A crucial vulnerability in Streamlit, the favored open-source framework for constructing information purposes, permits attackers to conduct cloud account takeover assaults.
The flaw, found in February 2025, exploits weaknesses in Streamlit’s st.file_uploader element to bypass file sort restrictions and achieve unauthorized entry to cloud situations operating Streamlit purposes.
The vulnerability demonstrates how seemingly minor elements can create important safety dangers, significantly when deployed in misconfigured cloud environments.
Key Takeaways1. Extreme Streamlit bug enabling cloud account takeovers and monetary information tampering.2. Attackers may add malicious information and achieve unauthorized entry.3. Streamlit patched the difficulty.
Streamlit Vulnerability – Account Takeover Assaults
The vulnerability originates from improper file sort enforcement in Streamlit’s file add widget, the place restrictions had been solely utilized client-side via JavaScript with out server-side validation.
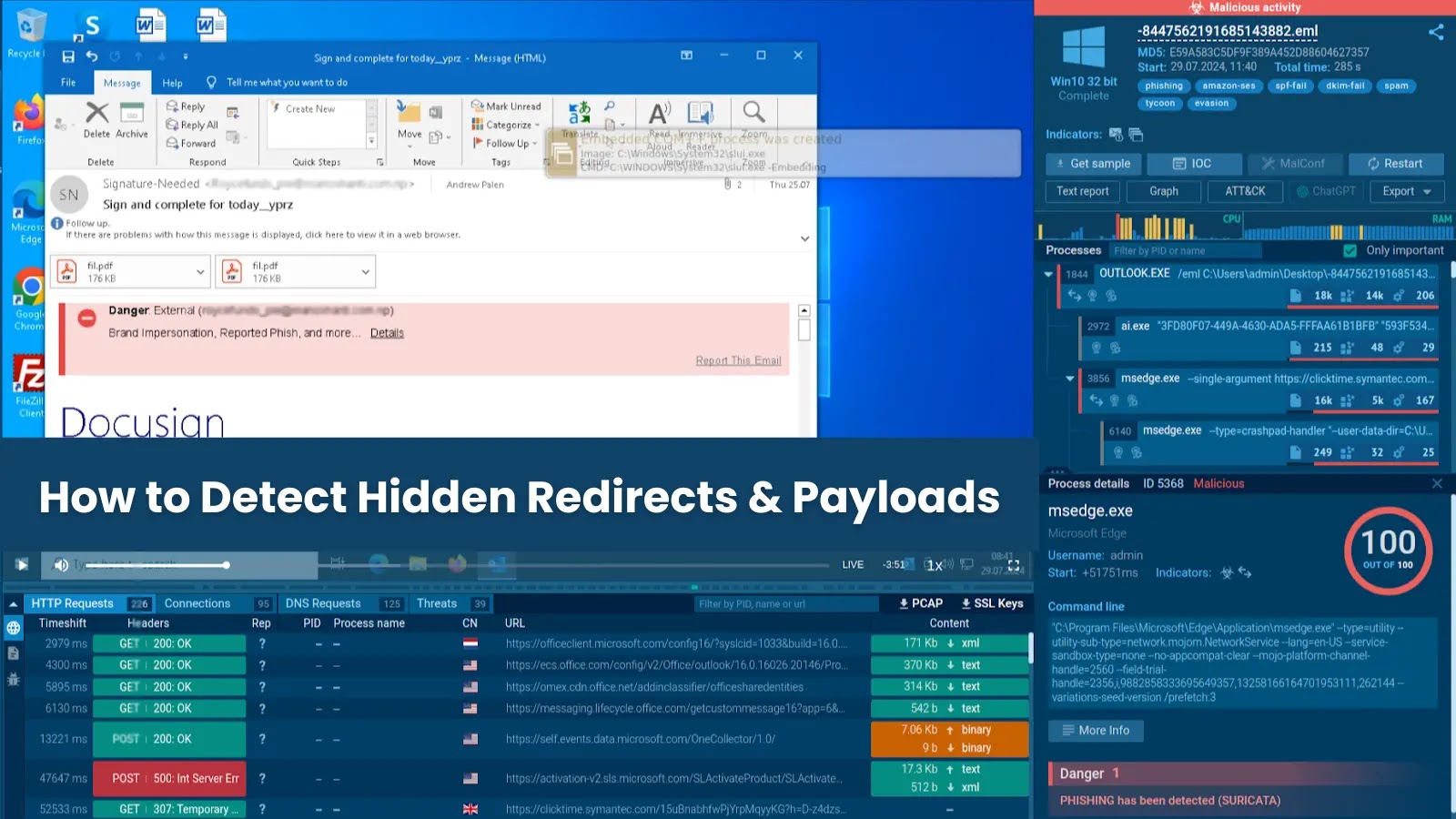
Safety researchers demonstrated how attackers may use proxy instruments like Burp Suite to intercept add requests and bypass frontend restrictions by modifying file extensions throughout transit.
The assault chain entails importing malicious information disguised as official ones, equivalent to renaming malicious.exe to seem as a PDF file.
Of their proof-of-concept demonstration, researchers confirmed how this might escalate to listing traversal assaults, the place risk actors modify uploaded filenames to ../../.ssh/authorized_keys and overwrite crucial system information with their SSH public keys.
This method grants passwordless distant entry to compromised cloud situations operating Streamlit purposes.
The technical exploitation follows a scientific strategy: reconnaissance of publicly accessible Streamlit situations, request interception to change file extensions and paths, authorized_keys file overwriting, SSH entry institution, cloud setting enumeration, and at last information pipeline manipulation.
The implications for monetary establishments are significantly alarming, as Streamlit has change into a go-to framework for constructing inventory market dashboards, machine studying prototypes, and real-time monetary information visualizations.
Cato Networks’ researchers revealed how compromised situations may manipulate ingestion of pipeline scripts, database values, and dashboard code, doubtlessly resulting in undetected market manipulation.
Such assaults may set off cascading results the place automated buying and selling methods reply to false alerts, media sentiment shifts primarily based on manipulated information, and traders observe fraudulent tendencies.
The researchers famous that “inventory market dashboards might drive automated alerts, danger fashions, and inside technique choices, which means the manipulation may set off a series response of portfolio changes”.
Streamlit acknowledged the vulnerability and launched a patch in 1.43.2, introducing backend validation to implement file-type restrictions.
Cato Networks has up to date its SASE Cloud Platform with enhanced risk prevention capabilities focusing on unauthorized file add bypass makes an attempt and irregular filename path detection.
Organizations are urged to make sure that cloud situations internet hosting net purposes implement correct community restrictions and entry controls.
Combine ANY.RUN TI Lookup along with your SIEM or SOAR To Analyses Superior Threats -> Strive 50 Free Trial Searches