conventional file-encrypting ransomware, this malware doesn’t have to encrypt information as a result of it could possibly merely erase the whole lot utilizing manufacturing facility reset instructions.
This makes prevention and detection essential, as restoration after an infection turns into practically not possible with out knowledgeable help.
Observe us on Google Information, LinkedIn, and X to Get Extra On the spot Updates, Set CSN as a Most popular Supply in Google.